ProxyLogon researcher details new Exchange Server flaws
After testing Microsoft's mitigations for ProxyLogon, security researcher Orange Tsai discovered new Exchange Server bugs, including one flaw that took more than a year to fix.
Listen to this article
The security researcher who discovered the ProxyLogon vulnerabilities in Microsoft Exchange Server last year detailed additional Exchange vulnerabilities this week, including one flaw that took more than a year to patch and disclose.
Orange Tsai, a security researcher with Taiwan-based consulting firm Devcore, first found ProxyLogon, a server-side request forgery vulnerability that could allow an attacker to bypass authentication in Exchange servers, in late 2020. Subsequently, he demonstrated how the critical flaw could be chained together with another Exchange Server vulnerability, tracked as CVE-2021-27065, to enable remote code execution.
Threat actors including the Chinese nation-state group known as Hafnium exploited the vulnerabilities in a series of zero-day attacks prior to Microsoft's public disclosure and patching. The ProxyLogon discovery spawned another set of dangerous flaws later that year, dubbed ProxyShell, which affected a multitude of unpatched Exchange servers.
In a blog post Wednesday, Tsai detailed a new set of Exchange Server flaws he discovered and named ProxyRelay, which allow attackers to bypass authentication or achieve code execution without user interaction. The vulnerabilities affect Windows New Technology LAN Manager (NTLM), a set of tools used to authenticate users' identities.
"Since it's an entire attack surface instead of a single bug, this idea could be applied to different contexts, causing different vulnerabilities," Tsai wrote in the blog.
One flaw, tracked as CVE-2022-21979, is an Exchange information disclosure vulnerability that Tsai first reported to Microsoft on June 2. However, the tech giant did not publicly disclose or patch the flaw until Aug. 18, after several requests for extensions and follow-ups by Devcore.
"We could have published this article earlier (the original bug was reported to MSRC [Microsoft Security Response Center] in June 2021 with a 90-days Public Disclosure Policy). However, during communications with MSRC, they explained that since this is an architectural design issue, lots of code changes and testings are expected and required, so they hope to resolve this problem with a one-time CU (Cumulative Update) instead of the regular Patch Tuesday. We understand their situation and agree to extend the deadline," Tsai wrote.
After Microsoft released the CUs for Exchange Server 2019 and 2016 in April, Tsai's exploit still worked on the latest version because the patch was not enabled by default. The patch for CVE-2022-21979 was eventually completed and released as part of Microsoft's August 2022 Patch Tuesday.
Microsoft has not addressed why it took so long to disclose and patch CVE-2022-21979.
"We released updates to address this issue in August 2022, and customers who have installed all available updates are already protected. We appreciate the work of Orange Tsai and all security researchers who work with us to identify and address issues through coordinated vulnerability disclosure," a Microsoft spokesperson said in an email to TechTarget Editorial.
Tsai noted in his blog post that a security researcher known as Dlive from Chinese company Tencent Security Xuanwu Lab had independently found and reported the attack surface to Microsoft and shares credit on several of the CVEs for ProxyRelay.
ProxyRelay discovery
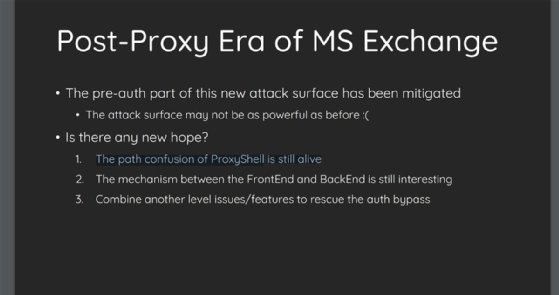
Tsai first found the flaws while researching whether there was a way to bypass Microsoft's mitigation for the 2021 Proxy-related attacks. While the mitigation addressed the problems Devcore researchers had disclosed, Tsai said that because Microsoft only fixed the "problematic code," Exchange remained vulnerable to similar attacks in the future.
His theory was proven in September when two new Exchange Server zero-day vulnerabilities, which researchers called ProxyNotShell, were exploited in the wild. These flaws, discovered by Vietnamese cybersecurity company GTSC, were similar to ProxyLogon and were also exploited as zero-days.
Another attack vector Tsai tested was NTLM, which threat actors could use to impersonate any user in Exchange services, according to the blog. Further research and penetration tests revealed it was possible to use NTLM and relay the malicious authentication from one Exchange server to another.
Although it took more than one year to mitigate the attack surface, the patch for CVE-2022-21979 was successful, according to Tsai, because it "permanently eliminates all relay attacks on Backend by forcibly turning on the Extended Protection Authentication in IIS [Internet Information Services]." Previously, Devcore researchers used that to bypass authentication.