
rvlsoft - Fotolia
As network security analysis proves invaluable, NDR market shifts
IT infrastructure threat detection and response have emerged as critical elements of enterprise cybersecurity as network security analysis proves invaluable to protecting data.
The market for network detection and response tools is gaining steam as they prove effective against the latest and most challenging cybersecurity threats. While some may scoff at the idea of incorporating yet another security tool, NDR is not only incredibly accurate in identifying hard-to-discover threats, but it's also poised to bolster weaknesses in current security technologies being used by the enterprise.
The evolution of NDR
Much of the technology behind most NDR platforms can be traced to network traffic analysis -- and eventually to AI for IT operations (AIOps) platforms. These tools focus on network performance by collecting flow and packet capture data taken from specific parts of the corporate network. Once collected, this data is then analyzed to identify difficult-to-find network performance issues, such as overutilization, intermittent hardware or software failures, and IT misconfigurations. These tools have proven to be a tremendous timesaver because AI is used in both the identification and remediation of network performance problems.
What sets AIOps platforms apart from more traditional network performance monitoring tools is the fact that packet capture data is the focus, as opposed to logs, traps and other alerts generated from the network hardware and software itself. By using packet capture data, a baseline that indicates normal network performance behavior can be built. Then, when performance issues occur, the analyzed data will show changes in traffic behavior, as well as why the problem started, where the root cause is and even information about how to remediate the problem.
Security vendors took a close look at the power of AIOps from a packet capture data collection perspective, as well as incorporating AI to automate the root cause analysis and remediation steps. What they found was that the same data collection, analysis and remediation model used for AIOps purposes could also be used as an incredibly powerful cybersecurity tool. Just like with AIOps, an NDR platform collects and baselines all network behavior. But, instead of focusing on network performance analysis, the focus would instead shift to network security analysis to identify suspicious traffic behaviors.
How emerging threats now require the use of NDR
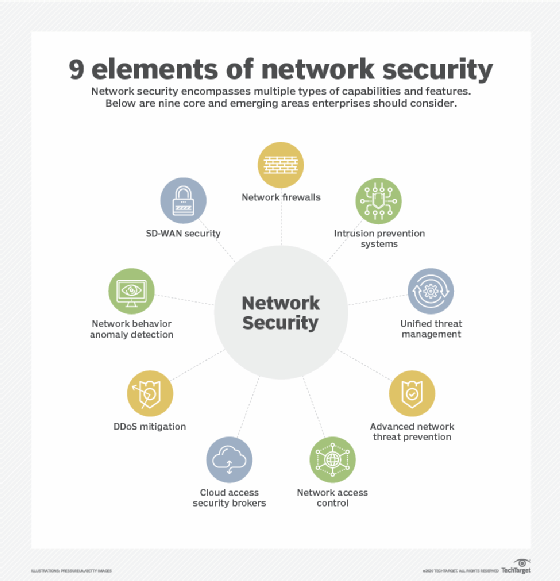
The reason why packet capture data is so appealing is because emerging threats are designed to evade security tools traditionally used to identify suspicious behaviors that indicate an infrastructure compromise or breach. These include technologies such as network/firewall and server logs, endpoint detection and response (EDR) software, and traditional security tools, like intrusion prevention systems and SIEM systems that centralize security visibility. The problem with these detection mechanisms is the fact that attackers are becoming increasingly proficient at evading or disabling these types of tools. Bad actors understand that enterprise-grade systems will have logging enabled, as well as EDR software installed. Thus, they will seek to bypass one or more of these security mechanisms when making their initial compromise on a system. Once inside, they have far more flexibility, as most security tools focus on external threats as opposed to internal.
The use of NDR, on the other hand, cannot be easily evaded. In fact, attackers will likely have no idea an NDR is observing their activities as this type of network security analysis and monitoring is completely passive. Additionally, some of the more extensive NDR platforms on the market enable the decryption of encrypted packets to achieve complete network visibility so attackers cannot obscure their threats. The other difference is that NDR monitors all traffic, so compromised internal devices are more likely to be detected soon after their network traffic behavior changes.
It also cannot be understated that the greatest source of truth on any corporate infrastructure is the raw packets that flow from one device to the other. This is another reason why NDR platforms are becoming so popular among network security professionals. Beyond detecting and remediating threats, NDR tools can collect and store full packet capture data. This packet data is critically important for digital forensics purposes. An NDR platform eliminates the need for collecting packet capture data through other methods. Thus, this is simply one less forensic task a security team needs to concern itself with.
The business case for NDR
As mentioned previously, NDR evolved out of AIOps platforms that are mostly used by network operations support staff. While some NDR vendors have removed much of the network performance analytics capabilities in favor of strictly focusing on network security analysis, other vendors have combined both AIOps and NDR into a single, unified tool. Thus, network performance analytics and network security analytics can share the use of NDR for different purposes.
Additionally, NDR platforms can generally be deployed across any network architecture, including private networks and data centers, public clouds and hybrid environments. Because both AIOps and NDR tools are expensive investments, the opportunity to consolidate two platforms into one is a highly appealing cost-saving opportunity.
Without an NDR tool deployed across your corporate network, the potential for undetected compromises and breaches is a continuing risk. The business case for an NDR platform is simple: The evolution of attack methods justifies the use of cybersecurity detection platforms that cannot be bypassed by nefarious actors. Additionally, the opportunity for cross-team collaborative use from an AIOps perspective can also help to maintain a healthy network, while saving tremendous costs through tool consolidation.








