santiago silver - Fotolia
Which SD-WAN security concerns should I tackle first?
IT teams thinking about software-defined WAN technology should assess a few SD-WAN security concerns before deployment to make sure it's worth the investment.
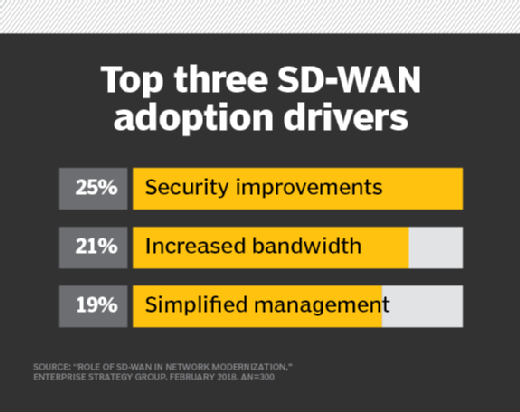
Software-defined WAN is one of those technologies that, despite it being relatively complicated, is more secure when compared with legacy MPLS or site-to-site VPN tunnels. Because of SD-WAN's end-to-end visibility, centralized configuration and encryption requirements, vendors tout security as one of its primary benefits.
That said, it's important to consider a couple of SD-WAN security concerns when evaluating your options.
- Decide whether you want to use an SD-WAN service provider. The first SD-WAN security concern to address is whether you want to design, deploy and manage the SD-WAN yourself or let one of the many SD-WAN service providers do it for you. If you opt to go with a managed service provider, you place the responsibility for your WAN infrastructure in the hands of a third party. On the other hand, if you don't have the right in-house SD-WAN expertise, you may introduce holes in your WAN that can be exploited.
- Integrating security tools at the WAN edge. To address some customer SD-WAN security concerns, different SD-WAN technology vendors offer varying degrees of added security beyond simple encryption. This includes Layer 7 firewalls, intrusion prevention and unified threat management. Integrating these security tools at the WAN edge ensures data flowing between the corporate network and branch locations isn't compromised.
- Evaluate the need for added SD-WAN security features. Keep in mind that most enterprise LANs already have these standard security tools in place. It's up to the SD-WAN architect to determine if add-on SD-WAN security features offered by some platforms are worth the extra investment to license, configure and support.