How to create an enterprise mobile device management policy
An MDM policy helps organizations secure corporate, BYOD and hybrid workforce devices by defining acceptable use, data protection, privacy and enforcement standards.
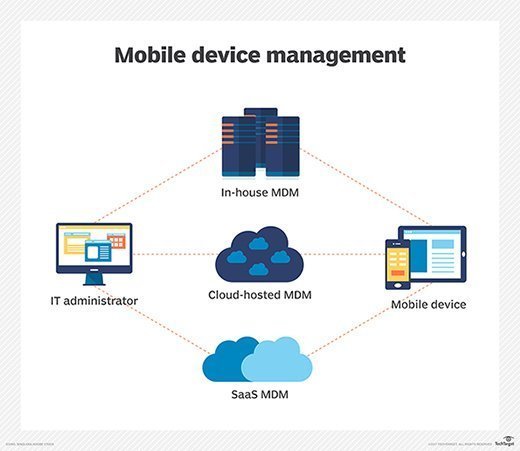
An effective mobile device management (MDM) policy is essential for organizations managing corporate, BYOD and hybrid workforce environments.
Creating an MDM policy is a foundational step toward protecting organizational data, endpoints and IT infrastructure. It helps secure data, clarify acceptable use and privacy standards, and still enable end users to remain productive on their devices.
An MDM policy should guide how end users can use and manage any mobile devices within the organization. As part of the MDM policy, IT must consider issues such as acceptable use of mobile devices, security measures, end-user privacy and other policies relating to data access and application usage.
When developing an MDM policy, it's important to collaborate with stakeholders across the organization. This helps ensure that everyone is on the same page regarding expectations on how to use mobile devices at work.
In modern enterprise environments, MDM policies are increasingly aligned with broader unified endpoint management (UEM) and zero-trust security strategies. Read on to find out what MDM policies include, why they're important and how to create one for an organization with practical examples.
What is a mobile device management policy?
A mobile device management policy is an organizational document that outlines rules and procedures for using company-issued or personally owned devices. It details which activities are acceptable on the device and any associated consequences for not following the policy.
These guidelines can include restrictions on downloading certain apps and access to sensitive data, password-strength requirements, rules for cellular data access and consumption if using corporate data plans, data protection and other security measures. A comprehensive MDM policy should also include guidelines for devices that are lost or stolen, and standards for data removal and device return if an employee leaves.
Enforcement of a mobile device management policy is critical to its success. An effective enforcement strategy should include methods for monitoring user compliance and consequences for inappropriate behavior. For example, if someone downloads unauthorized apps or accesses sensitive data, an IT admin might quarantine them, revoking access to corporate apps and data. In some circumstances, they might lose access to certain features or services entirely or, in more severe cases, have the device remote wiped and factory reset to ensure data security. These ramifications can help ensure all users are accountable, discouraging potential device misuse.
Importance of an MDM policy
Organizations can reduce risks associated with unauthorized access or misuse of company resources by setting clear expectations around device usage. MDM policies provide guidelines on how employees should use corporate and personal mobile devices and determine what activities are permitted while connected to corporate apps and networks. They also include rules and procedures for the secure storage and transmission of confidential information, such as passwords and sensitive customer data, end-user privacy, device management, security and access.
Additionally, an MDM policy can help avoid unexpected tech support needs due to a lack of user understanding or awareness of the policy. By setting clear rules and enforcing them effectively, organizations can protect corporate resources and ensure their employees use mobile devices responsibly.
MDM policy privacy considerations
User privacy is a significant factor to consider when creating an MDM policy. In particular, organizations must address this concern when outlining policies for personal or BYOD endpoints. If a device is used for both work and personal purposes, users expect some degree of freedom and privacy with regard to the personal apps and data. These scenarios make MDM policies all the more necessary. At the same time, an MDM policy can raise employees' concerns if it doesn't include clear privacy information.
An effective policy should explain what data the organization can and cannot access, how that data is used and the safeguards in place to protect personal data. Employees should understand that IT might collect device identifiers, security posture and network activity related to corporate resources, but not personal content such as photos, personal emails, text messages or browsing history.
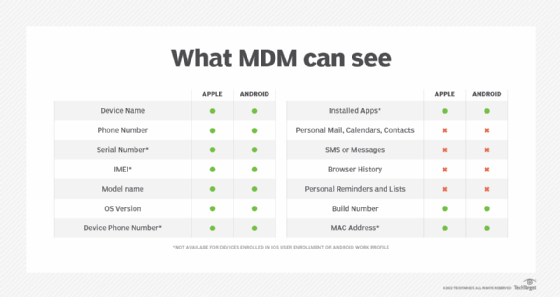
Other privacy considerations include transparency around monitoring practices, data retention and the mechanisms that separate personal and corporate data. The policy should also specify how guidelines might change based on the device ownership scenario. In BYOD environments, the policy should emphasize that corporate controls, such as remote wipe or access restrictions, apply only to corporate data and apps.
Common MDM policy examples
Organizations can use several different types of MDM policies, but not every approach is well-suited to every organization.
Access control
Identity and access management policies and tools set the parameters for users to connect to company networks and access data on mobile devices. This ensures that only authorized personnel can access sensitive data or systems. Additionally, access control policies can cover cellular data usage and consumption.
Data security
Data security policies set the rules around how corporate data should be stored, accessed and managed on mobile devices to prevent unauthorized use or information transfer. IT can set restrictions on what types of data and apps can be stored and installed on employee devices, as well as what apps can access and share that data. These policies also cover how organizations enforce encryption and PIN code access to secure data.
Software update
These policies help IT departments ensure mobile devices remain up to date, secure and running smoothly. They also include rules about how often IT should update device software.
Device management
Device management policies help IT determine and enforce security measures that protect the device's hardware and operating system. These security measures could include implementing encryption, PIN code access and certificate-based authentication. Other measures might include limiting of a device -- such as removing access to capabilities like iCloud backup or camera use -- based on the device's use case.
Privacy policies
These policies define the rules around collecting and using user data from personal or corporate devices. Privacy policies are important as they show users how the corporation is accessing and monitoring data on their devices.
By creating and enforcing MDM policies, IT departments can ensure data security, device management, access control, end-user privacy and compliance with company regulations. This is essential for both security and employee productivity.
5 steps to create an MDM policy for the organization
While every organization should customize its MDM policy to suit individual needs, there are five broad steps that IT teams can follow for success.
- Start with a clear purpose and scope. Before writing the policy, it's important to ensure everyone involved in creating and enforcing it understands its necessity and intended scope. Make sure to consider any applicable local laws and regulations as well.
- Identify key stakeholders. Identify who will oversee the policy, who will be affected by its implementation and any other stakeholders who should consult on the process.
- Develop rules for mobile device usage. Create regulations covering all aspects of mobile device usage, including the standard MDM policies and details on acceptable use, security requirements, data handling procedures and more.
- Establish an enforcement process. Develop a clear plan for addressing policy violations and what disciplinary action to take if necessary.
- Implement, review and update. After creating the MDM policy, ensure leadership communicates its specifics to everyone affected. Additionally, periodically review and update the policy to ensure it effectively protects the business or organization's interests.
Best practices for creating an effective MDM policy
For the most effective implementation, IT teams can follow a few best practices throughout the policy creation process.
- Align the policy with broader security frameworks. Ensure the MDM policy supports existing UEM, zero‑trust and identity‑based access strategies.
- Differentiate clearly between corporate‑owned and BYOD devices. Spell out how requirements, monitoring and controls differ based on device ownership status.
- Use the principle of least privilege. Grant only the minimum access necessary for users and devices to perform their work.
- Standardize security baselines across device types. Define consistent expectations for encryption, authentication, OS versions, patching and app permissions, regardless of platform.
- Automate enforcement where possible. Use MDM and UEM tools to automate compliance checks, remediation actions, conditional access and device quarantine.
- Plan for the full device lifecycle. Include onboarding, configuration, management, incident response, offboarding and secure device return procedures.
- Review and update regularly. Revisit the policy as platforms evolve, new threats emerge and regulatory requirements change.
Real-world MDM policy use cases
Organizations across industries use MDM policies to solve challenges related to security, compliance and workforce mobility. These examples show how policies translate into day‑to‑day operations.
- Healthcare organizations. Hospitals use MDM policies to enforce encryption, restrict unauthorized app installations and block noncompliant devices from accessing electronic health records. IT can remotely wipe lost or stolen devices to maintain HIPAA compliance.
- Shared-device and shift-based environments. Frontline workers often rely on shared corporate devices. MDM policies define kiosk modes, limit access to approved apps and prevent the storage of personal data on shared endpoints.
- Organizations supporting hybrid and remote work. Organizations with distributed teams use MDM policies to secure VPN access, enforce conditional access rules and ensure personal devices meet minimum security standards before accessing corporate apps.
An MDM policy is more than just a technical document; it is a governance tool that sits at the intersection of security, privacy and endpoint strategy. As organizations support hybrid work, BYOD programs and increasingly identity-driven access models, mobile devices are no longer peripheral endpoints but part of the broader enterprise attack surface.
For IT leaders, the goal is to establish clear, transparent expectations about what IT can manage, what data is protected and where employee privacy boundaries exist. Policies that reflect modern MDM and UEM capabilities help reduce user friction, improve compliance and make enforcement more predictable across diverse device types.
Ultimately, the most effective MDM policies are living documents. They should evolve alongside platform capabilities, regulatory expectations and workforce mobility trends. This ensures organizations can protect corporate data while enabling employees to work productively across personal and corporate devices.
Editor's note: This article was updated in March 2026 to improve the reader experience.
Michael Goad is a freelance writer and solutions architect with experience handling mobility in an enterprise setting.







