What is a micro VM (micro virtual machine)?
A micro VM (micro virtual machine) is a virtual machine program that serves to isolate an untrusted computing operation from a computer's host operating system.
The goals of a micro VM are to stop malware at the endpoint, increase cybersecurity and boost resilience through virtualization -- all without affecting the end user.
An alternative to software sandboxing, micro VMs rely on hardware isolation to prevent infection from untrustworthy, often user-initiated tasks, such as web browsing or document/media downloading. The concept was pioneered by security startup vendor Bromium, which released its first micro VM product in 2012. Cloud vendor Amazon Web Services (AWS) released the open source Firecracker micro VM in 2018.
In a microvirtualization environment, enterprises set up policies to identify trusted processes. Any computer process deemed untrusted, such as opening a file or downloading a webpage, is automatically placed in a micro VM. This way, malware or other malicious code executing in the isolated micro VM instance is not able to compromise the rest of the system.
At any given time, a computer can run dozens or hundreds of micro VMs. Because they are generated for user-initiated tasks, micro VMs must be created instantaneously. To prevent latency and bottlenecks, micro VMs were designed to only access a minimal set of operating system (OS) resources. They cannot interact with any other processes.
Containers vs. VMs vs. micro VMs
A micro VM provides VM isolation for each instance with containerlike architecture. Ideally, this setup enables admins to deploy a large number of micro VMs quickly and efficiently, while ensuring the logical isolation and security of each instance. Standard VMs and containers each have their own drawbacks. When IT organizations use VM and container technology in combination, they offset those disadvantages and boost the benefits.
VMs
VMs provide isolation but consume large amounts of resources. VMs run on a hypervisor and provide exceptional logical isolation. VMs don't share each other's memory space and aren't aware of the presence of other VMs on a host server. Each VM can support its own guest OS, enabling a virtualized server to run many different OS types and versions.
Due to this isolation and completeness, VMs can be large, resource-intensive virtual constructs that take several minutes to deploy. A server often hosts only a handful of VMs. Each VM needs its own OS. This can result in unnecessary duplication of resources. For example, 10 VMs running Windows Server workloads need 10 Windows Server licenses. So, VMs can be costly to deploy.
Containers
Containers are small by comparison to VMs, with a shared OS. Containers run atop a container engine, such as Docker, and require relatively few compute resources. In general, dozens or hundreds of containers can deploy in a matter of seconds and coexist on the same server that might fit only a handful of VMs.
A big part of this efficiency is the use of a common OS. Every container shares the same OS kernel, which is usually a version of Linux. Containers include all the dependencies needed to operate, enabling a container to easily deploy across many host systems. However, the common OS poses potential security and stability risks. Any security or functional flaw in the OS can potentially affect all the containers running on it. This lack of complete isolation makes containers more susceptible to malicious attacks than VMs, though both carry security risks.
Micro VMs
Micro VMs promise the best of both worlds: isolation and security. A micro VM environment starts with standard server hardware and runs a host OS, such as Linux, to supply the kernel-based VM (KVM) needed for micro VMs. A micro VM engine, such as Firecracker, runs atop the OS, acting as the hypervisor -- or engine -- that supplies an application programming interface (API), network, storage and management tools needed to operate each micro VM.
Once running, the micro VM engine creates completely isolated virtual instances that can run a guest OS and a container-type workload. The instances are small and isolated, and admins can quickly create them in large volumes.
Micro VM products
Bromium, part of HP Wolf Pro Security. Bromium was acquired by HP in September 2019 and is now part of HP Wolf Security. The Bromium micro VM technology is integrated into HP Wolf Pro Security for PCs as "advanced threat isolation." Files, applications and webpages are contained inside micro VMs. Bromium is the basis for HP's Sure Click security tool.
AWS Firecracker. AWS Firecracker is a specialized VM monitor. AWS developed Firecracker to create and manage micro VMs.
AWS originally developed the Firecracker platform to support micro VMs in container- and function-based services, such as AWS Lambda and AWS Fargate. Open source Firecracker is available under Apache License version 2.0 through Git.
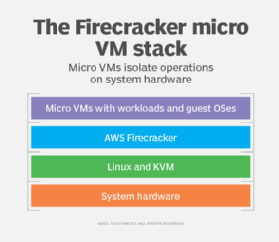
Firecracker runs as an additional layer atop KVM. Firecracker includes only essential functionality, such as the API, network and storage capabilities, rate limiting and metadata services. This simplicity enables quick startups, micro VM security and compact size so multiple micro VMs can exist at once without taxing system resources.
The Firecracker API allows basic actions, including starting/stopping a micro VM, provisioning virtual central processing units and sharing metadata. Rate limiters restrict network and storage use, enabling multiple micro VM instances to operate simultaneously on shared infrastructure.
Firecracker is compatible with the following container and serverless platforms:
- appfleet
- containerd
- Fly.io
- Kata Containers
- Koyeb
- OpenNebula
- Qovery
- UniK
- Weave Firekube
How are micro VMs used in Windows?
Microsoft Windows is an endpoint OS. Windows 10 is the most commonly used version, and Microsoft released Windows 11 in 2021. Endpoint computers have fewer compute, memory and storage resources than enterprise servers, so creating multiple VMs with different OSes and other operating elements for the purposes of isolation can exhaust available resources.
Micro VMs can be used for security on endpoint systems. Micro VMs protect the endpoint when the user opens a website, downloads a document with macros in it or runs an application.
In 2015, Bromium and Microsoft announced a partnership to support Bromium's micro VM technology as a security mechanism for Windows 10. HP Sure Click is supported for Windows 10. HP also has a roadmap of support for Sure Click and Windows 11.





