
olly - Fotolia
Ninety percent of dark web hacking forum posts come from buyers
Positive Technologies built a picture of dark web hacking forums via data from the 10 active forums and over 8 million users, though the veracity of such posts remains unclear.
Nine out of 10 posts on dark web hacking forums are made by those looking for hacker services -- not by hackers themselves -- according to new research from Positive Technologies.
Positive Technologies' report, titled "Custom Hacking Services," was released Tuesday and analyzes "the ten most active forums on the dark web, which offer services for hacking websites, buying and selling databases, and accessing web resources." Those forums, which are not named in the report, include over 8 million registered users, 7 million topics and 80 million published posts.
Beyond the 90% of users soliciting hacking services, the remaining 10% includes those selling hacking services (7%), those selling hacking tools and programs (2%) and people searching for hacking accomplices (1%). Positive Technologies senior cybersecurity analyst Vadim Solovyov told SearchSecurity via email that for 8 million accounts "it is impossible to estimate the number of users" due to the potential for duplicates.
Asked about the veracity of the services being offered on such forums, Solovyov said it's challenging to establish the veracity of posts.
"Anonymity is the first priority on the dark web. Illegal hacking services can be sold in this place. All these advertisements are not legitimate. Moreover, some members use anonymity to scam others. So, you cannot be 100% sure about the reliability of such services," Solovyov said.
The report notes that since March 2020, Positive Technologies noticed "a surge of interest in website hacking." In addition, the report points out that one potential cause may have been COVID-19, which was declared a pandemic by the World Health Organization (WHO) that same month and resulted in "an increase in the number of companies available via the Internet."
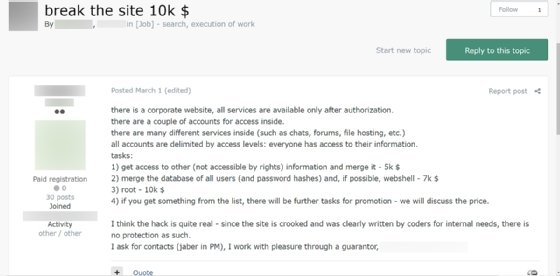
As for why the aforementioned potential "customers" need the hackers, the report said 69% of inquiries were for obtaining access to a website, 21% for downloading client databases (which accounts for "competitors and spammers who collect lists of addresses for targeted phishing attacks aimed at a specific audience"), 4% for placing malicious files, 3% for deleting information from a website, 2% for website hacking-related programs and 1% for seeking accomplices.
While the report paints a picture of dark web hacking forums, it may be impossible to gain a complete picture considering that the dark web by nature is focused on privacy and anonymity. For example, as Solovyov said, it is difficult to gain an understanding of how many advertisements referenced in the report are legitimate, or how many of the 8 million accounts represent unique people (or even people at all).
In addition, short of speaking with multiple dark web hackers and/or those looking for said services and confirming their identities, the task of finding out what kinds of people are paying for hacking services on the dark web -- and what their end goals are -- is virtually impossible.
However, the 8 million figure may at least symbolically represent the massive influx of dark web users over the last decade. In a recent SearchSecurity report about the state of the dark web in 2021, author and longtime dark web expert Eileen Ormsby discussed how the dark web has "devolved" over time, saying that while there used to be more civil, high-level discussions among a smaller community built in substantial part by cypherpunks, now, "you've got every man and his dog on there."
Alexander Culafi is a writer, journalist and podcaster based in Boston.







