11 DevSecOps best practices to prioritize in 2026
DevSecOps is a strategic shift to make security a shared responsibility across the lifecycle, with best practices covering automation, compliance, collaboration and risk reduction.
Many IT leaders see DevSecOps as merely a technical project. In reality, it's a business-wide, strategic approach that reshapes how organizations integrate security and development.
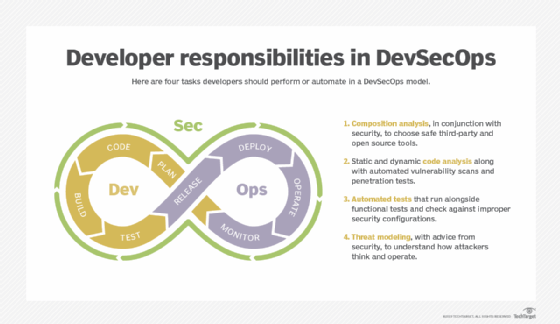
DevSecOps builds on DevOps by making security a shared responsibility across the entire software lifecycle, from development to deployment to operations. Although DevOps improved speed, it often left security unmanaged until late in the development cycle.
The shift to cloud-native architectures, rising cybersecurity risks and expanding regulatory pressure demand better software security integration. An effective DevSecOps practice requires executive leadership to provide the direction and resources needed to succeed.
This article covers key operational practices, essential metrics and common pitfalls for an effective DevSecOps transition.
Core DevSecOps best practices
The following best practices help IT leaders guide organizations toward the cultural and operational changes needed for a DevSecOps framework.
1. 'Shift left' and embed security early
Shifting security left means adding security earlier in development, including during planning, architecture and coding. Practices that aid in this process include threat modeling, establishing secure coding standards and early vulnerability scanning.
This article is part of
What is DevOps? Meaning, methodology and guide
This delivers benefits such as reduced remediation costs, vulnerability avoidance and secure but speedy delivery.
2. Map DevSecOps to compliance frameworks
Various DevSecOps frameworks exist to help structure practices. Examples include these frameworks:
- NIST Secure Software Development Framework or Cybersecurity Framework 2.0.
- ISO 27001.
- System and Organization Controls 2.
- PCI DSS.
Automating audit data is a key part of these frameworks.
DevSecOps frameworks simplify compliance and improve the enterprise's security posture.
3. Integrate infrastructure-as-code security
Programmable infrastructure supports secure and stable DevSecOps practices.
Best practices include the following:
- Scanning templates for policy violations.
- Enforcing secure configurations automatically.
- Embedding infrastructure policies directly into CI/CD pipelines.
These practices help prevent misconfigurations and the breaches that often follow them.
4. Automate security across the pipeline
Automated security tests in CI/CD pipelines reduce manual work, errors and delays.
This can include the following examples:
- Static application security testing.
- Dynamic application security testing.
- Software composition analysis.
- Infrastructure and container scanning.
Integrated security testing also scales effectively as projects grow.
5. Foster cross-functional ownership
DevSecOps removes traditional silos among development, security and operations.
Encourage these practices in your team:
- Shared planning of development projects.
- Shared KPIs to measure progress.
- Security champions within development teams.
- Strong collaboration between engineering and security teams.
Don't underestimate the positive effect of this collaboration. Build clear communication and cross-functional leadership.
6. Standardize and secure toolchains
Manage security and test tools effectively to avoid wasted licensing and user fatigue:
- Consolidate development and security tools to reduce complexity and risk.
- Ensure toolchains support identity management, access control and auditability.
- Standardize to improve visibility and reduce shadow tooling -- the use of nonauthorized tools.
7. Secure the software supply chain
Modern applications use open source libraries, third-party APIs and container images. Carefully control this supply chain to reduce the risk of compromised components entering production.
Controls include the following:
- Maintaining a software bill of materials.
- Scanning dependencies for vulnerabilities.
- Verifying artifact integrity and provenance.
- Using trusted package repositories.
- Maintaining effective version control.
8. Implement secrets management and identity controls
Hardcoded credentials remain a major security risk in development pipelines. DevSecOps calls for effective secrets and identity management, including these practices:
- Secure vaults for credentials, API keys and tokens.
- Automated secrets rotation.
- Least-privilege access for developers and automation tools.
- Short-lived credentials for pipelines and containers.
This significantly reduces the risk of compromised credentials.
9. Implement continuous monitoring and feedback
DevSecOps extends beyond deployment. Continuous monitoring feeds data to development pipelines, strengthening code, improving controls and preventing recurring issues. Monitoring applications, infrastructure and user activities quickly exposes vulnerabilities, misconfigurations and emerging threats.
10. Adopt policy-as-code governance
Policy-as-code codifies security and compliance requirements directly into development pipelines. It helps ensure consistent enforcement of governance standards without impeding development speed.
Consider these policy examples:
- Automatically validating compliance requirements.
- Automatically enforcing configuration policies.
- Blocking deployments that violate security controls.
11. Establish security champion programs
Embed security champions into development teams to highlight issues and improve communication.
Security champions handle these important tasks:
- Serve as the first line of security guidance within development teams.
- Help translate security requirements into developer-friendly practices.
- Accelerate vulnerability remediation.
- Help smooth secure coding adoption.
Measuring DevSecOps success
Measure DevSecOps success by business and security outcomes. Executives must tie technical metrics to business value, such as the following:
- Reduced breach risk.
- Reduced financial exposure.
- Faster product innovation.
- Improved regulatory readiness.
- Increased customer trust.
Accomplish this by tracking specific measures, including these:
- Risk reduction metrics:
-
- Number of critical vulnerabilities in production.
- Mean time to remediate.
- Delivery metrics:
-
- Deployment frequency.
- Lead time for changes.
- Operational resilience:
-
- Incident detection and response times.
- Percentage of automated security testing.
DevSecOps should enable both speed and security, not trade one for the other.
Common pitfalls to avoid
Transitioning to a DevSecOps culture means integrating it into the enterprise's long-term strategy. It's essential to get certain things right. Watch out for the following pitfalls.
Treating DevSecOps as a technology project:
- DevSecOps is a fundamental cultural and operational shift, not a one-time project.
- It requires leadership alignment and cross-team accountability.
Overtooling without process change:
- Buying multiple security tools without integrating them into workflows results in alert fatigue and poor ROI.
Ignoring change management:
- Teams must adapt to new workflows and responsibilities.
Failing to invest in training:
- Developers require training in secure coding standards.
Conclusion: Executive priorities for the first 90 days
Focus on these priorities in the first 90 days of adopting DevSecOps practices:
- Align the strategy. Define objectives tied to risk reduction and delivery speed.
- Assess the current maturity of development practices. Evaluate existing pipelines, tooling and team structure.
- Establish cross-functional governance. Bring together development, security and operations leaders.
- Prioritize automation and quick wins. Integrate security scanning into the CI/CD pipeline.
- Consider external expertise. External partners, consultants or managed security providers can help accelerate implementations.
DevSecOps succeeds when organizations require shared responsibility for security across the entire software lifecycle using measurable, repeatable pipelines.
Damon Garn owns Cogspinner Coaction and provides freelance IT writing and editing services. He has written multiple CompTIA study guides, including the Linux+, Cloud Essentials+ and Server+ guides, and contributes extensively to Informa TechTarget, The New Stack and CompTIA Blogs.








