
Alex - stock.adobe.com
Coalition: Vulnerability scoring systems falling short
Coalition said enterprises faced more substantial fallout from attacks on Citrix Bleed and Progress Software's MoveIt Transfer due to inadequate vulnerability prioritization.
In a new report Wednesday, cyberinsurance firm Coalition highlighted the limitations of current vulnerability scoring and prioritization systems that contribute to enterprises' timely patching struggles.
The insurer published its "Cyber Threat Index 2024," which detailed several critical vulnerabilities that policyholders faced throughout 2023 and challenges that ensued. The report said data was compiled using "Coalition's threat-collection technology" such as honeypots, scanning data and Coalition's Exploit Scoring System (ESS) that was launched in June. The insurer analyzed vulnerability trends through training an autoregressive integrated moving average model.
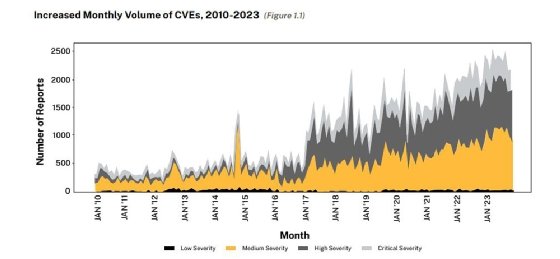
The report reinforced how essential timely patching is to effective security postures, especially with the growing number of disclosed vulnerabilities. "In fact, Coalition's claims data showed that policyholders with even one unpatched critical vulnerability were 33% more likely to experience a claim," the company wrote in the report.
Throughout last year, the insurer found that current vulnerability scoring and prioritization frameworks such as the CVSS and CISA's Known Exploited Vulnerabilities (KEV) catalog, which enterprises use to prioritize patching efforts, often fall short. "Legacy vulnerability scoring systems commonly lack a practical understanding of real-world exploitation," Coalition said in the report.
The report noted that when used alone, the existing systems can provide misleading results for organizations looking for advice on where best to direct their patching efforts. Prioritization is crucial because organizations don't have time to navigate the massive influx of vulnerabilities.
The report also emphasized the ongoing race between enterprises and threat actors to patch a vulnerability before it is exploited. "Instead of considering the commonality of a vulnerable software configuration, CVSS creates a disconnect between severity and the actual likelihood of exploitation in the wild," the report said.
In some cases, Coalition found that severity ratings and delays in vulnerability disclosures led to organizations having sufficient time to patch before a threat actor exploited the flaw. However, security advisories and alerts for other vulnerabilities sometimes raised overly excessive alarms.
'Celebrity CVEs'
The report cited several examples of what Coalition called "celebrity CVEs," or high-profile flaws that dominated news cycles but sometimes produced misleading impressions for organizations. For example, two remote code execution zero-day vulnerabilities, tracked as CVE-2023-42114 and CVE-2023-42115, in the Exim Mail Transfer Agent were disclosed in September. Trend Micro's bug bounty program Zero Day Initiative (ZDI) published a security advisory for CVE-2023-42115 that Coalition said caused "panic among security professionals."
ZDI's advisory documented a 9.8 CVSS score and warned that exploitation did not require authentication.
However, Coalition scanned policyholders for vulnerable Exim infrastructure and found that the numbers did not match the hype. Out of 330,000 instances, its scans only detected the vulnerable configuration once for CVE-2023-42114 and four times for CVE-2023-42115.
"Given the number of global Exim installs, the results of an easily exploitable vulnerability combined with a common configuration could have been catastrophic. But in reality, attackers could only exploit these vulnerabilities if the mail servers used a specific configuration," Coalition wrote in the report.
That was not the case for another critical vulnerability last year in Progress Software's MoveIt Transfer product, which was widely exploited by a threat actor associated with the Clop ransomware gang. While attacks did not involve ransomware deployment, the threat actor was able to claim hundreds of MoveIt customers by exploiting one vulnerability.
Progress disclosed the SQL injection zero-day vulnerability on May 31, but Coalition said there were warning signs well in advance of the disclosure. For example, the company's honeypots detected initial scans for the vulnerability as far back as November 2022.
"Roughly 16 days before Progress published its security advisory, our honeypots detected a 1,000% spike in scans for MOVEit tech. A second spike began on June 1, 2023, when security companies began scanning the internet to understand the scope of the problem," the report said. "The speed with which the Cl0p ransomware group exploited the MOVEit vulnerability highlights how, at times, even the most relevant information comes too late."
As a result, Coalition said, combining honeypot data with automated vulnerability prioritization is "an exciting prospect." To that end, Coalition's long-term goal is to combine honeypot traffic with machine learning to assign weights to specific activity. The honeypot data would be integrated into Coalition's own ESS model, which was announced last year and compares descriptions of newly published CVEs to previously published vulnerabilities to predict the likelihood of exploitability.
Another example was Citrix Bleed, two unauthenticated buffer-related vulnerabilities tracked as CVE-2023-4966 and CVE-2023-4967 that affected Citrix NetScaler ADC and NetScaler Gateway. Citrix disclosed and patched the flaws in October, but Mandiant later discovered that initial exploitation occurred August. In November, CISA and the FBI warned that the LockBit ransomware gang was exploiting the Citrix Bleed vulnerabilities.
"While it made sense for Citrix to avoid alarmism and wait and see whether the vulnerability would be exploited at scale, there were clear early warning signs, shown by honeypot activity as early as July," Coalition said in the report.
While attackers' use of zero-day vulnerabilities was significant last year, Coalition said Citrix Bleed is a reminder of threat actors' ability to build exploits even after a patch is released and ramp up attacks, highlighting the need for better vulnerability prioritization.
"A policyholder following Coalition's notifications could have implemented a patch six days before Citrix announced exploits were possible and 42 days before CISA warned ransomware gangs were capitalizing on the vulnerability," the report said.
Scott Walsh, principal security researcher at Coalition, told TechTarget Editorial that Citrix Bleed shows how the line between zero-day and N-day vulnerabilities has become blurred because enterprises can't keep up with the pace at which vulnerabilities are disclosed.
The report found a significant correlation between vulnerability exploitation and ransomware. Vulnerabilities placed among the top three vectors that ransomware operators used in 2023 to compromise victim organizations.
"Our claims data shows vulnerability exploitation as a root cause directly leading to ransomware claims," Walsh said.
Exposed RDP leads to ransomware
Ransomware groups also targeted organizations with Remote Desktop Protocol (RDP) exposed to the internet. In August, Sophos published a report that warned RDP was involved in 95% of attacks from the first half of 2023 and urged enterprises to prioritize security.
Despite a dip in the summer, Coalition also observed RDP traffic growth in 2023. "We detected a 59% increase in unique IP addresses that were scanning for RDP from January 2023 to October 2023," the report said.
By combining the scanning and claims data, Coalition determined "that businesses with RDP exposed to the internet are the most likely to experience a ransomware event."
While an array of internet-exposed services caused challenges for Coalition policyholders, one of the biggest concerns last year involved exposed databases. Coalition emphasized that attackers frequently target unpatched and end-of-life (EOL) versions of databases. The insurer found that businesses using EOL versions in their environment were "three times more likely to experience a claim."
Coalition said it found that a "concerning" number of EOL and unpatched SQL servers remain internet-exposed. SQL injection vulnerabilities, which were involved in the MoveIt Transfer attacks, posed a significant threat to enterprises last year. Coalition's report examined Microsoft SQL servers and found an alarming trend.
"Our scans found over 100,000 EOL Microsoft SQL servers, including over 10,000 running Microsoft SQL Server 2000, released in 2001," the report said.
To tackle the vulnerability patch management challenges, Coalition said programs should embrace an array of sources including CVSS, KEV and security advisories. The report warned enterprises not to rely on KEV alone because it doesn't include global coverage and has "some delays in publication."
Coalition also urged enterprises to implement a managed detection and response (MDR) service. "Businesses with MDR in place have a 50% faster median time to respond (MTTR), dramatically lowering the impact of cyber incidents," the report said.
While EOL Microsoft SQL servers and exposed RDP caused significant challenges last year, Walsh said there are new technologies that enterprises need to be cautious with in 2024. One is the Ivanti Connect Secure VPN, which contains several vulnerabilities attackers continue to exploit.
"Recently, our claims data is showing increased risk from Ivanti Connect Secure VPN and Fortinet SSL VPN products, as well as on-premises Microsoft Exchange servers. We continue to monitor this closely," he said.
Arielle Waldman is a Boston-based reporter covering enterprise security news.






