soft token
What is a soft token?
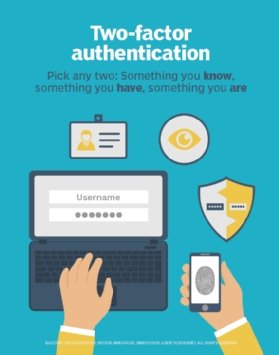
A soft token is a software-based security token that generates a single-use login personal identification number (PIN). Traditionally, a security token was a hardware device, such as a key fob or USB token, that produces a new, secure and unique PIN for each use and displays it on a built-in liquid crystal display (LCD). The system activates after the user presses a button or enters an initial PIN.
Security tokens are generally used in environments with higher security requirements as part of a multifactor authentication (MFA) system. While the hardware tokens are more secure than soft tokens, they are also costly and difficult to deploy on a large scale, as might be required for online banking.
Soft tokens, also known as software tokens, are an attempt to replicate the security advantages of MFA, while simplifying distribution and lowering costs. Soft tokens exist on common devices, such as a smartphone with a soft token app that performs the same task as a hardware security token. The smartphone provides an easy-to-protect and easy-to-remember location for secure login information. Unlike a hardware token, smartphones are wirelessly connected devices, which can make them less secure. Just how secure they are depends on the device's operating system and client software.
When using a soft token system, an end user logging into a financial investment company's user portal is required to enter a username and a password. Then, the system sends a one-time password (OTP) to a phone number or email address associated with that user's account. The user enters the OTP in the field indicated in the security login screen to get access to the portal.
Why are soft tokens important?
Soft tokens play a vital role in cybersecurity. providing a software-based authentication method that enhances security, improves convenience and reduces costs.
- Security. Soft tokens ensure that access to systems is protected by at least two-factor authentication. They protect against unauthorized access and identity theft, providing an extra layer of security that protects the confidentiality, integrity and availability of information.
- Convenience. Soft tokens can be easily deployed to users' mobile devices, making them a flexible and efficient security technique.
- Cost-effective. Soft tokens cost less to deploy than hardware tokens because they eliminate the need for physical devices and can be easily distributed to users. They are easier to scale when organizations grow in size or their security needs increase.
Who uses soft tokens?
Soft tokens are used by individuals and organizations to enhance cybersecurity by providing an additional layer of authentication. Soft tokens are commonly used to provide secure remote access, as well as in virtual private networks and cloud applications.
Industries that deal with confidential personal data, such as healthcare, financial institutions and government agencies, are among the top adopters of soft tokens. Soft tokens are accessible and convenient, making them ideal for deployment to a range of users and applications.
Both hard and soft tokens can effectively manage authentication and access control. The key is to use a technology that is consistent with the organization's security strategy and requirements.
Hard tokens vs. soft tokens
Hard and soft tokens can be used to achieve the same goal, but there are some differences in how they go about it.
Hard tokens
Hard tokens predate soft tokens and are still in use, though far less than a few decades ago when they were common. A popular hard token is the RSA SecurID, a thumb-sized device with an LCD for token PINs. An algorithm in the device changes the six-character display at preset intervals. During a login process that uses a hard token, the user initiates a system login, enters an ID and password, followed by the number displayed on the token.
There are some circumstances where a hard token is required. For instance, if biometric authentication is used, a physical token that can take a thumb or eye scan is needed. In MFA, if one or both initial authentication factors are disabled or compromised, a hard token option might be used as backup.
However, hard tokens can be costly and more challenging to manage compared to soft tokens. They also can be lost, misplaced or stolen.

Soft tokens
Users logging into a soft token-based application follow much the same process as with a hard token. They enter their ID and password, and then must enter an OTP sent to their phone or email to complete the authentication process.
The security technology in a system generates a one-time passcode or password that's entered to complete the authentication process. New tokens are created for each access request, making them quite secure.
Soft tokens are less expensive to use than hard ones because they carry little or no overhead. They also don't have a physical implementation so they can't be lost or stolen.
Learn about the six different types of authentication.








