
Getty Images
IPv4 vs. IPv6: What's the difference?
IPv4 and IPv6 are two forms of IP addresses, but they differ in length and style. Compare the two, and find out why organizations might implement one over the other.
IP is a mechanism used to logically identify devices at the network layer of the TCP/IP model. Each device on an IP network must have a unique IP address, subnet and default gateway to perform intersubnet or intervirtual LAN communication by way of routing.
Devices on the internet currently use one of two versions of IP addresses: IPv4 or IPv6. Let's compare how these two addressing types differ.
What is IPv4?
The fourth iteration of IP, known as IPv4, emerged in the early 1980s, evolving from the Advanced Research Projects Agency Network, or ARPANET, initiative that introduced TCP and IP. IPv4 remains the most popular version of IP, both within enterprises and across the internet.
IPv4 addresses use a 32-bit dotted-decimal format broken into four quadrants. The address specifies the subnet and unique address within the 32 bits. The network address and host address allocations vary depending on the subnet mask used.
For example, in the IPv4 address 192.0.2.2, the first three quadrants, 192.0.2, specify the network ID. The final quadrant -- .2 -- indicates the device's unique host ID. A gateway address is also part of the addressing process and indicates to which router address the device should send traffic from outside the specified network.
The structure of IPv4 limits the number of unique and internet-routable IP addresses to around 4 billion devices. A 2020 Statista report projected that the number of non-IoT devices connected to the internet will reach over 10 billion by 2025. This is more devices than IPv4 can allocate, showcasing an undersupply of publicly routed IPv4 networks.
To counter the shortage, businesses often use private IPv4 ranges. Network professionals can use Network Address Translation (NAT) to map privately addressed devices to one or more publicly addressable IP addresses so these devices can communicate across the internet.
IPv4 benefits include the following:
- connects devices to the internet;
- enables simple management due to existing IP infrastructure; and
- supports NAT to create private IP addresses.
What is IPv6?
Version six of IP has been around since the late 1990s, when the Internet Engineering Task Force first developed it. IPv6 uses a 128-bit addressing format, which can create up to 340 trillion unique addresses.
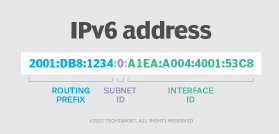
Unlike IPv4 addresses, an IPv6 address format uses eight hexadecimal segments to specify both the network and individual device addresses. IPv6 addresses also include letters within the fields and use colons rather than periods to separate the segments, e.g., 2001:DB8:1234:0:A1EA:A004:4001:53C8.
IPv6 addresses also come with a host of benefits, including the following:
- improved multicasting capabilities;
- simplified IPv6 address autoconfiguration;
- quality of service;
- streamlined routing; and
- built-in encryption and packet integrity checks.
Which IP address format should enterprises use?
For the better part of two decades, experts have debated about IPv4 versus IPv6. Some organizations, such as the American Registry for Internet Numbers, encourage enterprises to migrate to IPv6 to prevent the complete exhaustion of IPv4 addresses.
However, most network architects and administrators are already familiar with IPv4 and use NAT to create private IP addresses, which don't overlap with public IPs. Additionally, most organizations can easily acquire smaller blocks of public addresses. For most organizations, IPv4 remains relevant.
Some organizations, however, prefer not to use NAT because it complicates other aspects of network operations. These organizations might opt to take advantage of the inherent benefits found in a modern IPv6 scheme, and it's likely the most future-proof option.






