visitor-based networking (visitor-based network)
What is visitor-based networking?
Visitor-based networking (VBN) is a computer network with high-speed internet access provided by an organization for temporary use by visitors, guests or other users in a public area. It may also be called a guest network or a public network. These are most often provided through Wi-Fi, though wired Ethernet access may also be provided.
A VBN should be kept separate from a corporate network, often by a virtual local area network (VLAN). Providing a VBN is important for airports, convention centers, malls, shopping centers, restaurants, stores and universities. Many companies offer a VBN for employee's personal devices. Most VBNs will employ a VBN gateway to control access, connect users and filter content.
As more people use smartphones and consume and produce more online content, access to high-speed internet connections is more important than ever. VBNs exist to offer internet connectivity in locations that have poor mobile internet signal service or for users on devices that do not have mobile modems, such as laptops. Locations that cater to corporate customers benefit from offering a VBN.
A VBN can vary greatly in size and cost depending on its intended use and number of supported users. A small store or restaurant with only a few users may have a single simple Wi-Fi router with a guest network and a shared password. A large space with thousands of users may require many access points (APs) connected through switches to a central router and gateway with per-user authentication and EULA acceptance.
What are the types of visitor-based networks?
Several types of VBNs exist depending on the intended use and audience.
Transparent VBN
The purpose of a transparent VBN is to provide easy access to the internet. These are often provided free to use in a public space. They do not require a password or preauthentication but may have a captive portal for users to accept terms and conditions before connecting.
A public VBN will often use a gateway to block certain abusive uses. This may include blocking explicit material, file sharing and blocking access to ports other than those used for web access or email. They may also use timeouts to restrict access after a certain length of time.
Billing VBN
A billing VBN charges users money for access to use its service to access the internet. These are common in locations where it is costly or difficult to obtain internet access. Some examples are for airplane in-flight access or in remote locations.
Historically, paid internet access has been used in airports, convention centers and hotels -- but most of these locations now offer free VBN to guests as part of their service.
Most commonly, a billing VBN will use a captive portal to collect payment information. These can be bought at the time of use with a credit card or using a prepaid account.
Authentication VBN
An authenticated VBN requires the user to provide credentials or prove identity to use. These are common in a business environment for employees, contractors or guests to connect personally owned devices.
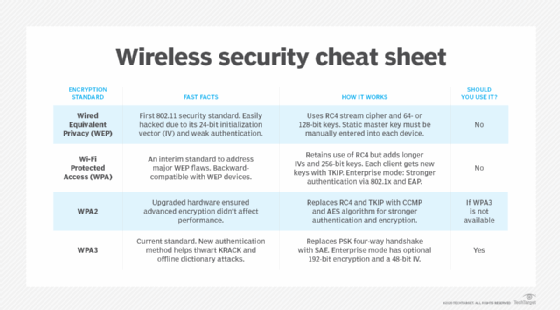
Authentication is usually done by connecting the VBN to another identity provider. This is commonly by using WPA2-Enterprise 802.1x to connect to an Active Directory, LDAP or RADIUS authentication source. (WPA stands for Wi-Fi Protected Access).
What are uses, benefits and risks of visitor-based networks?
Uses of VBNs
Providing a VBN is a core service to many businesses. Many restaurants and coffee shops provide free VBN internet to customers to attract remote workers, freelance workers or students to work from their store and build business for their other items for sale. This may also allow customers to access a web menu or ordering system. coworking or shared workspaces must provide a VBN to its customers so that they can conduct business.
Many retail locations provide a VBN as a convenience to their customers. Often large stores or shopping areas may have poor cellphone service; providing a VBN in such places allows their customers to access the internet when they may not be able to. This allows customers to stay longer, or to access the company website to research or purchase items.
Often a captive portal can be used to direct traffic to the vendor. This may also provide access to a web-based map or list of stores and services.
Benefits of VBNs
Wi-Fi 6 and Wi-Fi 6E have many benefits for VBN. These improvements include better sharing of in-use channels and more regular communication times between devices and the access points.
These changes can particularly benefit locations such as sporting arenas and stadiums that may often have poor performance on their guest networks during large events.
Risks of VBNs
A VBN does carry security risks to both the provider and the user of the service. The provider must be careful that the network is properly secured and isolated from the corporate network. Separate VLANs and SSIDs (service set identifiers) may be used to separate the networks. The provider may also be liable for activity that occurs on the guest network and may therefore need to filter what users can access.
VBN users must also be cautious. With the proliferation of public Wi-Fi, some attackers set up networks that appear to offer free internet access but are actually honeypots designed to steal the user's private information. Even if connected to a legitimate VBN, it may open their device to attacks by other user devices on the same network, such as man-in-the-middle, DNS hijacking, cache poisoning, etc.
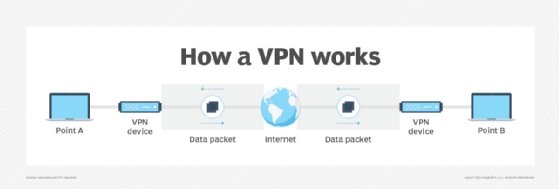
Many people have started using virtual private networks (VPNs) to mitigate some of the risks of connecting to public networks.






