Tor networks: Stop employees from touring the deep Web
Are employees using Tor to view blocked Web sites, or mining Bitcoins on corporate resources? Sinister or not, it needs to stop.
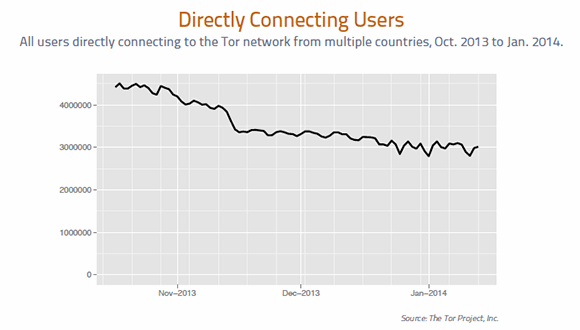
Interest in the deep Web exploded in 2013 as international headlines broadcast the unexpected reach of National Security Agency's mass surveillance programs, and the made-for-Hollywood story unfolded of the Silk Road website and arrest of its alleged proprietor, "Dread Pirate Roberts."
A marketplace for computer hacking and illegal drugs, among other goods and contraband, Silk Road used a Bitcoin-based payment system and "tumbler," which made the identities of the people involved in transactions hard to trace. According to a U.S. criminal complaint, the FBI was not able to defeat the anonymity afforded Silk Road by the onion router (Tor) networks and its decentralized, peer-to-peer Bitcoin payment system, two technologies that underpin much of the deep Web.
How can you see Tor traffic or Bitcoin mining over a network? Both applications use SSL connections over Web ports but can be adjusted to use any port.
Silk Road's alleged proprietor Ross Ulbricht was publicly unmasked because of a simple mistake. In January 2011, a user who identified himself as "altoid" was trying to publicize Silk Road on various websites, including the Bitcoin Talk forum. In October 2011, altoid was looking for an "IT pro in the Bitcoin community" on the Bitcoin Talk forum and directed interested parties to Ross Ulbricht's Gmail address.
While the deep Web encompasses legitimate activities like scientific research and e-commerce, it poses a major problem for information security professionals, because employee participation in legal pastimes (Bitcoin mining) or illegal pursuits (computer hacking, narcotics and pornography) often goes undetected on corporate networks and devices. These activities, violations of almost any acceptable use policy (AUP), open up organizations to security risks, liability and potential litigation.
Internet privacy without anonymity
The deep Web refers to the majority of the World Wide Web that runs over a traditional IP network to fully defined domain names but is not searchable by conventional search engines such as Google or Yahoo. Traditionally, deep websites operated exactly the same as surface websites except they were not linked to other sites, and they opted out of being indexed by search engines. Blocking that traffic was typically done at a Web proxy by allowing access only to approved, categorized websites. Early on, the deep Web was primarily used for storing large data sets (proprietary databases) and hosting restricted or private sites, which were not (necessarily) illegal.
This part of the deep Web does not allow anonymity of the sites or the IP numbers of the people viewing those sites. It rides on the global IP network and is subject to any type of eavesdropping technologies a law enforcement organization or foreign government can deploy.
In 2006, the Tor network was developed with funding from the U.S. Navy and DARPA. It uses multiply relay servers and layers of encryption to create a parallel but truly anonymous Internet that effectively hides the identity of its users. The software to access the Tor networks (.onion) is freely available for download and supports all operating systems. The Tor bundle includes a hardened browser based on Mozilla Firefox and a control panel, which allows users to participate—as relays or proxy endpoints for someone else—and run websites or hidden services such as Silk Road.
The proliferation of the Tor network was not a conduit for a black market on the Internet unto itself. For a black market to thrive, money must change hands anonymously. Otherwise, law enforcement can follow the money trail to the owners of hidden sites and arrest them, which happened before Bitcoin.
Darker net develops
Bitcoin was introduced in 2009 and is now valued against the U.S. dollar for paper currency on global exchanges. (Satoshi Nakamoto, who introduced the Bitcoin concept in a white paper, left the open source project in 2010, according to Bitcoin.org.) Bitcoin is a legal form of currency, and it continues to gain legitimacy as millions of transactions are logged daily and its valuations skyrocket. Some governments, major retailers (Virgin Atlantic, Overstock.com) and third-party vendors are beginning to explore how to facilitate virtual currency—namely Bitcoin—which appears unstoppable as mobile devices continue to proliferate.
Bitcoins can be traded for goods and services or purchased and redeemed for real money, and all of this can be done anonymously. A cryptocurrency, Bitcoin's shared public ledger is a block chain of chronological transactions. People can buy Bitcoins, or they can "mine" Bitcoins by trading computational power to help manage the Bitcoin encryption. But as Silk Road demonstrates, there's a growing dark side to transactions that are virtually impossible to trace to individuals. Bitcoin, coupled with the Tor suite of technologies, has created a perfect recipe for an underground economy that shields illicit activities. In March 2013, the U.S. Department of the Treasury's Financial Crimes Enforcement Network issued guidance on the use of virtual currencies, such as Bitcoin.
Today, there is a real underground economy on the Tor networks that deal exclusively in Bitcoin commerce. The top items on the known websites are drugs of all types, computer hacking, forged documents (passports and credentials), guns and, sadly, a lot of child pornography. Some sites claim to provide murder-for-hire services. (Silk Road's Ulbricht allegedly solicited six murders, but there is no evidence that anyone was killed.)
Doing what the FBI Couldn't
Why should any of this matter to enterprise security organizations? While you may not have to worry about murder, employee participation in unapproved activities on the deep Web can take many forms:
- Employees violating the corporate AUP
- Employees using corporate resources to purchase illegal goods and services
- Employees downloading and using the Tor network to bypass edge security controls
- Employees establishing Tor hidden services on corporate networks
- Employees using corporate services to mine Bitcoins
- Tor networks used by intruders to steal data by bypassing security controls
How can you see Tor traffic or Bitcoin mining over a network? Both applications use SSL connections over Web ports but can be adjusted to use any port. This makes discovery of the protocols impossible if you don't use an application-aware firewall or a Web proxy. A typical stateful firewall is going to allow the traffic out along with the rest of the Web traffic, but Tor uses entry, exit and bridge nodes to access the Tor network. Those IPs, while not static, can be found in several places, with some sites claiming to update them every 30 minutes. By developing a blacklist, and then creating an explicit outbound deny rule on your border firewalls based on those IPs, you should be able to stop a lot of the traffic and build a log of all hosts attempting to connect with the Tor nodes. The blacklist must be maintained to remain relevant.
Bitcoin runs on port TCP/8333. Closing that port to all traffic would block Bitcoin effectively, but people can change the default ports. And because it is not dynamic (yet), it is unlikely to run on any other port.
A more graceful solution is to get to the core of the way both Tor networks and Bitcoin communicate. Both technologies use self-generated SSL certificates to encrypt traffic between nodes and servers. Using self-signed digital certificates, or SSL digital certificates not signed by a certificate authority, is a typical communications strategy of botnets and other nefarious actors. As a rule, it's not a good idea to allow outbound SSL traffic across your network at all. Web proxy services are very good at proxying SSL connections and can stop all traffic using self-signed digital certificates. Because both Tor and Bitcoin run on Web service ports, proxies and application-aware firewalls can inspect traffic deeper in the stack and, regardless of the port, block traffic based on packet content. This stops port hopping and endpoint shifting, which are difficult to manage, and allows for the traffic to be stopped based on its behavior rather than the port, source or destination, which are variable.
Clear policy on Tor usage
The proliferation of Tor networks and the coming of age of anonymous digital money mean that companies need to begin to pay attention to the risk of employees using corporate networks and resources to access these sites. Unmonitored activities, criminal or otherwise, can create security risks and liability for organizations.
Prevention should start with awareness, training, and making sure the supporting processes and policies speak directly to the use of the Tor bundle on corporate resources. Once the AUP is updated, it is important to communicate to the entire staff that downloading the Tor bundle on any company computer or use of the Tor network over company networks is a fireable offense. Once the policy is in place and communicated, then the traffic should be stopped, and attempts logged for investigation.
About the author:
Adam Rice is an information security professional with 17 years of experience. He has served as chief information security officer at a defense and aerospace Fortune 500 company; chief security officer of a global telecommunications company; general manager and vice president of a managed security services business; director in several network consulting companies; and is a retired U.S. Army non-commissioned officer. He is also a regular contributor to several information security publications.







