Automation brings NetOps to the next level
Automation and AI can help enterprise NetOps teams attain the data insights they need to deliver services more efficiently and create a more agile, proactive network.
Network operations, or NetOps, isn't what it used to be. Networks now comprise hybrid environments that generate growing amounts of data, causing NetOps to encompass more than just traditional tasks of network configuration, troubleshooting and provisioning. To revamp network processes, many NetOps teams are implementing automation capabilities in their network infrastructure.
One of the ultimate goals of integrating automation and NetOps is to enable a more agile, proactive and insightful network -- what some call a self-healing or self-operating network. But self-operating doesn't necessarily mean the network works without any human interaction.
Networks already have a wealth of data that can provide insights into how a network runs and point to areas in need of improvement. The ideal version of NetOps capitalizes on data using automation and AI tools that weed through information to pinpoint useful metrics and trends. NetOps teams can use those insights to determine which processes they should automate to align with their business needs, said Ernest Lefner, former ONUG co-chairman and current chief product officer at Gluware, a network automation vendor.
"What that will do is let us generate insights, take action on those insights, make the network better and take us one step closer to that self-operating model," Lefner said.
The stages of automation adoption
NetOps follows in the footsteps of DevOps, a software development methodology that prioritizes continuous integration and continuous delivery (CI/CD) and cross-collaboration. While DevOps aims to deliver code releases more quickly and efficiently, NetOps prioritizes service and application delivery. Both strategies achieve those goals using automation and orchestration.
By now, most network engineers have heard about the importance of automation and what it means for their future. And most tend to think of automation in the context of scripting with Ansible, Chef, Puppet or Python.
But scripting languages are just one avenue toward automation. Network engineers can choose from vendor platforms, open source tools, infrastructure as code and low-code/no-code options -- all of which have varying outcomes depending on the organization and business requirements.
A sizable portion of enterprise network teams have made headway in adopting automation. According to a recent survey from Enterprise Strategy Group (ESG), a division of TechTarget, 28% of 338 IT professionals said they used network automation extensively, while another 41% said they used it in limited fashion. Some of the most common tasks respondents said they automated included the following:
- IT asset inventory discovery;
- lifecycle management; and
- provisioning new devices using centralized policies.
While most network practitioners start by automating basic network management tasks, they can expand into other areas, such as firewall rule migration, hybrid cloud monitoring and OS management.
Eventually, as teams trust the automated processes more -- and as the automation, AI and data analytics behind them evolve -- networks could develop into self-healing, proactive networks.
 Ernest Lefner
Ernest Lefner
What are the components of NetOps automation?
Many network pros start with automation by buying tools from common networking vendors. Those tools automate some workflows but don't always provide the functionality or control teams want, Lefner said. That's often when teams turn to Ansible or Python so they can better customize the tasks they want to automate. But, depending on the staff, skill sets and resources available, scripting isn't always scalable or efficient. In some cases, a low-code automation platform that simplifies automation with drag-and-drop components can be beneficial.
NetOps teams will likely gravitate toward one option based on their level of expertise and trust. But, regardless of how they choose to implement automation into their network operations, some common factors are necessary to attain an efficient NetOps model.
Data insights and observability
Network observability is more than monitoring. It capitalizes on the data produced by networks to focus on how networks can improve end-user experience. NetOps teams can then determine how their networks should operate to reach an intended state, which is designed to meet business goals.
But intent is not enough on its own, Lefner said.
"There needs to be a level of intelligence that comes with it," Lefner said. "The goal is to garner insights from the network and have those insights, in an automated way, translate into activities you do with your automation to make the network better."
 Bob Laliberte
Bob Laliberte
AI and machine learning
To achieve the needed intelligence for those insights, networks need to incorporate AI and machine learning (ML) tools, as humans simply can't sift through data as efficiently, said Bob Laliberte, principal analyst at ESG.
"It's impossible to humanly do the data correlation," Laliberte said. "You need the intelligence layers to read through the data. But human intervention will be key for AI and ML."
According to ESG, 32% of respondents said their top data center network initiative was to invest in AI and ML tools for their self-healing and optimizing capabilities. But enterprises have varying levels of trust in those tools.
Laliberte said network teams tend to see three progressive levels of AI and ML adoption:
- Tools send alerts, but staff remain in full control.
- Tools provide alerts and recommendations based on network insights, but staff are responsible for implementing and executing the recommendations.
- Tools automatically detect, analyze, recommend and apply changes as needed, while staff can review and make changes, if necessary.
A large majority of network pros favor the second option, which keeps control in their hands but minimizes the analysis they do to fix or address a problem. Essentially, this option provides what Laliberte called an "easy button," where staff can push a button to make the automation run. Typically, he said it takes organizations two to eight months to reach that point of full automation, depending on how many processes they automate.
Orchestration, CI/CD and APIs
Eventually, automation and AI lead to orchestration and a CI/CD pipeline that enables cyclical loops of testing, deployment and validation. Once teams start relying more on automation tools, Laliberte said they should ensure the tools incorporate a closed-loop system to verify problem resolution and approve fixes for future scenarios.
According to Lefner, industry vendors are already working to develop these capabilities within their automation platforms and make it easier for customers to drag and drop where they want to automate processes.
"What you're finding is NetDevOps platforms for networks are being built in a way that allow for low-code/no-code and an encapsulated CI/CD platform directly inside the platform," Lefner said.
APIs are a key component of those platforms, he added, because they enable automation to work among various environments, vendors and devices. By natively integrating the APIs within the platform, they become part of the CI/CD pipeline. Those native APIs can also better support automated remediation of vulnerabilities throughout the system.
Agility and reliability
Proper data insights, automation and orchestration pave the way for more agile networks that enable faster response times and can better address changing business requirements.
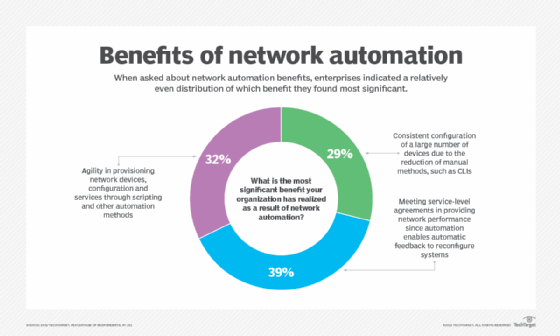
According to ESG's survey, enterprises indicated that agility and feedback loops were some of the most significant benefits they saw from network automation:
- 39% said network automation best helped them meet service-level agreements for network performance, as it supports an automatic feedback loop.
- 32% said the most significant benefit was agility in provisioning network devices, configuration and services through scripting and other automation methods.
- 29% said they considered consistent configuration of a large number of devices to be the biggest benefit because they could move away from manual methods, like the command-line interface.
Network security
Finally, NetOps strategies need to consider network security. As security threats swell, network and security teams have realized they can no longer remain in silos if they want to secure their networks, Lefner said.
"Now, they're saying, 'Hey, the fact of the matter is: The tooling and information we need to be able to run a security and network organization are pretty much the same, so how do we start bringing them together?'" Lefner said.
As a result, NetOps and security operations teams are working together more. According to a recent Enterprise Management Associates survey of 366 IT professionals, 83% of organizations said they saw increased collaboration between their network and security teams. The main driver of this collaboration was the security's team need to analyze network data.
According to Lefner, network and security responsibilities will shift so security engineers focus on content -- what to block, where to block, how to protect -- while network engineers are responsible for policy enforcement, policy validation and audit control.
"It's going to become a much more sophisticated data-driven model," Lefner said.







