
zagandesign - Fotolia
How easy is a Veritas Backup Exec 16 upgrade from another version?
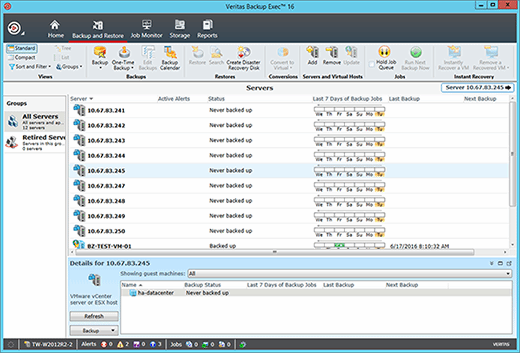
With the right planning, transitioning to Backup Exec 16 from an earlier version can be smooth sailing, preserving data directories and retaining most settings.
Veritas Technologies has made the process of a Backup Exec 16 upgrade relatively easy. In-place upgrades are possible as long as an organization is using version 2010 R3 or higher, and is not running Backup Exec on a 32-bit OS.
Organizations running an earlier version of Backup Exec can theoretically still perform an in-place upgrade if Backup Exec is running on a 64-bit OS, but a multistep upgrade would be required. This means the organization would have to perform a preliminary upgrade to version 2010 R3 or higher, and then a secondary Backup Exec 16 upgrade.
When performing an in-place upgrade, Backup Exec preserves all of the catalogs and data directories from the previous version, unless you opt to remove them. The upgrade process also retains most of the previous version's settings, with the exception of custom filters and custom descriptions of managed media servers and remote agents. Support for these features was discontinued in Backup Exec 2012.
When planning a Backup Exec 16 upgrade, there are two main steps. First, you need to determine the licensing requirements. The technique used in the license verification process varies depending on the version of Backup Exec you are running.
The next step is to clean up your existing Backup Exec deployment. Veritas recommends running a database maintenance job and deleting any job histories and catalogs you won't need in the future.
It is also important to install any available updates for your current Backup Exec version before attempting an upgrade.
If you are performing a Backup Exec 16 upgrade from version 15, you should also view the video Veritas created to demonstrate the process.







