
arthead - stock.adobe.com
Log4j 2.17.0 fixes newly discovered exploit
The Log4j 2.17.0 update is the third of its kind since Log4Shell was disclosed and the mass exploitation began. Versions 2.15.0 and 2.16.0 patched remote code execution bugs.
The Apache Software Foundation released its third Log4j update since the disclosure of Log4Shell earlier this month.
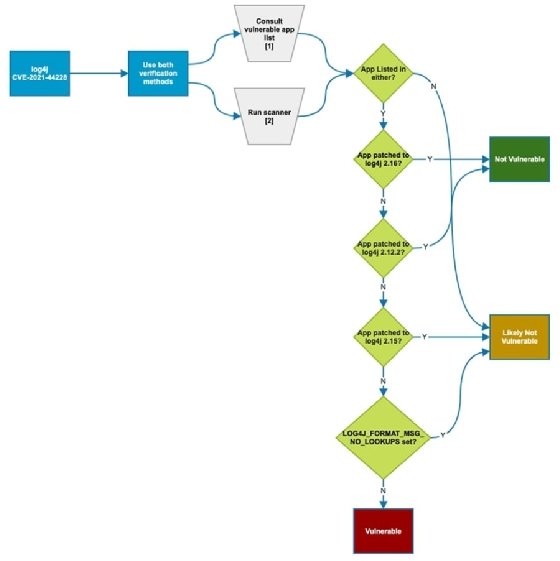
Log4j 2.17.0 fixes a new vulnerability reported late last week that enables denial-of-service attacks against vulnerable instances of the popular Java logging framework. The flaw, CVE-2021-45105, occurs due to older Log4j versions not protecting against uncontrolled recursion from self-referential lookups.
Apache's Log4j vulnerabilities page describes the high-severity bug in the following way:
"When the logging configuration uses a non-default Pattern Layout with a Context Lookup (for example, $${ctx:loginId}), attackers with control over Thread Context Map (MDC) input data can craft malicious input data that contains a recursive lookup, resulting in a StackOverflowError that will terminate the process," the page read.
While Apache primarily recommends users update to the latest Log4j version, they also provided a second mitigation, involving configuration changes, on the vulnerabilities page.
2.17.0, released Friday, marks the third patch for Log4j since the now-infamous Log4Shell vulnerability became publicly known a week and a half ago. Log4j 2.15.0 helped mitigate the initial remote code execution (RCE) vulnerability, tracked as CVE-2021-44228, while 2.16.0 fixed CVE-2021-45046, another critical RCE flaw related to Log4Shell.
The Cybersecurity and Infrastructure Security Agency (CISA) added to its Log4Shell vulnerability guidance page to reflect the new update.
The U.S. government cybersecurity agency also released Emergency Directive 22-02 on Friday, which requires other federal agencies to take inventory of vulnerable Log4j systems and apply the appropriate patches and/or mitigations by 5 p.m. Eastern time on Dec. 23. By Dec. 28, agencies are required to report identified vulnerable systems -- and actions taken -- to CISA.
In a call with media held Dec. 14, CISA executive assistant director for cybersecurity Eric Goldstein said there had been "no confirmed instances of federal agencies that have been compromised."
Alexander Culafi is a writer, journalist and podcaster based in Boston.






