The ins and outs of cyber insurance coverage
Cyber insurance coverage can help companies successfully navigate the aftereffects of a data breach. However, choosing a policy in the first place can be confusing.
For many companies, it's not a question of if they will be involved in a data breach, but when -- regardless of the number of risk mitigation strategies they implement to prevent one.
"As organizations scramble to reduce their risk, they face two options: mitigate or transfer," Sherri Davidoff wrote in Data Breaches: Crisis and Opportunity. "Risk mitigation is an important part of the cybersecurity puzzle, but like car accidents, bad things are bound to happen."
And, just as insurance is a wise option for any vehicle on the road, cyber insurance coverage is an increasingly popular contract to help companies reduce the financial risks associated with data breaches and other security events.
The cyber insurance industry has seen a major uptick in recent years: By the end of 2017, insurers wrote approximately $4.5 billion in global cyber insurance premiums annually, a number Orbis Research estimated could reach $17.5 billion in 2023.
Confused about the cyber insurance industry and what it means to your enterprise? In this excerpt from Chapter 12 of her book, Davidoff, founder and CEO of LMG Security and CEO of BrightWise, offers need-to-know info about cyber insurance, including challenges in the industry, different types of cyber insurance coverage available, how to assess breach response teams and more.
Data Breaches: Crisis and Opportunity
Download a PDF of Chapter 12.
Learn more about publisher Pearson Education.
12.2 Industry Challenges
As alluring as cyber insurance is, the industry is fraught with challenges, both for insurers and consumers. Cyber threats are constantly changing. Whereas once a "cyber" policy might need to primarily cover losses due to network outages or data exposure, today's high-risk threats include ransomware, cryptojacking, and more.
IT infrastructures are changing, too -- and the risks change with them. The insurance industry's CRO Forum cited five factors that influence the threat landscape:
- The cloud
- Shadow IT ("when business functions procure IT solutions without involving the IT department")
- Mobile and flexible working
- Bring Your Own Devices (BYOD)
- Internet of Things (e.g., smart buildings, wearable devices, appliances, etc.)
Finally, coverage options are not standardized and are often unclear. Cyber coverage can overlap with standard property and liability coverage, leading to questions about who is responsible for covering a loss -- or whether anyone is responsible at all. "Policy wordings are currently inconsistent, with evidence of some clear cyber exclusions, some explicit inclusion . . . and many policies which are not explicit either way." The details of coverage vary widely, with certain types lumped together under different names depending on the provider, and significant variation in the definitions of common terms such as "personal information."
12.3 Types of Coverage
Cyber insurance can include both first-party and third-party coverage. First-party coverage insures against losses related to damage that affects the insured organization itself, such as data destruction, lost revenue due to operational outages, and other impacts that directly affect the policyholder. Third-party coverage involves liability related to other parties as a result of a cybersecurity incident or data breach, such as consumers affected by exposure of their personal data, banks and card brands that are impacted by a payment card data breach, or regulatory bodies that assess fines.
Common coverage options include:
- Information Security and Privacy Liability - Claims and damages payable due to parties as a result of a data breach or failure of computer security. This can even cover explicit violations of privacy or security-related laws, including liability for failure to notify affected parties in a timely manner following a breach. The costs of legal fees and other investigation expenses are often included.
- Response/Remediation Services - This covers costs associated with breach response. In some cases, the insurer will provide breach response services. Covered services may include:
- Forensics services
- Legal counsel
- Crisis management
- Call center services
- Public relations
- Notification
- Credit monitoring/identity theft protection offers
In some cases, items from this list may be split out into separate coverage. Insurers may also provide proactive breach response training at no charge, such as tabletop exercises, training videos, and more.
- Regulatory Defense and Penalties - Costs related to regulatory action such as investigation, assessment, or penalties due to a violation of privacy or security regulations. For example, this might cover fines assessed by the Office for Civil Rights (OCR) due to HIPAA violations or the legal fees associated with appealing a penalty.
- Payment Card Industry (PCI) Fines and Expenses - Since PCI is a contractual requirement and not a regulation, associated fines and expenses are typically not covered under regulatory defense and penalties. Many insurance policies explicitly exclude contractual obligations. Organizations that process or store payment card data should consider obtaining PCI-specific coverage.
- Network Interruption - Lost revenue due to a cyber event, such as a denial-of-service attack on a retailer's website.
- Media Liability - Costs that the policyholder is required to pay as a result of copyright infringement, plagiarism, defamation, libel, or other negligent acts relating to publication of media.
- Public Relations/Reputation Management - Public relations and crisis communications costs associated with managing a negative publicity event. This typically includes the costs of responsive advertising via digital media, television, and print; social media campaigns; and image monitoring. In some cases, proactive reputation management plans and training are included.
- Information Asset - Expenses to restore, repair, or recreate data after corruption, destruction, or other loss.
- Cyber Extortion - Ransom payments and other fees associated with an extortion involving digital assets. This type of coverage typically covers the costs of retaining security professionals to help resolve the incident.
- Cyber Terrorism - Coverage for damages as a result of an act of cyber terrorism, typically as defined by the federal Terrorism Risk Insurance Act (TRIA). This means losses must exceed $5 million in aggregate and result from a "violent act or an act that is dangerous to human life, property or infrastructure" and is committed "as part of an effort to coerce the civilian population of the United States or to influence the policy or affect the conduct of the United States Government by coercion." Terrorism (and war) are often explicitly excluded from coverage, unless a cyber terrorism endorsement is purchased.
- Proactive Risk Management - A relatively new development in cyber insurance is the integration of risk management tools and services, combined with cyber coverage. This can include security controls assessments, enterprise risk management assessments, response readiness evaluations, vulnerability scans, and other offerings -- in addition to standard breach response services.
From Coffee to Cyber
I stood on the second floor of Lloyd's of London, leaning over the glass railing. Down below, men and women in suits and ties busily conversed in polished wooden booths (or "boxes," as they are called), with gray signs above that read "Advent," "Chaucer," "Beazley," and more. Here and there, small groups of professionals stood conversing. Tiny printers and copiers dotted the floor.
"Lloyd's started out as a coffeeshop in the seventeenth century," my guide explained to me. To attract shippers and merchants to his establishment, proprietor Edward Lloyd provided news about ships that arrived, departed, sank, and other status updates. Groups of customers sat in wooden boxes, drank coffee, and conversed. A sunken ship could be devastating to ship owners and merchants, who would lose not only the vessel but the very expensive cargo as well. Over time, frequenters of Lloyd's Coffee House banded together, and groups began to insure each other so that if a ship sank, many people would chip in to cover the losses. Eventually, Lloyd's of London was born.
In the center of the main floor was the Lutine bell, a recovered remnant from the sunken HMS Lutine. In 1779, the German economy was on the verge of a crash. The HMS Lutine was loaded with an estimated $1.2 million in gold (worth more than $130 million in 2017 U.S. dollars) and sent to Germany to support the banks. A storm struck, and the ship sank, along with its valuable cargo. The ship and its cargo were insured through Lloyd's, and amazingly, the Lloyd's syndicate paid the full cost of the enormous claim, within two weeks. "It was the Lutine that created Lloyd's reputation for paying valid claims -- and for having the financial wherewithal to withstand a loss of such legendary proportions."
In 1858, a recovery operation yielded the ship's bell, which was hung in the center of Lloyd's. The bell is rung to indicate important news: once for bad news (such as a sunken vessel) and twice for good news (such as a returning ship).
Today, brokers on the floor don't just plan for the breach of a vessel -- they plan for data breaches, too. Lloyd's syndicates specialize in specialty insurance, insuring many unusual risks such as kidnapping, political unrest, war, and even famous body parts, such as Keith Richard's fingers. It was the perfect place to learn about a new and rapidly changing type of policy: "cyber" insurance.
12.4 Commercial Off-the-Shelf Breach Response
Cyber insurance has changed the game when it comes to data breach response -- and not for the reasons that most people think. While cyber insurance has existed for two decades in one form or another, the common thread through all policies is financial coverage for claims or expenses due to a cyber event. Around 2009 a groundbreaking change occurred: Insurers began offering data breach response services. Instead of simply covering the costs, insurers provide access to their own response teams that support thousands of policyholders. This may include breach response professionals directly employed by the insurer, as well as forensic analysis, attorneys, and other specialists from third-party vendors.
Mike Donovan, the global head of technology, media and business services for Beazley Group, came up with the idea for breach response insurance in 2007. At the time, data breach regulations had picked up steam. There were notification laws in many states, and breaches were on the rise.
But few organizations had access to the specialists required to provide experienced advice regarding data breach investigations and response, such as attorneys who were familiar with data breach notification laws in all 50 states or forensic investigators who knew how to preserve and analyze volatile, nonvolatile, and network-based forensic evidence. Even organizations that could afford these services without insurance typically did not have the time or connections to build their own panels of providers that specialized in data breaches.
Donovan and his team recognized that many organizations were struggling with cybersecurity incident response. "To be able to develop [breach response] capability was not easy," he reflected in an exclusive interview. "This was particularly true in the midmarket space. It was almost impossible. You're trying to line up credit monitoring after you've had a large breach when you have no relationship with anyone who provides it, you have no idea what the right price should be and you have to get it set up in a week. You have to mail [notifications] and you have no idea who to hire and you have to get them out."
Mishandled data breaches were -- and still are -- far more costly and expensive than a breach where the response is quick, efficient, and tightly managed. Often, consumer lawsuits, negative PR attention, and regulatory fines are the result of delayed notification or lack of effective crisis communications (as the case of Target illustrates; see Chapter 7, "Retailgeddon"). There are even times where a "breach" might not have been declared a breach at all if evidence had been properly preserved.
Donovan and his team realized that their clients needed quick access to services in the event of a breach -- and that insurers were uniquely positioned to help. "With normal insurance, an event happens and you insure the outcome of that event," Donovan explained. "A traffic event happens and the insurer responds to whatever damage exists at that time. The insurer is not in a position to do anything as the accident is happening. In the cyber space, the loss was happening in a very different way. These were crisis events. They were happening in real time."
Instead, Donovan envisioned a different model. His team would essentially act as a clearinghouse, connecting their clients with seasoned experts, right when they needed help the most. "When a breach happened, we already had talent experts," he explained. "We had call centers. We had credit monitoring. We had everything they needed to respond in an effective manner. We could bring it to them immediately." His goal was to reduce the losses for everyone. "If the breach is handled well, the chance that they'll suffer reputational damage, lawsuits is much less."
Today, many insurers offer breach response services (as do law firms, credit bureaus, and cybersecurity companies). When a policyholder contacts the insurer with a suspected breach, a team member quickly responds and brings in third-party specialists such as legal counsel or forensic investigators as needed. The insurers maintain panels of service providers, including forensic analysts, data breach attorneys, call centers, PR firms, and other vendors that specialize in breach response and are available on short notice to assist. For small to midsized organizations or any entity that does not manage data breach crises on a day-to-day basis, the services of an experienced third-party breach response team can prove invaluable.
When breaches are handled effectively, the response and liability costs are greatly reduced, and damage is minimized. By providing policyholders with quick and easy access to experienced providers in a time of crisis, insurers can elevate the quality and speed of data breach response and thereby reduce losses. This is a win-win for both the insurer and the insured.
12.4.1 Assessing Breach Response Teams
When choosing an insurance policy, consider the insurer's role in your breach response process. Will you be leveraging response services provided by the insurer or an approved provider? If so, ask the following questions:
- Ease of Contact - How easy is it to contact your insurer? Do you have 24/7 availability, or more limited hours?
- Responsiveness - What can you expect for the response time? Some insurers may respond in minutes, whereas others may take days or weeks to process your request and assign providers. Responsiveness can make a big difference in the outcome of a data breach investigation, especially given that evidence can spoil at any moment.
- Approved Providers - How experienced are the vendors on the insurer's panel? Some insurers carefully vet their providers based on quality of work to make sure they're hiring experts. Others may select vendors based on favorable rates, market position, or other relationships.
Even if your insurer's panel is excellent, you may prefer to work with a different legal counsel or forensic investigator with whom you have an existing relationship or whose name you received from a trusted source. "Selection of counsel continues to be a delicate issue with insureds," writes risk consultant Richard S. Betterley, "but as we frequently see in other new lines of coverage, carriers typically reserve the right to select, or at least approve, counsel."
Make sure to address the issue of provider selection during the procurement phase -- not in the heat of the moment when a suspected breach occurs. Carefully review the list of approved service providers, and find out what it would take to use your own selected vendor. Consider asking to get your vendors preapproved so that in the event of a suspected breach, you can hit the ground running.
12.4.2 Confidentiality Considerations
Be aware that when you purchase breach response coverage, you may be required to disclose ongoing details of the event with your insurance provider in order to receive coverage. The insurer is footing the bill, after all, and may have the right to review your service agreements, communications with providers, and reports. The vendors that you work with -- including forensic investigators -- may have contractual obligations to the insurer that require them to provide copies of your reports or other information about your case to the insurer.
As with any type of insurance, a negative event may affect your coverage and costs for future policies. For example, in the case of Sony Pictures Entertainment, when a breach occurred in 2011, the company made a $1.6 million claim against its policy with Hiscox. (Ironically, the details of Sony's insurance claims and negotiations were made public after its next major breach in 2014.) Steve Ragan of CSO magazine analyzed the leaked documents and determined that "due to exposures, as well as their $1.6 million claim, Hiscox didn't want to write a new policy, and thus declined to quote at renewal."
12.5 How to Pick the Right Cyber Insurance
Cyber insurance isn't one-size-fits-all. A good policy can help you:
- Transfer risks to a third party
- Respond effectively to a breach
- Reduce the risk of a breach occurring in the first place
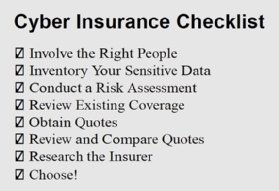
However, a policy that's not aligned with your risk profile or business needs will just be a waste of money. How do you choose the policy that's right for you? Here is a simple checklist:
Buying the Wrong Policy
"We had a really close call." It was Jenn, the office manager at a financial advising firm. Earlier that week, the firm had received a call from the bank notifying it that one of its money management computers had a virus. A staff member clicked on a link and accidentally downloaded malware, which was designed to steal banking credentials. Fortunately, the bank detected the suspicious activity -- just in time.
The firm's executive team was spooked. "We manage a lot of money online," said Jenn. "We need insurance to cover a cash loss in case someone does break into one of our accounts." Within days, the firm's insurance agent sent over a quote. It was long and complex.
"Can you review it and tell us if it's the right coverage for us?" asked Jenn. The agent recommended the policy but the executive team wanted input from a cybersecurity professional.
After speaking with the agent, I reviewed the quote and concluded that it wasn't the right policy at all. The policy covered HIPAA violations, PCI violations, and breach response services appropriate for organizations bound by those regulations. However, the firm was not regulated by HIPAA and rarely handled credit card numbers.
After further research, we discovered that the firm's existing crime policy already covered the risk of money stolen from its online bank account. An in-depth discussion with its IT team revealed that the company had other critical risks that were not on the executive team's radar but that could be addressed by a different type of cyber insurance policy.
Time and time again, organizations ask their agents for "cyber" insurance, and the resulting quote is totally the wrong fit. Many organizations buy it anyway, not realizing until an issue comes up that they haven't covered their most critical risks.
Why does this occur? First, customers may not clearly communicate (or even understand) their coverage needs. Sometimes they just tell an agent they need "cyber" insurance and leave it at that.
On the flip side, agents often don't ask the right questions. They are not cybersecurity experts. Few agents have a strong understanding of the latest security threats or compliance requirements. Cyber policies themselves are so varied that it is hard for anyone to compare. The products are constantly evolving.
Know what risks you need to address, and get the right people involved in your cyber insurance selection process. That way, you can choose a policy that brings real value to your organization.
About the author
 Sherri Davidoff
Sherri Davidoff
Sherri Davidoff is the CEO of both LMG Security and BrightWise Inc. As a recognized expert in digital forensics and cybersecurity, Sherri has been called a "security badass" by The New York Times.
Sherri has conducted cybersecurity training for many distinguished organizations, including the FDIC/FFIEC, the American Bar Association, the Department of Defense and many more. She is a faculty member at the Pacific Coast Banking School and an instructor for Black Hat, where she teaches her "Data Breaches" course. She is also the co-author of Network Forensics: Tracking Hackers Through Cyberspace (Prentice Hall, 2012), a noted security text in the private sector and a college textbook for many cybersecurity courses.
Sherri is a GIAC-certified forensic examiner (GCFA) and penetration tester (GPEN) and holds her degree in computer science and electrical engineering from MIT. She has also been featured as the protagonist in Breaking and Entering: The Extraordinary Story of a Hacker Called "Alien."