What is a SIM swap attack (SIM intercept attack)?
A SIM swap attack is a form of identity fraud in which the attacker transfers a user's phone number to a different SIM card to gain access to the user's phone calls, text messages, bank accounts, credit card numbers and other sensitive information. This type of attack is also known as a SIM intercept attack or a SIM hijacking attack.
Relatively new and on the rise, SIM swap attacks are increasing in popularity due to the increasing use of cellphones and the growing dependence of users on cellphone-based user authentication. Such attacks are sly because, often, the original user doesn't realize that an attack has occurred until their phone suddenly stops working.
How a SIM swap attack works
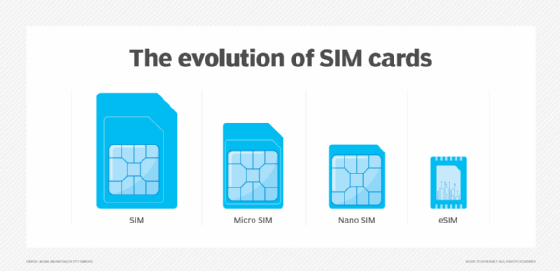
Mobile phone SIM cards are used to store information about its user and to identify and authenticate the mobile phone to a cellular network. Without a SIM card, devices cannot be registered to an account, network or subscription. By compromising the SIM, a SIM swap attack does not affect the programming of the device, but rather it remotely disables the device without the victim's knowledge.
The general process for most SIM swap attacks is as follows:
- The threat actor gets information on the target victim.
- The attacker performs the SIM swap by manipulating the mobile carrier.
- The carrier activates the new SIM.
- The attacker takes control of the victim's phone number.
- The attacker impersonates the victim to access their accounts, steal or reset credentials, or steal cryptocurrency.
The first step in a SIM swap attack is for the hacker to gather as much information about the victim as possible. One way to do this is through phishing. Through fraud emails, phone calls or text messages, hackers trick victims into revealing personal information, such as legal names, birthdates, phone numbers, Social Security numbers (SSNs) and addresses that may be tied to account security. They may also scrape information about potential victims from other sources, such as lists of previously compromised accounts, social media, the internet and the dark web.
A newer tactic used by some attackers is to lure mobile carrier employees to phishing websites. These websites replicate their company's login page but are hosted on attacker-controlled Internet Protocol addresses. When the unsuspecting victim logs in, the hacker can capture the information needed to access internal company systems. They can then target the carrier's customers and swap SIMs at will.
Regardless of how they collect user information, the goal is the same: to fake the victim's identity for malicious and/or financially motivated purposes.
After the attacker has collected enough information to claim the victim's identity, they contact the mobile phone provider to declare the original SIM card has been compromised and they would like to activate a new one in their possession to the same account. Using the personal data previously collected, attackers can usually answer security questions without raising any alarms and complete the transaction.
Once the attacker manages to swap or intercept the SIM, all calls and texts to the user's phone number get redirected to the criminal's phone. Some of these calls and texts may be security-related, such as one-time PINs (OTPs) and verification links. SIM swapping enables the hacker to receive these OTPs and calls to compromise the original user's accounts, such as email, banking, social media and cryptoexchanges.
What can hackers do with a compromised SIM?
SIM swap attacks leave massive amounts of information vulnerable to theft and compromise.
If not caught early on, the attacker could potentially log in to the victim's bank account to steal their funds, lock the victim out of all online accounts, steal additional personal data from those accounts and sell it on the dark web.
Some hackers use SIM swap attacks to perpetrate fraud while hiding behind the victim, causing financial, social or reputational harm to the victim. If the account holder is high profile -- say, a company chief executive officer -- the attacker may threaten to publish the stolen data. They then extort the victim to extort money, embarrass the victim or disrupt their company's operations.
Increasingly, cybercriminals use SIM swap attacks to steal cryptocurrencies like bitcoin. Since cryptotransactions are usually irreversible and pseudonymous, hijacking a SIM card of a phone that's linked to a cryptoaccount enables them to engage in large numbers of such transactions and potentially steal large amounts of cryptocurrency.
How to identify a SIM swap attack
A telltale sign of a SIM swap attack is the discontinuation of cellular service. A sudden loss of signal, as indicated by no bars or on-screen notifications, like "no service" or "emergency calls only," is a common red flag of a SIM swap. If the user's SIM has been swapped without their knowledge, they aren't able to send or receive text messages or make or receive calls with that device. Once the attacker has successfully redirected a phone number, the victim's device practically voids its communication capabilities.
Unusual account activity is another red flag. When a SIM is swapped, users usually receive notifications about login attempts or password resets. Some online accounts also send automatic notifications on detecting new device logins. Ignoring these alerts as mundane or irrelevant could result in the victim getting locked out of the device or losing information.
Account lockouts and unauthorized charges can also indicate a SIM swap. Some users find that they cannot log in to certain accounts, while others realize that they are no longer receiving OTPs and password reset links to their device.
Often, cellphone providers contact users, usually using a text message or email, on detecting a new SIM card or a new device being activated on the user's account. This usually means that the swap was done by someone without the proper authority to do so.
How to prevent a SIM swap attack
Users can protect their cellular devices and accounts from SIM swap attacks by following these best practices:
- Avoid relying on Short Message Service (SMS) for primary communication as the data is not encrypted.
- Remove cellphone numbers from accounts that do not require one and from sensitive online accounts, including cryptoaccounts.
- Avoid sharing personal information online.
- Verify the types of alerts set up for each account to identify false and potentially malicious login attempts.
- Set up an account PIN or passcode separate from the number to prevent account misuse.
- Secure online accounts, including email, social media, credit card and bank accounts, with strong and hard-to-guess passwords; also, change passwords regularly, and never reuse old passwords.
- Watch for suspicious logins from unknown devices or locations -- if a SIM hijacking attempt is suspected, change the passwords for all accounts tied to that phone number.
- Monitor the phone bill; contact the carrier in case of suspicious or unexpected charges.
- Be suspicious of texts, emails and calls from unknown senders that ask for personal or sensitive information, like passwords, PINs, SSNs or credit card details; never act on the message, and delete it -- after forwarding it to the cellphone provider, if possible.
- Use a password manager to securely create, manage and store passwords and other sensitive information.
- Strengthen security, and minimize the potential for account compromise by enabling two-factor authentication.
- Avoid relying on SMS codes, and use app-based authentication using authenticator apps, such as Google Authenticator and Authy, to generate OTPs for authentication of online accounts.
In some countries, cellphone providers allow users to enable a SIM protection security feature. This locks the lines on the user's account so it cannot process a SIM change, including unauthorized and malicious SIM swaps. Only the user or an authorized account manager can disable SIM protection.
With an increase in SIM swap attacks, many telecommunications companies have added new security controls to safeguard user accounts. For example, they may mandate that an OTP must be provided before a new SIM card or device is activated. Even so, SIM swapping is a growing threat, so users also need to be alert to them.
How to respond to a SIM swap attack
Despite using precautions, hacks occur, and users should immediately contact their carrier.
The user should reset passwords for sensitive accounts linked to the swapped-out phone number. It's also important to revoke access to suspicious devices and scan the device for additional viruses, malware or spyware.
It may also be necessary to inform law enforcement. In the case of company-owned devices, both the company's cybersecurity team and law enforcement must be notified. A long-term strategy to adopt is to enable login notifications on all online accounts, as well as fraud alerts on all financial accounts.
Recent real-world SIM swap attacks
In February 2023, the Federal Bureau of Investigation (FBI) published a public service announcement to inform mobile carriers and the public about the dramatically increasing use of SIM swap attacks by criminals to steal money. Between January 2018 and December 2020, the FBI's Internet Crime Complaint Center (IC3) received 320 complaints related to SIM swapping. And, in 2021, IC3 received five times more such complaints.
One recent example of a SIM swap attack occurred in December 2024. U.S. federal authorities arrested and indicted a U.S. Army soldier on suspicion of hacking into the systems of numerous telecommunications firms and advertising SIM swapping services targeting Verizon Push to Talk customers, mainly U.S. government agencies and emergency responders.
Also in 2024, a former manager of a U.S. telecommunications company admitted to swapping the SIMs of the company's cellphone customers with cellphones controlled by another individual, enabling the latter to control the customers' phones. The person received $1,000 in bitcoin per SIM swap for a total of $5,000 in bitcoin. He was also promised by his recruiter that he would receive a percentage of the profits earned from illicitly accessing the victims' mobile devices. The fraud affected five victims in four different U.S. states.
Regulatory landscape to protect against SIM swapping
In November 2023, the U.S. Federal Communications Commission (FCC) announced that it would be implementing new rules to protect cellphone users in the U.S. from SIM swap fraud. This announcement was the FCC's response to the increasing number of consumer complaints received by the agency.
These rules mandate wireless providers to adopt secure authentication methods before transferring a customer's phone number to a different device or service provider. These methods have to accommodate the needs of a broad spectrum of their customers. Additionally, the FCC requires mobile companies to immediately notify customers if any SIM change request is made on their accounts.
Smartphones are being used to address global health concerns, such as sleep apnea and hearing loss. Learn how groundbreaking technology is creating smartphone-based diagnostic tools.
