Ansible vs. Chef vs. Puppet: A comparison
For teams that oversee ecosystems and software packages, configuration management tools have the power to boost operational consistency. But which products deserve attention?
Consistent configurations enable the many machines, servers and applications across an organization to function properly. Effective configurations also bolster security and performance.
A configuration management tool thus is important to IT operations. But how do you evaluate your options?
Many IT teams can agree on some common principles. Core features must be intuitive to use. Tools must include meaningful visualizations. Automation is a critical ingredient in the mix, as manual methods are time-consuming and error-prone. Configuration management tools also potentially shield companies from compliance troubles by documenting everything.
In general, a configuration management tool does the following in an enterprise IT environment:
- Pushes updates and patches to applications and environments.
- Modifies key sets of configurations.
- Scans systems to inspect loaded software versions.
The best configuration management tools have most or all of this functionality included.
Here's a look at three popular configuration management products, and considerations for how to choose between them. Each tool is available as a standalone product with professional support, while community support may also be available. They include Ansible from Red Hat, Progress Chef and Puppet Enterprise from Perforce.
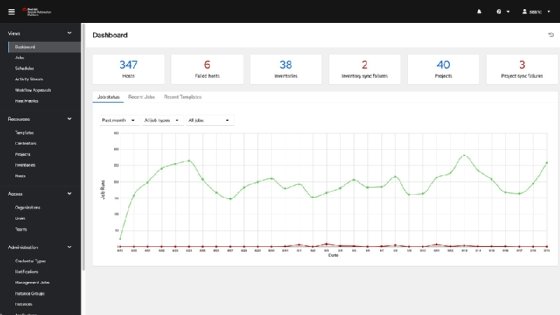
Ansible from Red Hat
Ansible is an open source tool from Red Hat for automating configuration management, infrastructure provisioning and application deployment. Ansible is written in Python and uses YAML formatting to describe desired configurations. It's agentless, meaning it doesn't require any software installed on the endpoints it manages.
Ansible offers tight integration with the Red Hat ecosystem, a benefit for organizations that deploy applications on platforms such as Red Hat Enterprise Linux. That said, Ansible can also run on all other major Linux distributions, as well as other Unix-like OSes including macOS, FreeBSD and Solaris. Ansible offers Playbooks -- templates to define and execute repeatable workflows.
Ansible also avoids error-prone scripting approaches by working toward desired states. For example, if the computers within a network aren't updated to reflect an OS version or include key applications, the software automatically remedies this issue. Other configuration managers might show the path necessary to achieve the same thing, but that puts the onus on IT teams, adding a task instead of removing one. In this sense, Ansible offers the benefit of a more hands-off approach to operations once a workflow deploys.
Ansible can't run on Windows, although you can use it to manage Windows-based servers. Some developers also find Ansible's data structures and control flows complex, which can result in a steep learning curve for the tool.
Chef infrastructure management
The infrastructure management products from Chef are made to deploy automation across cloud ecosystems, physical ecosystems or VMs. Chef cookbooks are automated, repeatable routines, similar to Ansible Playbooks. A central workstation pushes instructions and more information to a distribution server, which then passes those actions onward to targeted systems. Target systems can be remote or local. The system works as a central node communicating to these destination nodes. Chef functionally lives on the server, though automations are established via the central node.
Chef is part of Progress, an application development and digital experience technologies vendor. It's also open source. Chef is configurable via Ruby and uses procedural language. Chef's AIOps support opens the door for third-party integrations -- including platforms such as Datadog, Kubernetes, Terraform and Splunk -- as well as major cloud providers. Integrations can make it easier for users to scale with greater visibility.
Advantages of Chef include its agent-based approach, which helps nodes operate as autonomous actors after setup. Chef targets agent-based operation as a fit for security-focused companies in verticals such as finance, healthcare, insurance and government.
Some engineers see Chef's agent-based model as a drawback of the product because it can lead to slower workflows than an agentless design. Some also report that Chef cookbooks can be challenging to work with because they can require more oversight and troubleshooting during execution.
The tool also offers advantages related to scalability as organizations -- and their networks -- expand. Since these changes and others might introduce inconsistencies, remediation is needed. With Chef, teams can execute changes automatically, though they also have the option to test critical changes prior to implementation. Chef says these dry runs help prevent errors or assess viability.
Chef supports configuration control on Microsoft Azure, AWS, Google Cloud and other infrastructures. Chef officially supports the following OSes and platforms:
- Unix (AIX and Solaris) and Unix variants (macOS and FreeBSD).
- Linux distributions including Amazon, CentOS, Debian, Oracle Enterprise, Red Hat Enterprise, SUSE Server and Ubuntu LTS.
- Microsoft Windows.
In addition to officially supported options, the Chef community provides unofficial OS-support packages, which are acknowledged within the tool's documentation. These include non-LTS versions of Ubuntu, Arch Linux, Fedora, openSUSE and Windows Server (semiannual channel). Teams that maintain ecosystems using any of these OSes can do so successfully, but organizations that oversee sensitive information should evaluate their options.
Puppet Enterprise
Puppet Enterprise is another configuration management tool that champions simplicity. It works with existing automation code, which enables developers and IT professionals to use Puppet without the steep learning curve common with new software.
Service stability and reliability are two chief focus areas of Puppet Enterprise. Automation management in this case centers on reducing the need for remediation, though Enterprise will show users what needs fixing. Puppet aims to have users commit more changes that work effectively, reducing errors. Puppet Enterprise sends configurations to servers within the managed environment. From there, it can push changes to other downstream machines. If a configuration changes, Puppet defers to the predetermined configuration on the host machine.
Like Chef, Puppet Enterprise uses infrastructure as code. The tool also supports state enforcement akin to Ansible, which offloads any core oversight tasks to defined automations.
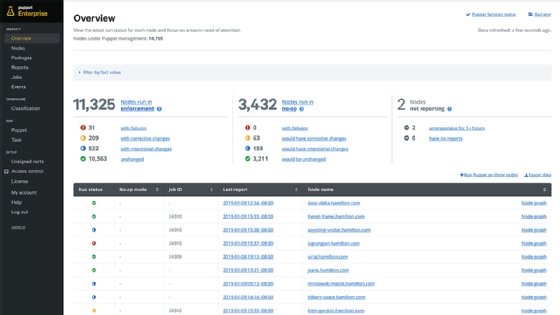
Puppet Enterprise can connect to any device locally or remotely. Those devices can also run almost any modern OS or distribution. To keep certain functions safeguarded, Puppet institutes role-based access controls.
Puppet uses the Puppet declarative language to write manifests, which describe how resources should be configured. However, tasks -- meaning actions executed on a target device -- can be written in diverse languages such as PowerShell, Bash, Python, Ruby and YAML.
Puppet's configurations are considered declarative, following the same state management mantra shared by other configuration management tools. Users can also code automations using Puppet's proprietary domain-specific language.
A common complaint about Puppet is that the tool can be complex and hard to use, which might make it a poor fit for smaller-scale or simpler environments that won't take advantage of all of Puppet's advanced features. Puppet also primarily uses an agent-based architecture, which can lead to slower performance and higher resource consumption than agentless configuration management tools. Agentless management is available for certain use cases, for example with Agentless Catalog Executor or Bolt to run Puppet jobs. Puppet also has less robust support for Windows than for Linux and other Unix-like OSes, although Puppet's Windows capabilities have improved significantly in recent years.
Note: The previous version of this tools comparison article included SaltStack, which offered a supported version of the open source Salt project. In 2020, SaltStack was acquired by VMware. In turn, Broadcom acquired VMware in 2024. SaltStack is no longer offered as a standalone product comparable to the above configuration management tools.
How to choose between Ansible, Chef and Puppet
When comparing configuration management tools, consider the following:
- Which operating systems you need the tool to run on. As noted previously, some options don't run on Windows or offer limited Windows support.
- Which languages the tool supports or requires. If you prefer one language over another, such as Python over Ruby, this might help inform your decision about which tool to choose.
- How important performance is. If you need workflows to execute as quickly as possible and with minimal resource usage, you might want to stick with an agentless platform, which typically performs better, but might also offer less control.
- The tool's setup process and learning curve. In general, more powerful configuration management tools are more difficult to set up and master. Conquering the learning curve might be worth it if you need advanced capabilities. Conversely, stick with a simpler platform for simpler use cases.
- Scalability of the tool. Some tools are more adept than others at supporting very large environments.
- Interoperability. Check with any short-listed configuration management tool vendors for their list of integrations to cross reference with your IT environment.
| Ansible | Chef | Puppet | |
| Vendor/owner | Red Hat | Progress Software | Perforce |
| Agent-based or agentless? | Agentless | Agent-based | Primarily agent-based (agentless option available through Puppet Bolt) |
| Primary programming language(s) | Python, YAML | Ruby | Custom declarative language |
| Supported OSes | Most Linux and Unix-like systems Doesn't run on Windows, but can manage Windows hosts |
Most modern Windows, Linux and Unix-like systems Official support is limited to certain Linux distributions, but unofficial community support is available for others |
Most modern Windows, Linux and Unix-like systems Windows support isn't quite as extensive as for Linux and other Unix-like systems |
| Key advantages | Relative simplicity Ability to work automatically toward desired state even when state isn't fully achievable Integration with Red Hat ecosystem Playbooks feature |
High scalability Ruby-based configuration is arguably simpler than using languages like YAML |
High scalability Support for desired-state automation |
| Key drawbacks | Doesn't run on Windows Might not operate well at high scale |
Performance can be slower due to agents Cookbooks can present challenges |
Complex tool that comes with a high learning curve Somewhat limited Windows support |
Choosing the right configuration manager doesn't mean an organization must seek out the best tool on the market. What works for one company might be wrong for a different company.
Every configuration management tool, including Ansible, Chef and Puppet, caters to specific organizational goals and preferences. Ansible and Puppet, for instance, are agentless; Chef isn't.
If an organization has rigid OS requirements, that dictates which tools to evaluate and which to cross off the list.
Some of the IT tool selection process is about comfort, not architectural fit. Consider programming languages. A team that's not skilled in Python, for example, might not be as comfortable with Ansible as one that knows that language well. If PowerShell is of high importance to your team, you'll probably want Puppet Enterprise on your short list. The strengths and competencies of a team should determine which configuration product is the best fit.
Editor's note: This article was written in 2020 by Adam Bertram. In 2024, Chris Tozzi updated and expanded the information, including updated product specs and information on company roadmaps. Both authors are independent DevOps and IT experts.
Adam Bertram is a 20-year veteran of IT and an experienced online business professional. He's an entrepreneur, IT influencer, Microsoft MVP, blogger, trainer and content marketing writer for multiple technology companies.
Chris Tozzi is a freelance writer, research adviser, and professor of IT and society who has previously worked as a journalist and Linux systems administrator.







