Cloud storage security best practices
Protecting stored cloud data requires meticulous planning and a well-crafted strategy. Here are the steps to take to keep your organization's data safe and secure in the cloud.
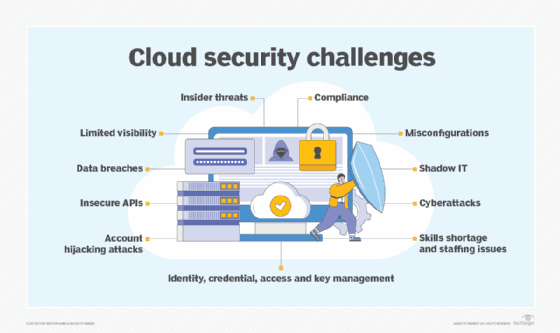
As organizations expand their use of public cloud storage services, enterprise IT teams are increasingly required to coordinate security, governance and data protection controls across multiple cloud platforms, regions and service tiers. Without intentional coordination, each cloud storage service may be able to operate with its own management interface, identity controls and telemetry systems -- effectively creating a series of isolated security domains.
As the number of cloud storage environments grows, it becomes more difficult to enforce security, governance and lifecycle policies consistently. Controls that are tightly managed in one storage service may be misconfigured or loosely enforced in another, creating security gaps that attackers can exploit.
The following best practices can help organizations strengthen cloud storage security and reduce risk across distributed cloud storage environments:
Extend enterprise identity governance across cloud storage platforms
Integrating cloud storage authentication with enterprise identity governance can help organizations standardize access controls and reduce identity-related risk. Coordinated identity governance limits overprivileged accounts, credential misuse and unmanaged access paths across storage services. The following practices can help IT management implement enterprise identity governance across cloud storage environments:
- Replace local storage credentials with federated authentication integrated with enterprise identity providers.
- Register service, automation and API accounts in centralized identity directories and assign clear ownership.
- Implement automated credential rotation or short-lived authentication mechanisms for workload and automation identities.
- Enable single sign-on for human users accessing cloud storage services and enforce multi-factor authentication.
- Establish standardized enterprise roles and map them consistently to each provider's native access model.
- Forward authentication events, privilege changes and API activity to centralized security monitoring platforms.
- Use conditional access policies to restrict storage access based on device posture, location and risk signals.
- Classify sensitive data and apply stricter access and logging policies to high-risk storage buckets, volumes and datasets.
- Enforce least privilege and conduct periodic entitlement reviews.
- Use just-in-time or time-bound privileged access to reduce persistent administrative permissions.
Integrate cloud storage telemetry into enterprise monitoring workflows
Cloud storage platforms generate valuable security telemetry, but critical signals often remain confined to provider-specific consoles. Centralizing storage telemetry improves visibility and enables security and storage teams to collaborate and correlate activity across identity, network and endpoint domains.
- Enable logging for authentication activity, API operations, configuration changes, retention modifications and object or snapshot deletions.
- Forward storage logs to SIEM, XDR or centralized security analytics platforms.
- Monitor retention and immutability changes and alert on backup or snapshot deletion attempts.
- Analyze access patterns programmatically to detect abnormal API usage, large data transfers or access from unexpected accounts or regions.
- Configure detection rules that correlate activity across security domains to identify privilege escalation or unauthorized role changes affecting storage resources.
- Enforce secure deletion and lifecycle policies to prevent sensitive data from persisting beyond retention requirements.
- Govern vendor and third-party access using time-bound credentials, approvals and dedicated audit trails.
Treat cloud backup and recovery storage as protected security domains
Cloud backup repositories are often the final recovery option after a ransomware attack. Because backups are increasingly being targeted, recovery storage must be protected as a high-value security domain rather than treated solely as operational infrastructure.
- Maintain offline, air-gapped or logically isolated backup copies using provider-supported isolation features such as separate accounts, vaults or recovery regions.
- Apply stricter administrative and access controls to backup repositories compared to production storage.
- Configure object lock, WORM or immutable storage settings to prevent unauthorized deletion or modification.
- Use separate accounts, vaults or restricted access boundaries for backup storage resources.
- Restrict automation identities to narrowly defined backup tasks.
- Require dual authorization or multi-administrator approval for destructive backup changes.
- Regularly test restore procedures through scheduled recovery exercises.
- Continuously monitor backup environments and alert on deletion attempts, retention changes or anomalous activity.
Maintain the integrity of backup logs by sending them to centralized logging platforms that can enforce immutable retention.

Reduce cloud storage control-plane fragmentation
When each cloud storage service provides its own management interface and policy engine, hybrid and multi-cloud storage management becomes more complex. When storage resources are managed independently across providers or accounts, administrative visibility decreases and configuration drift becomes more likely. Reducing control-plane fragmentation improves visibility and helps maintain consistent security enforcement across all storage environments.
- Adopt management tools that aggregate visibility across cloud storage services and provide centralized reporting.
- Map replication paths, backup locations and archive tiers to cloud storage resources to improve architectural visibility.
- Apply policy-as-code controls to enforce encryption, retention and access policies consistently.
- Standardize change management workflows for storage configuration and security updates.
- Use infrastructure-as-code to provision and configure cloud storage consistently, securely and repeatably without relying on manual configuration.
- Continuously audit cloud storage configurations to detect policy drift.
Align encryption enforcement with disciplined cloud key governance
Encryption protects cloud storage data only when consistently enforced and supported by strong key governance. Differences in provider defaults, service configurations and key custody models can weaken protection if not centrally managed.
- Require encryption at rest across all cloud storage tiers.
- Require encrypted connections for management access and data transfers.
- Verify encryption enforcement across primary storage, replication targets, archive tiers and backup repositories.
- Store backup encryption keys separately from backup data and restrict key management access.
- Integrate storage services with enterprise key management or cloud key management system platforms.
- Rotate and expire encryption keys on defined schedules and document the schedule for audit purposes.
- Forward key access logs to monitoring platforms capable of detecting anomalous key usage or unauthorized access.
- Apply consistent immutability and retention protections to backups and archival storage.
Conclusion
As organizations expand their storage across multiple cloud providers, fragmented visibility, inconsistent governance and uneven policy enforcement can amplify security risks. By standardizing how cloud access is governed, how activity is monitored and how recovery pathways are protected, organizations can limit configuration drift, reduce administrative complexity and improve their ability to detect and respond to security threats. Over time, consistent governance and automation can grow cloud storage from a collection of independently managed services into a resilient, centrally governed data platform capable of supporting both security and compliance objectives at scale.
Margaret Rouse is an award-winning writer and technologist known for her ability to explain the value of emerging technology to business users.







