Address Resolution Protocol (ARP)
What is Address Resolution Protocol (ARP)?
Address Resolution Protocol (ARP) is a protocol that maps dynamic IP addresses to permanent physical machine addresses in a local area network (LAN). The physical machine address is also known as a media access control (MAC) address.
ARP translates 32-bit addresses to 48-bit addresses and vice versa, which is necessary because IP addresses in IP version 4 (IPv4) are 32 bits but MAC addresses are 48 bits.
ARP works between Layer 2 and Layer 3 of the Open Systems Interconnection model (OSI model). The MAC address exists on Layer 2 of the OSI model, the data link layer. The IP address exists on Layer 3, the network layer.
ARP can also be used for IP over other LAN technologies, such as token ring, Fiber Distributed Data Interface and IP over Asynchronous Transfer Mode.
How ARP works
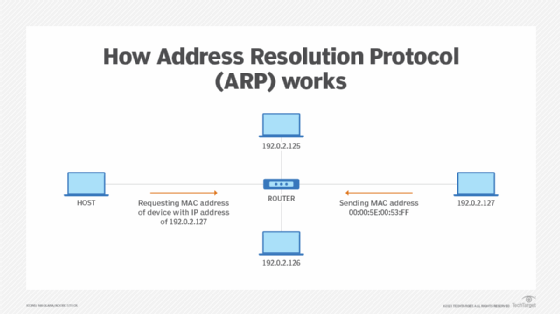
When a new computer joins a LAN, the network assigns it a unique IP address for identification and communication. When an incoming packet destined for a host machine on a particular LAN arrives at a gateway, the gateway asks the ARP program to find a MAC address that matches the IP address. The ARP cache table maintains a record of each IP address and its corresponding MAC address.
All operating systems in an IPv4 Ethernet network keep an ARP cache. Every time a host requests a MAC address to send a packet to another host in the LAN, it checks its ARP cache to see if the IP to MAC address translation already exists. If it does, a new ARP request is unnecessary. If the translation doesn't already exist, ARP performs the request.
ARP broadcasts a request packet to all the machines on the LAN and asks if any of the machines are using that particular IP address. When a machine recognizes the IP address as its own, it sends a reply so ARP can update the cache for future reference and proceed with the communication.
Host machines that don't know their own IP address can use the Reverse ARP protocol for discovery.
ARP has a limited cache size, and ARP periodically cleanses entries to free up space. Addresses tend to stay in the cache for only a few minutes. Frequent updates enable other devices in the network to see when a physical host changes their requested IP addresses. When ARP cleanses its cache, it detects unused entries along with any unsuccessful attempts to communicate with computers that aren't currently powered on.
Proxy ARP
Proxy ARP enables a network proxy to answer ARP queries for IP addresses that are outside the network. This enables the successful transfer of packets from one subnet to another.
When ARP broadcasts an inquiry packet, a router examines the routing table to find which device on the LAN can reach the destination fastest. This device, which is often also a router, acts as a gateway for forwarding packets outside the network to their intended destinations.
ARP spoofing
LANs that use ARP are vulnerable to ARP spoofing, also called ARP poison routing or ARP cache poisoning.
ARP spoofing is a device attack in which a hacker broadcasts false ARP messages over a LAN to link an attacker's MAC address with the IP address of a legitimate computer or server within the network. Once a link has been established, the target computer can send frames meant for the original destination to the hacker's computer first, as well as any data meant for the legitimate IP address.
ARP spoofing can have unfavorable effects on an enterprise. In their simplest form, ARP spoofing attacks can steal sensitive information. However, the attacks can also facilitate other malicious attacks, including the following:
- Man-in-the-middle attacks.
- Denial-of-service attacks.
- Session hijacking.
History and future of ARP
ARP was first proposed and discussed in Request for Comments 826, published in November 1982 by David C. Plummer. The problem of address resolution was immediately evident in the early days of the IP suite because Ethernet quickly became the preferred LAN technology but Ethernet cables required 48-bit addresses.
IP version 6 (IPv6) addresses, which are 128 bits, use the Neighbor Discovery protocol acquire configuration information instead of ARP. While IPv4 addresses are currently more common, the use of IPv6 is increasing, largely due to the influx of internet of things devices that require IP addresses. Neighbor Discovery operates in the Layer 2 of the OSI model and uses Internet Control Message Protocol version 6 to discover neighboring nodes.
Editor's note: This definition was reformatted to improve the reader experience.





