CCISO exam guide authors discuss the changing CISO role
Learn more about EC-Council's Certified CISO exam and how the certification helps CISOs at any organization manage successful infosec programs and a changing threat landscape.
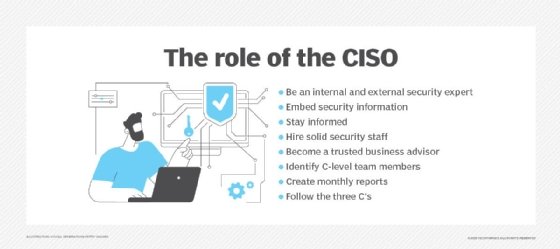
The CISO role has seen enormous fluctuation since its inception. Historically, it was considered an advisory position. Today, as the threat landscape and compliance initiatives have intensified, organizations have begun to take cybersecurity and its critical leadership more seriously.
CISO responsibilities vary based on an organization's industry, budget, security priorities and other attributes. But what defines the CISO position is its entanglement of technical comprehension with managerial and business understanding. To reinforce necessary technology and strategy knowledge, EC-Council designed the Certified Chief Information Security Officer (CCISO) program for experienced security leaders and CISOs.
"Other security certifications focus a great deal on technical domains and implementation details," said Steven Bennett, co-author of CCISO Certified Chief Information Security Officer All-In-One Exam Guide, published by McGraw Hill. "But what makes the CCISO special is that it addresses leadership and management skills every C-level executive should have, whether they're CISO, CIO or CFO."
Here, Bennett and co-author Jordan Genung opine on the changing role of the CISO, the benefits of CCISO accreditation and why a career in security leadership is so rewarding.
Editor's note: This transcript has been edited for length and clarity.
 Click to learn more about
Click to learn more about
CCISO Certified Chief
Information Security
Officer All-In-One Exam
Guide by Steven Bennet
and Jordan Genung.
More on CCISO Certified Chief Information Security Officer All-In-One Exam Guide
For a comprehensive security program management explainer -- including practice CCISO exam questions -- check out an excerpt of Chapter 3 from CCISO Certified Chief Information Security Officer All-In-One Exam Guide, published by McGraw Hill.
How do individuals and their employers benefit from the CCISO certification?
Steven Bennett: The CISO is the highest-level security executive in many organizations. While companies know they need a CISO, they often don't know what the CISO necessary looks like. Those in a technology-oriented field might have a good idea, but a food manufacturer or business in the services industry may not understand the role of a CISO.
The CCISO certification provides guidance for employers. If they hire a certified CISO, they have a reasonable expectation that the person has at least the basic skills needed for the role. The individual benefits because it provides an independent attestation that the person has the essential skills of a CISO so they can present that to a potential employer.
Jordan Genung: What is unique about the CCISO certification is that it doesn't just cover security and compliance domains. It also covers leadership domains that are important for a CISO to understand, including strategic planning and finance. Many other security certifications do not touch on these.
What prior experience is needed for the CCISO exam?
Genung: Success on the CCISO exam will depend on the candidate's background. Someone with a strong technical background may struggle with the leadership and financial topics, whereas someone with a business or compliance background may struggle with the more technical topics in the Security Core Competencies domain.
Bennett: Experience is everything. The CCISO is not an entry-level certification by any stretch. This is a certification for people who have worked for at least five years in the industry. The certification is deeply rooted in the person's experience with security and at the corporate level.
An excerpt of Chapter 3, 'Security Program Management and Operations,' is available on SearchSecurity. What challenges should CISOs anticipate with respect to security program management?
Bennett: One of the biggest challenges is getting buy-in from the top. Security is not necessarily directly tied to an organization's business or bottom line. In some organizations, it can be considered an outlier. That's a challenge. The best CISOs can demonstrate the value of maintaining good security to the business.
Genung: The challenge that everyone faces is having appropriate resources, whether it's funding or staffing. To handle the challenge of buy-in from business leaders, CISOs need to understand business goals and how to translate them into security decisions, including how and where to prioritize resources.
What are some of the broader security trends CISOs need to keep top of mind in 2021?
Bennett: The biggest problem in security is not the technology; it's the people. We have the technology and tools to help most security issues, but people are the weakest link in in cybersecurity. People make mistakes and fall victim to social engineering attacks all too often. Finding ways to ensure people are aware of good security hygiene practices is the key to human-based vulnerability management -- that's an emerging trend that will be very important in the years ahead.
Genung: CISOs should be able to adapt to the changing landscape to allow business innovation, while ensuring there are appropriate security controls in place. One of the significant trends today is the expansion of remote telework as a result of COVID-19. Organizations have more remote workers than ever, which is why human-based vulnerability management is so important. CISOs must be able to adapt to these ever-changing times and achieve business goals, while not compromising security.
What does human-based vulnerability management entail?
Bennett: We manage vulnerabilities in hardware and software by doing asset inventories and asset tracking. Making it human-based is the concept of extending vulnerability management beyond hardware and software assets to treat people as assets, too. We need to manage vulnerabilities associated with people and users as much as we do for hardware and software assets.
What are some common misunderstandings about the CISO role?
Bennett: One major misunderstanding I hear is that the CISO must report to the CEO and that it's not going to work if the CISO reports to the CFO or the CIO. But I don't hear that from CISOs. The best CISOs figure out how to be successful no matter who they report to. It's up to the CISO -- wherever they are on the organizational chart -- to figure out how best to communicate the proper security vision and figure out how best to have an impact on that organization.
Genung: I agree. The other misunderstanding is that the CISO is a one-size-fits-all role. CISO roles and responsibilities vary from organization to organization. Some organizations may have heavier compliance requirements, [and] so may need a CISO with a strong compliance background. A software development company, on the other hand, may need the CISO to have a strong background in secure software development.
How would you each respond to the argument that certifying CISOs is unnecessary because there's no one-size-fits-all CISO?
Bennett: There is no one-size-fits-all CISO, but there are core capabilities. For example, every CISO should know about the CIA [confidentiality, integrity and availability] triad, as well as how security controls are selected and implemented. Most importantly, every CISO should know that the right security approach will be tailored to the organization's business. Depending on the business and the CISO's background, implementation details will vary considerably, but there's a core skill set that applies to every CISO. That's what the CCISO certification is designed to address.
Genung: The benefit of the CCISO exam is that it fills in any gaps in the CISO's background experience. For example, if a CISO came up through a business or compliance route, they may have a knowledge gap in security core competencies. Alternatively, if they came up through a technical route, the certification process is an opportunity to learn more about strategic planning or finance. The certification will help them become a well-rounded leader.
What kind of soft skills do the best CISOs have?
Bennett: As a C-level role, the CISO is a high-level manager in the organization with many people working for them, so leadership skills are important. Communication skills are important as well -- not just the ability to express your view, but also the ability to listen to and negotiate with employees and other leaders throughout the organization. The security team has to be able to change and adapt to the threat landscape, the marketing landscape and the business landscape. Thus, the CISO's ability to manage change is very important.
Genung: The one that comes to mind is humility. The CISO is not always going to be an expert in every single security domain, so they need to rely on and take advice from their team members. Empathy is another important skill, not only for your security staff, but also for the general employees of the organization. This skill can help translate into the security awareness program strategy. I personally value a sense of humor in a CISO as well, but that might be just me.
How have your careers as information security leaders been rewarding?
Bennet: My career in infosec has provided the opportunity to make great friends and build relationships with peers -- and earn good pay. It provides a vehicle for me to express myself creatively and to have a positive impact on an organization by helping them implement good security.
Genung: I agree with all those items. The security landscape is always evolving, so there's always a new challenge and something new to learn. The opportunity to build relationships with great people like Steve and our technical editor, Mike, has been rewarding.
 Steven Bennett
Steven Bennett
About the authors
Steven Bennett, CCISO, CISSP, CISA, is an engineer, sportsman, entrepreneur and consultant. He has worked in the IT field for more than 40 years, helping organizations protect their most important assets from criminal threats. Bennett has spent his lifetime studying human and animal behavior in complex systems, relationships between predator and prey, and offensive and defensive survival strategies and tactics observed in business and nature. His information security consulting career includes supporting clients in healthcare, manufacturing, retail, finance, military and government.
 Jordan Genung
Jordan Genung
Jordan Genung, CCISO, CISSP, CISM, CISA, has served as an information security officer and security advisor for public and private sector organizations. His experience includes security consulting for Fortune 100 companies and government agencies, building information security programs and developing information security curriculum. Genung holds a degree in computer science and information security from the University of Texas at San Antonio, which is a National Security Agency and Department of Homeland Security National Center of Academic Excellence in Cyber Operations, Cyber Defense and Research.








