
Amid explosive growth, API security a growing concern
APIs are expanding exponentially across the technology landscape and creating a vast attack surface that enterprise security teams are struggling to understand and defend.
The explosion of APIs is creating a pace that's almost impossible to keep up with, and increasingly harder to secure.
While APIs are not inherently insecure, the massive volume deployed across the technology landscape has created challenges for enterprise security teams. A rapid digital transformation over the last five years contributed to those challenges, with APIs expanding to cloud services, microservices and mobile apps.
These emerging APIs are not always designed or deployed with security in mind, leading to a lack of proper authentication, authorization and possible exposure of sensitive data such as personally identifiable information (PII). As everything about API security changes, teams are scrambling to keep up with the amount and struggling to understand how many APIs are in an environment.
The onset of COVID-19 contributed to the growth, according to a Google report titled "A State of the API Economy 2021." Businesses responded to the pandemic by accelerating digital transformations as they transitioned to remote work.
The report found that out of the 700 IT executives surveyed, nearly three in four organizations continued their digital transformation investments. APIs played a primary role, particularly as the "backbone of digital business ecosystems."
The transformation also extended to artificial intelligence and machine learning-powered API security, which Google said is "gaining widespread adoption to help companies detect and block malicious attacks." The report also cited weaknesses such as the potential for exposure to external individuals and organizations, putting corporate and customer data at risk.
Infosec companies, especially startups in the newer API security market, are taking note. Karl Mattson, CISO of API security vendor NoName Security, referred to the pace of change and accelerated utilization as "explosive." Similarly, Salt Security CEO Roey Eliyahu said over the last few years the amount has grown from every company having a few APIs to thousands of them.
The visibility challenge
While enterprise security teams typically know when developers are creating a web application, the velocity at which APIs emerge is taxing. Idan Plotnik, CEO of application security startup Apiiro, said because so many new APIs are being developed daily, it becomes much more likely that a mistake, security issue or exploitable design issue will be created along with those APIs.
The rate of emergence is so rapid that Sandy Carielli, principal analyst at Forrester, said it's easy to lose track. One of the biggest issues that Forrester customers face with respect to APIs is the inventory. "They don't know what they have. And it's very easy to have legacy APIs that are perhaps sitting out there," Carielli said.
Lack of visibility affects all companies, no matter the size. Carielli said most organizations don't have a full view of its APIs. Plotnik agreed; whether it's company with 100 developers, or a large enterprise with 15,000 developers, Plotnik said they don't know how many APIs they have.
"All the API security solutions out there can map how many APIs they have that are exposed to the internet, but internally the source code in the code base, they don't know how many because they have a lot of APIs that are internal facing but still have a wide attack surface," Plotnik said.
If companies don't know what APIs are out there, then they don't know what data they could be pulling in and they don't know who has access to them, and the potential for data leakage is much greater, particularly because APIs were created with a format, such as Rest APIs, that makes it relatively easy for customers to pass data back and forth, Carielli said.
"If we're not careful about it, if we're not applying the same security principles in terms of access control authorization, in terms of authentication, in terms of data leakage -- things that we've looked at for years with traditional applications. If we don't apply those to APIs, we get the problems that we've seen," Carielli said.
API vulnerabilities under the radar
As it becomes more common for APIs to interact with cloud and microservices on top of mobile apps, external applications and the internet of things, the potential risks increase. Mattson cited the use of APIs "increasing and diversifying exponentially" into those two areas as a primary challenge of security.
"It's extremely hard for an IT organization or for a security organization to keep up, even just to have a basic map of the state of the state. There's so much complexity, so much diversity and quantity of APIs and it's a moving target," Mattson said.
For example, in August, Rapid7 researcher Arvind Vishwakarma uncovered multiple vulnerabilities in the Fortress S03 WiFi Home Security System. According to the blog post, CVE-2021-38276 could allow unauthenticated API access. Vishwakarma referred it to as an "insecure cloud API deployment which allows unauthenticated users to trivially learn a secret that can then be used to alter the system's functionality remotely."
Dror Arie, cloud solutions engineer at GlobalDots, discovered another cloud vulnerability that exposed the COVID-19 vaccination status of all Israeli citizens. While filling out a COVID declaration form on the Israel Ministry website using his cell phone, he found that the API endpoint was off and that all he needed in order to know someone's vaccine status was their ID number. To make matters worse, those IDs reveal more than just vaccination statuses.
"In Israel, ID numbers are considered a very weak and hardly private PII: Unlike social security numbers, you use your ID almost everywhere -- including payment providers, point of sale, etc.," Arie wrote in the GlobalDots report.
API vulnerabilities are even more dangerous due to lack of proper tools. One of the biggest struggles of securing APIs, according to Carielli, is the absence of a single tool that can be dropped into an environment. Therefore, searching for flaws and evaluating the security of an API environment requires additional resources and effort.
"It is more of a multi-faceted approach which involves looking at all your existing applications, security tooling and asking your team and maybe asking vendors, 'Does this support APIs?'" she said.
Securing APIs in runtime protection is the biggest challenge Eliyahu has uncovered, which he credits to increasing attack sophistication and uniqueness. The categorization of the Common Vulnerabilities and Exposures (CVE) system also poses issues. According to Eliyahu, a CVE is typically for components that are being shared across companies, and a lot of APIs use passive code.
In addition, some API vulnerabilities are created because of a specific design choice or misconfigurations, which are often not assigned CVEs.
"It's a vulnerability that someone -- a developer at Zoom or the bank, or SaaS company -- just created by introducing a code change, and the ability to learn this unique behavior when there is no one standard, I think, is the biggest challenge," Eliyahu said.
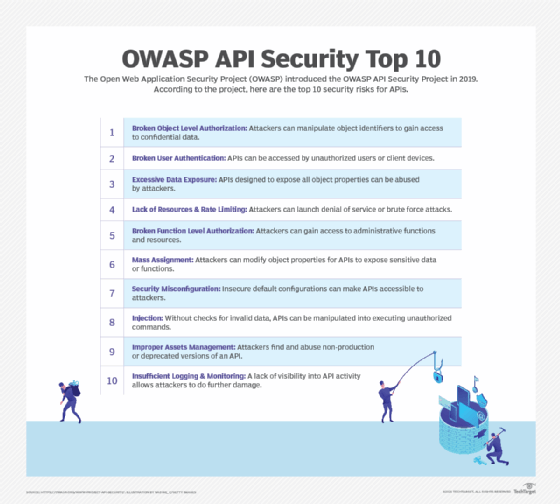
However, progress has been made. In 2019, the Open Web Application Security Project (OWASP) created a category which captures and classifies the type of API vulnerabilities, including a top 10 list. Carielli cited it as a recent example of the investment that's been made in understanding the type of flaws that impact APIs.
Looking at the OWASP top 10 list, Patrick Sullivan, CTO of security strategy at Akamai, highlighted one vulnerability in particular -- a lack of rate limiting for APIs, which he said has been done for web applications for 20 years. Compared to web applications, Sullivan said there's less maturity in the security practices for APIs, which outweighs any defects in the CVE method.
Looming threats
According to Sullivan, the biggest struggle for API security lies with the building blocks of authentication. This has grown in importance with APIs' increased access to critical data. Over the past six years, Eliyahu observed APIs emerge as one of the most critical attack vectors.
"I saw new challenges like the fact that APIs suddenly accessed critical data and the fact that they are now changing all the time because of agile development. They used to change maybe every six to 12 months," he said.
Having knowledge of the attack surface is step number one in API security, according to Eliyahu.
That attack surface has been increasingly targeted by threat actors over the last five years or so, according to infosec experts. A 2019 study by Gartner said, "by 2021, 90% of web enabled applications area for attack in the form of exposed APIs rather than UI, up from 40% in 2019."
Sullivan believes attackers are more focused on APIs than defenders, though improvements in API security have been made over the years. "I think the good news is defenders are paying more attention to API security in 2021 than they were in 2016. It was not a major focus there," Sullivan said.
Prior to the uptick in attacks, Eliyahu saw firsthand how vulnerable APIs were and observed a few incidents in the market, including a Turbo Tax vulnerability and a Facebook API bug that exposed millions of users' photos.
Another example of a high-profile API attack was one against Imperva in 2018, which resulted in a data breach. An exposed AWS API key was obtained by attackers and then used to access customer data. More recently, Twitter disclosed an attack that involved the exploitation of its API endpoint and enabled threat actors to match usernames to phone numbers.
Eliyahu attributes the accelerated digital transformation, which started taking off in 2015, as a key reason for the increase in attacks. "I realized that these products were not designed to how APIs are being developed and exposed today," he said.
While awareness is improving, Carielli predicts there will not be a leveling of attacks anytime soon.
Strengthening API security
Experts say further effort and prioritization is needed to secure APIs. One area that requires a level of maturation is communication, which Sullivan said is absent in many organizations. That counts for all stages of development. According to Akamai's "The State of the Internet" report regarding APIs, development needs to, one some levels, include various stakeholders. That includes development teams, network and security operation teams, legal compliance teams and more.
Mattson agreed that a major challenge today with API security is a lack of communication among stakeholders.
"They each have a different sheet of music -- what inventory is even in use, how they are configured, whether there is risk exposure, what activity is actually happening in runtime," he said. "So, when each stakeholder is presented with a sort of different view of the world, it's sort of necessary that they're going to come to different conclusions about what priorities to make and what conclusions to come to."
Carielli said there's an opportunity to create a positive security model because APIs can have specification files, but it requires effective communication between security and development teams to ensure the files are generated and kept up to date.
"If you're looking at API calls and you're only accepting calls in the format that was defined by your API specification file, then you can actually create a positive security model with these, which is also what you can do with traditional applications. It really is a matter of: Are you going to do the right things? If not, they're no riskier than traditional apps. The difference is we just haven't gotten there," she said.
Similarly, Sullivan said the best-case scenario in the fast-paced world of emerging APIs is having security teams use a traditional model, which means communicating when an API is created then follow-up with security protocols. However, he believes that approach is far too slow today.
"I think security really needs to think about enabling that development team, providing guardrails so you know, knock yourself out, you're going to create 1,000 APIs this week," Sullivan said. "We have these checkpoints and we're discovering APIs. We can still ensure safety."







