
beebright - stock.adobe.com
Cyberinsurance carrier Chubb investigating possible data breach
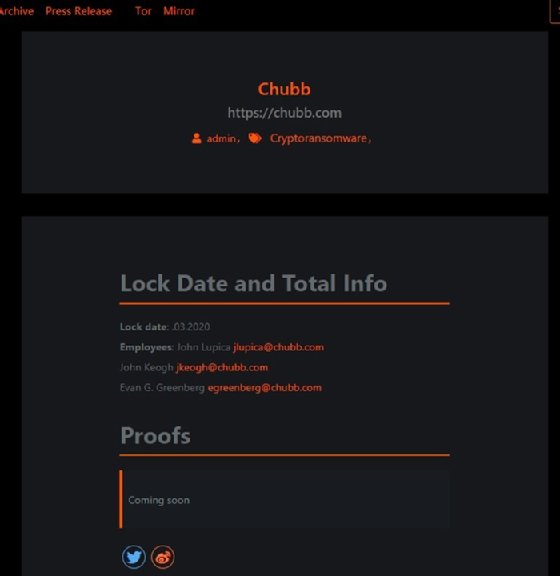
Insurance giant Chubb confirmed it is investigating an incident that may involve the Maze ransomware group, which claims to have stolen sensitive data from the company.
Cyberinsurance provider Chubb confirmed it is the investigating a security incident that occurred earlier this month.
According to a statement from Chubb, "the incident may involve unauthorized access to data held by a third-party service provider." The insurance carrier's statement follows an earlier post from the Maze ransomware group, which lists Chubb as its latest victim as of March 20th. It's unclear if the attack, which was first reported by TechCrunch, involved exfiltration of sensitive corporate data; Maze had not published any of the allegedly stolen data.
"We are working with law enforcement and a leading cybersecurity firm as part of our investigation," a Chubb spokesperson said in an email. "We have no evidence that the incident affected Chubb's network. Our network remains fully operational and we continue to service all policyholder needs, including claims. Securing the data entrusted to Chubb is a top priority for us. We will provide further information as appropriate."
Chubb, which is one of the largest insurance providers in the world, did not say who the third-party provider was, or what type of data was potentially exposed in the incident. The company declined to comment further.
Emsisoft threat analyst Brett Callow said if Maze has indeed obtained sensitive cyberinsurance data, it could be used future attacks even more dangerous. "Maze could potentially use the data for spear phishing and of course if it's published online, other criminals could access it and use it for the same things," he said. "Even other ransomware groups, because they could download the data."
In addition, ransomware has been shown to spike in the spring and summer months, according to Emsisoft.
While Chubb said there's no evidence the company's network was compromised, threat intelligence firm Bad Packets noted on Twitter that its scans found five Citrix NetScaler/Application Delivery Controller (ADC) servers that were vulnerable to a critical flaw, CVE-2019-19781, that was first disclosed in December.
The vulnerability has been exploited by different threat groups in recent months. One example is the Chinese state-sponsored threat group known as APT41, which FireEye recently said had executed one of the broadest cyberespionage campaigns its researchers had seen in several years. Part of that campaign involved exploitation of the Citrix NetScaler/ADC flaw.
"There's evidence that Chubb was running vulnerable systems, systems that ransomware groups have been known to exploit in the past so if they weren't hit, they were actually quite lucky," Callow said.
The potential breach comes just one week after Maze made news with a pledge to stop attacking hospitals during the COVID-19 pandemic.






