
Getty Images/iStockphoto
March ransomware attacks strike finance, government targets
In March, ransomware reports and disclosures showed a variety of victims, from public schools and county governments to financial services firms and large enterprises.
As tensions rose globally surrounding further armed conflicts and potential cyberconflicts stemming from Russia's invasion of Ukraine, the U.S. saw a continued wave of ransomware attacks both in the public and private sectors.
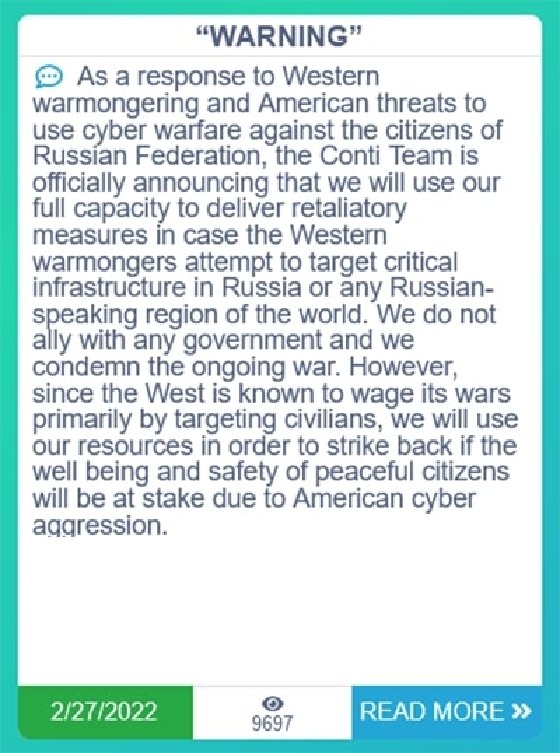
Following the invasion in late February, the Conti ransomware gang issued a statement supporting the Russian government and threatening attacks against Western nations, including the U.S. While the White House recently warned that the Russian government was exploring possible cyber attacks against the U.S., there wasn't a significant increase in reported ransomware attacks for March.
Editor's note: SearchSecurity tracks ransomware disclosures and public reports each month. This does not include purported attacks claimed by ransomware gangs that have not been confirmed by the victim or corroborated through other means.
However, March 2022 showed no signs that ransomware groups are slowing, either. SearchSeccurity tracked 28 reports and disclosures of ransomware attacks last month, including attacks against major financial service companies and public entities that left hundreds of thousands of potential victims.
Public sector victims
The month opened with yet another ransomware attack aimed at a public school, this time in Berks County, Penn., where the superintendent of the Fleetwood School District reported that schools were experiencing technical difficulties on March 2. According to the superintendent's statements, while some of the technology was disrupted, no student or staff information was accessed, and classes were able to take place as scheduled.
The following week, cybersecurity company Emsisoft told Valley Central News that while examining the leak site for the ransomware gang LockBit, they discovered that the Brownsville Public Utility Board (BPUB) was listed as a victim of the group. BPUB is a city-run organization that is responsible for providing water and power to Brownsville, Texas, one of the largest cities in the southern part of the state with nearly 200,000 residents.
Following the discovery by Emsisoft, on March 8, BPUB published a press release on its website, acknowledging the incident and saying that it had taken steps to protect the affected environment and was investigating the incident.
On March 25, BPUB provided an update to Valley Central and the board's customers, saying that there would be delays in seeing accurate balances in customer accounts. As of that update, BPUB still could not confirm what information or data was affected.
As the month went along, more public entities began to report ransomware attacks that took down some of their systems
During the weekend of March 19, the town of Plainfield, Conn., was hit by threat actors, affecting parts of the town's electronic administrative system and large segments of the police department. The town's police department said that following the ransomware attack, the police department lost access to electronic records, bodycam video and fingerprinting services and had some of their telephone service disrupted.
That same weekend, on March 20, another public service was disrupted by a ransomware attack, this time a few thousand miles away in San Antonio. According to a news release on the Bexar County Appraisal District website, the office was hit early on Sunday morning, and some systems were encrypted and select files were damaged in the incident.
According to the office, the property records database was not hit by the ransomware attack and as of its latest release on March 21, the rest of the services were still being recovered and restored.
To close the month, the ransomware group Hive claimed to hit one of California's largest providers of Medi-Cal, the Partnership HealthPlan of California. The healthcare provider, whose website as well as other services are still down, provides the state's version of Medicaid, focusing on helping low-income residents.
Hive, which struck several healthcare organizations over the past year, claimed to have stolen personal information from over 850,000 residents. It was first reported on March 24 by The Press Democrat that the group was experiencing network disruptions. So far, Partnership HealthPlan of California has not released a timeline for the recovery of their systems or what information may have been exposed as a result of the ransomware attack.
Financial service providers targeted
Public entities were not the only victims during the month of March, as the private sector was again hit hard, with large and small companies alike disclosing attacks.
During the month, several financial service providers, including Certified Title Corporation, Horizon Actuarial Services and Medaglia & Murphy, Inc., each disclosed that they had been the victims of ransomware attacks. While none of the companies specified what data may have been accessed or what systems were affected in the ransomware attack, they all sent out notification letters to their clients as well as to several state attorneys general in case any information was misused.
Horizon Actuarial Services was different from the other finance companies that reported ransomware attacks, as the company admitted to having paid the ransom following an attack in November; the company announced that several clients potentially had information accessed, including two rather large names.
The group's letter to potential victims and to Maine's attorney general said, "Horizon Actuarial provides technical and actuarial consulting services for benefit plans in the United States. You are receiving this letter because you or your family member are or were a participant in, or had contributions made on your behalf to, the Major League Baseball Players Benefit Plan, through which your information was provided to Horizon Actuarial for business and compliance purposes."
While Horizon said that it paid the ransom demanded in exchange for the data not to be misused, the ramifications of the players' benefit plan being exposed are massive. According to the office of Maine's attorney general, there were 13,156 victims of this breach of the Major League Baseball Players Benefit Plan, an entity that holds the personal and financial information of current and former MLB players, some of the wealthiest professional athletes in the world, and their families.
Another victim of the Horizon breach was the New York Teamsters Conference Pension and Retirement Fund, which potentially affected 42,384 people, according to the Maine AG.
On the other side of finance, real estate groups also said in March that they had been the victims of ransomware attacks.
Sudler Property Management, one of the largest real estate brokers in Chicago, reported to Maine's attorney general that it too had been attacked by ransomware. The notice, submitted on March 11, said that 8,860 people were affected by the breach. While it did not specify who had what information potentially exposed, it said that personal information such as Social Security numbers, bank account information and names may have been compromised in the ransomware attack.
It was not just local or regional companies in the U.S. that were hit by ransomware in March. Two international companies, Bridgestone and Snap-On Tools, suffered apparent ransomware attacks in March.
While both Bridgestone and Snap-On each admitted to suffering cyber attacks and disruptions in their systems, so far neither has confirmed the attacks as involving ransomware. However, two ransomware gangs were quick to take credit for these incidents.
In Bridgestone's case, it was reported that their data breach was caused by LockBit, who threatened to leak the data that they stole on their website if no ransom was paid.
For Snap-On Tools, another major ransomware group, Conti, claimed responsibility for the attack. On March 17, the group, which is allegedly responsible for major attacks like the one against the Irish Health Service Executive in 2021, said that it was responsible for the breach of Snap-On.
On its website, Snap-On noted that there did not appear to be any actual theft or misuse of data, and that the company shut down aspects of their network as a precaution.
This month also saw continued activity from the extortion group Lapsus$, which, while not explicitly using ransomware, claimed to hit both Nvidia and Samsung in February. In March, the group claimed two more enterprise victims in Microsoft, which had product source code stolen, and Okta, which had customer data stolen in a third-party breach.








