
igor - Fotolia
Researchers hack Apple Pay, Visa 'Express Transit' mode
Academic researchers discover an attack technique that enables them to make fraudulent transactions on locked iPhones when Apple Pay and Visa cards are set up for transit mode.
New research shows contactless payment can be more of a risk than a convenience.
Combining an iPhone, Apple Pay and a Visa card, academic researchers Andreea-Ina Radu and Tom Chothia at the University of Birmingham, along with Dr. Ioana Boureanu, Dr. Christopher J.P. Newton and Professor Liqun Chen of the University of Surrey, discovered a way to make fraudulent transactions through contactless payment. More significantly, they found a way to conduct such attacks even if the iPhone is locked.
While the attack requires physical possession of or proximity to the victims' iPhone, the ramifications could be significant. Researchers were successful in bypassing the contactless limit so they could withdraw any amount. In a video demonstration, the researchers were able to steal 1,000 pounds from an account.
One feature that particularly enabled the hack's success was Apple Pay's Express Transit mode, which was introduced in 2019. According to the research paper, it allows Apple Pay to be used without unlocking the phone. With no authentication required -- such as a fingerprint or Face ID -- the risk of stolen transactions increases.
The attack works by interfering with the broadcast code, used by Transport for London's (TfL) transit gates or turnstiles. Once researchers discovered the TfL code, which they dubbed magic bytes, they found they were able to trick the iPhone into thinking it was communicating with a transit gate rather than an EMV card reader.
To pull it off, all researchers needed was an iPhone, a card emulator, an EMV reader and a laptop. During tests, they used a Proxmark device for the reader emulator and a Near Field Communication (NFC)-enabled Android phone for the card emulator. From there, they were able to deploy a man-in-the-middle attack. The Proxmark device was used to communicate with the victim's iPhone, while the Android phone communicated with the payment terminal.
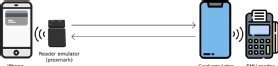
"The Proxmark and card emulator need to communicate with each other," the research team wrote in a GitLab post. "In our experiments, we connected the Proxmark to a laptop, to which it communicated via USB; the laptop then relayed messages to the card emulator via WiFi. The Proxmark can also directly communicate with an Android phone via Bluetooth. The Android phone does not require rooting."
The researchers reiterated that it does "require an iPhone to have a Visa card set up as transport card." However, it does not require assistance from the merchant and researchers confirmed that back-end fraud detection checks did not prevent any of the payment tests, no matter how the high amount.
"In order to relay transactions over the contactless limit, the Card Transaction Qualifiers (CTQ), sent by the iPhone, need to be modified such that the bit (flag) for Consumer Device Cardholder Verification Method is set," the GitLab post noted. "This tricks the EMV reader into believing that on-device user authentication has been performed (e.g. by fingerprint)."
Room for improvement in Express Transit feature
Some good news rests on the fact that the hack can only be achieved through the combination of Apple Pay, an iPhone and Visa.
"This vulnerability is due to the lack of checks performed on the iPhone combined with the lack of checks at the Visa back end," the researchers wrote. "Apple Pay with Mastercard is not vulnerable and nor are Mastercard and Visa with Samsung Pay."
To mitigate the attack technique, the research team recommended that all iPhone users disable the transit mode on Visa cards.
Chothia and Boureanu told SearchSecurity that Apple and Visa share equal responsibility as the vulnerability is due to mistakes on both sides. In addition, Chothia said each company could fix this issue on its own.
In particular, he said, there is no reason for Apple to allow 1,000 pound payments to be performed in Express Transit mode.
"Apple should limit the value that can be done without fingerprint authentication," Chothia wrote in an email to SearchSecurity.
Boureanu agreed that each company could fix the issue in a different way. For example, Visa could check more details it receives on the back end, which show if the merchant was a transit one or not, and if the user was authenticated to make the payment.
In a statement to SearchSecurity, Visa said cards connected to Apple Pay Express Transit are "secure and cardholders should continue to use them with confidence.
"Variations of contactless fraud schemes have been studied in laboratory settings for more than a decade and have proven to be impractical to execute at scale in the real world. Visa takes all security threats very seriously, and we work tirelessly to strengthen payment security across the ecosystem," a Visa spokesperson said in a statement to SearchSecurity.
Visa did not comment on the record about a potential fix for the problem.
Chothia said the features that enable contactless transactions through locked devices are fine, and Express Transit is quite safe on Samsung or when using Mastercard. "Apple and Visa just need to improve their security design," he said.
Similarly, Boureanu said the features don't require rethinking of such features, but in this case, they do require repairing. She also emphasized how other mobile payment providers who have travel modes were not affected by their research.






