What is Point-to-Point Protocol over Ethernet (PPPoE)?
Point-to-Point Protocol over Ethernet (PPPoE) is a network protocol that facilitates communication between network endpoints. PPPoE encapsulates Point-to-Point Protocol frames inside Ethernet frames, offering the same benefits as PPP, while providing connectivity across Ethernet networks.
With PPPoE, internet service providers (ISPs) can manage multiple client systems, authenticate their access to their services and track customer data usage. PPPoE also supports services such as data encryption and compression.
What is PPPoE used for?
PPPoE is commonly used by ISPs to deliver internet access services to their customers, typically over broadband connections. Providers offering Digital Subscriber Line (DSL) services implement PPPoE extensively. They use PPPoE to connect multiple hosts on a single Ethernet local area network to a remote site using a common device, such as a cable or DSL modem. The protocol can also support wireless connections to the Internet.
UUNET, Redback Networks (now Ericsson) and RouterWare (now Wind River Systems) developed PPPoE to address PPP limitations and provide an option for organizations that relied on common customer premises equipment to support multihost environments. In February 1999, the Internet Society helped to formalize PPPoE by publishing Request for Comments 2516. This informational specification describes PPPoE and how to build PPP sessions and encapsulate PPP packets over Ethernet.
How does PPPoE work?
Ethernet and PPP do not provide native support for each other, yet they both offer essential benefits for supporting multihost network environments. PPPoE bridges the gap between Ethernet and PPP by facilitating a point-to-point relationship between network peers. A multihost Ethernet environment can use PPPoE to open PPP sessions to multiple destinations using one or more bridging modems.
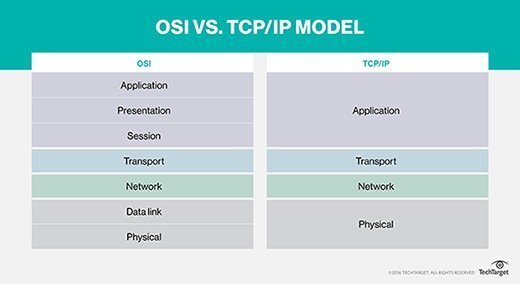
Like Ethernet and PPP, PPPoE operates at the network access layer in TCP/IP and at the data link layer in the Open Systems Interconnection (OSI) model. The protocol is intended for use with remote access broadband technologies that offer a bridged Ethernet topology. With PPPoE, service providers can take advantage of Ethernet's cost-effective benefits and still maintain the session abstraction, access control and billing functionality available to PPP.
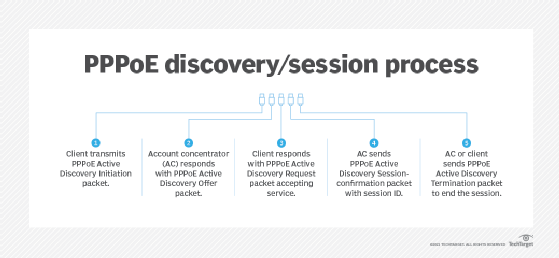
PPPoE communications are carried out in two stages: PPPoE discovery and PPP session. During the PPPoE discovery stage, the client system establishes a communication channel with an access concentrator (AC) -- a PPPoE server that negotiates and authenticates the connections with PPPoE clients. For example, a service provider might maintain multiple ACs to deliver internet access services to its customers.
When a client attempts to initiate a session with an AC, the client and AC enter into the following four-step discovery process in which specific packet types are exchanged:
- The client initiates communication by transmitting a PPPoE Active Discovery Initiation (PADI) packet that includes a request for service.
- When an AC receives the PADI, it responds by sending a PPPoE Active Discovery Offer (PADO) packet that contains its name and other details about the offered service.
- In response to the PADO, the client sends a PPPoE Active Discovery Request (PADR) packet to the AC -- in effect, to accept the service. If the client receives PADOs from multiple ACs, it selects one based on the name or services offered.
- When the AC receives the PADR, it sends a PPPoE Active Discovery Session-confirmation, or PADS packet, confirming the connection and providing a session ID used throughout the session.
After the discovery stage is complete and the connection has been established, the client and AC move on to the PPP session stage. During the session stage, point-to-point communications between the client and AC are carried out like any PPP encapsulation. The Ethernet packets themselves are sent unicast.
During the session, the AC or client can send a PPPoE Active Discovery Termination (PADT) packet to end the session. When the client or AC receives the PADT, no further PPP traffic is allowed during that session.
How is PPPoE configured?
Some ISPs supply their customers with broadband modems with the already configured PPPoE connections. In some cases, however, administrators might need to set up the connections manually. For this, they must know the PPPoE username, password and maximum transmission unit (MTU) size. The ISP should provide the customer with the username and password, but administrators are responsible for the MTU sizing.
Networks must be configured with the correct MTU size to work properly. The size is specified in octets -- 8-bit bytes -- and determines the maximum size packet or frame that can be sent across a network. TCP uses MTU when transmitting packets between devices connected to the internet.
An MTU size that is too large might result in retransmissions if the packet encounters a router that cannot handle the packet size. An MTU size that is too small can result in more header overhead and a greater number of acknowledgments that need to be sent and received. The recommended MTU for a network interface connected to a PPPoE network is generally a maximum of 1492.
There might also be times when users need to configure PPPoE connections directly from their computers, such as when a bridging modem is set up for passthrough PPPoE connectivity. In this case, users must manually configure the PPPoE connections.
Fortunately, major operating systems, such as macOS, Linux and Windows, include native PPPoE support, so setting up the connection is fairly straightforward. However, users need the PPPoE account information -- service name, username and password -- which the ISP typically provides. Once they set up their connections, they should not need to bother with it again, unless they upgrade their systems or perform other operations that affect the connection.
Benefits and drawbacks of PPPoE
ISPs and clients use PPPoE for the following reasons:
- Centralized authentication. PPPoE clients can be centrally authenticated using a Remote Authentication Dial-In User Service, or RADIUS, server, making account and access management easier.
- Dynamic IP addressing. IP address assignment to PPPoE clients can be dynamic using a central pool of available IP addresses.
- Session management. Multiple sessions can be created and managed over a single physical connection.
- Broad support. Windows, macOS and Linux all support PPPoE.
- Bandwidth management. ISPs can optimize bandwidth by managing speed and allotment to PPPoE clients.
- Security. IP security features, such as authentication and encryption, are easily implemented across an Ethernet network.
PPPoE does, however, have the following drawbacks:
- Complexity. PPPoE must be manually configured, requiring users to have strong familiarity and experience with network protocols.
- Unicast connections. PPPoE supports unicast connections, which can impair both efficiency and scalability.
- Fragmentation potential. PPPoE reduces the MTU from the Ethernet standard of 1500 bytes to 1492, possibly creating fragmentation issues.
- Lack of native support for multiuser environments. PPP was created for point-to-point connections, not multiuser networks.
PPPoE vs. DHCP
Dynamic Host Configuration Protocol (DHCP) is often compared to PPPoE or mentioned within the same context. DHCP is a communications protocol that runs at the TCP/IP application layer. It lets network administrators centrally manage and automate the assignment of IP addresses across a network. It also enables them to monitor and distribute IP addresses from a central point and automatically send new IP addresses when computers plug into other network locations.
DHCP allocates unique IP addresses to network devices so that data packets can be delivered back and forth. The DHCP architecture is typically made up of DHCP clients, DHCP servers and DHCP relay agents. Without DHCP, network administrators must manually configure IP addresses when adding or moving devices from one subnet to another -- or devise another option.
Unlike DHCP, PPPoE encapsulates network traffic based on credentialed access. Once a session is established, IP addresses can be assigned to client devices. PPPoE also includes authentication capabilities that enable ISPs to control and monitor access. However, PPPoE must be configured correctly before users can connect to the internet.
In general, PPPoE serves a much different purpose from DHCP. It facilitates authenticated PPP communications on an Ethernet network, whereas DHCP dynamically allocates IP addresses without requiring authentication.
PPPoE troubleshooting steps
The following are several good go-to steps for troubleshooting PPPoE implementations:
- ID address assignment failure. A PPP negotiation failure can result in no IP address being assigned. Reboot the client device and modem or router.
- Authentication failure. This is usually caused by incorrect credentials. Verify PPPoE username and password with the ISP.
- Slow speed. If PPPoE is below the speed specified in the plan, verify the mode and bandwidth settings in the modem's and router's administrative interfaces.
PPPoE best practices
Keep the following best practices in mind when setting up PPPoE:
- Manage traffic. To prevent overload, limit the number of connected devices on a PPPoE connection.
- Enable keepalive. Keepalive manages connection status by restarting any link that goes idle.
- Do regular firmware updates. To prevent security issues, do regular firmware updates on modems, routers and other PPPoE devices.
- Reboot regularly. Reboot modems and routers regularly to prevent accumulating compounding issues.
Port numbers are an important way to identify and direct network traffic to specific applications or services running on network-connected devices. Learn about the different types of port numbers and their uses.







