
bluebay2014 - Fotolia
Top 3 network security threats and how to protect against them
Enterprise networks are seemingly always under attack. Learn about the most common network security threats and what protections you should have in place.
The network is business-critical. Any network security threats that interfere with operations and infrastructure can have a significant effect.
According to a recent study by IBM Security and the Ponemon Institute, each data breach typically costs an organization nearly $4 million. As the volume and severity of cyberattacks accelerate, understanding the biggest threats and what security infrastructure needs to be in place is crucial to prevent attacks and recover from breaches when they occur.
Considering the diversity and expanse of attack types, identifying the most severe network security threats can be challenging. Everything from exploit kits to cryptojacking poses a threat to optimal network operations and data security.
In particular, these three common network security threats are perhaps the most dangerous to enterprises:
- malware
- advanced persistent threats
- distributed denial-of-service attacks
In all cases, effective mitigation requires a multilayered approach to security. The good news is many of the elements work to protect against multiple threat vectors.
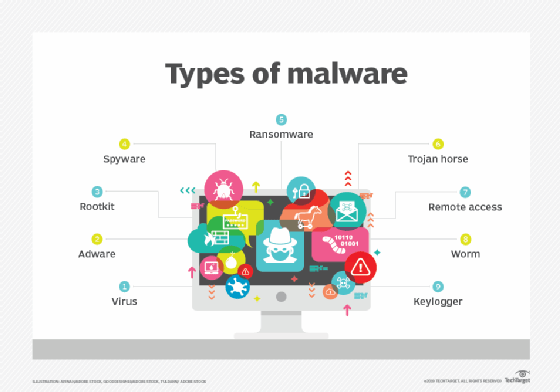
How dangerous is malware?
Malware is malicious software designed to infect computers and other systems to interrupt operations and surreptitiously track activity. It's one of the most widely employed and potentially damaging attacks. It can be deployed broadly through multiple organizations and often goes undetected until it is too late. Malware can be transferred via email, through a download from a website or through other communications methods.
While reports show some malware sources serving up less of the malicious code, other vectors such as phishing and other email-based attacks are soaring. Malware is used in a range of attack strategies, including ransomware, which is declining in the consumer sector, but escalating as an enterprise threat.
Fighting malware requires more than antivirus software and vigilant patch updates. Organizations need to employ content scanning and filtering on email servers, which have become especially attractive attack targets.
Firewalls -- and having the right rules in place -- can be vital to deflect malicious code. Virtual private networks also play a key defensive role in helping remote users connect to the network securely and avoid viruses, worms and other malicious code.
Educating end users on the different strategies attackers use to breach network assets -- including phishing attacks and malicious code delivered via insecure websites -- is an important part of a well-executed defense.
If a breach occurs, IT needs a solid business continuity and disaster recovery plan in place. Enterprises without a strategy that incorporates a consistent backup plan may find operations crippled for hours, days or longer. And if the attack involves ransomware, the prevailing wisdom is not to pay the demand or risk future strikes.
What are the characteristics of advanced persistent threats?
Advanced persistent threats (APTs) are highly sophisticated and stealthy attacks that target a specific company or system. They use several mechanisms to breach the network, circumnavigate enterprise controls and access the desired information without authorization.
APTs can use malware to penetrate the network and apply a technique like phishing to acquire credentials to tap into the desired data. Cyberattackers who use APTs often take their knowledge from a breach to retarget the organization.
Firewalls, email protection, managed detection and response services, and antivirus software are key elements in the defense against APTs. Enterprises should also have a sandbox environment to siphon untrusted programs and code to be tested.
What happens in a distributed denial-of-service attack?
Between January 2018 and June 2019, the number of average daily distributed denial-of-service (DDoS) attacks nearly doubled, according to Akamai Technologies. DDoS attacks use multiple systems to flood the targeted network asset with traffic in order to disrupt operations. In many cases, the attackers hijack high-value targets in order to extort the organization. These attacks are sometimes ideologically or politically motivated.
Public and private sector organizations need to have several measures in place to shield their infrastructure from these attacks. They need a secure network infrastructure that employs intrusion protection, unified threat management and network performance monitoring. Enterprises should employ a geographically diverse approach to server placement, potentially using the cloud to ensure that strategy.
Enterprises also need to execute on best practices that incorporate consistent system updates. They need a solid and tested response plan in the event of an incident. Many businesses also benefit from third-party DDoS mitigation services that detect and mitigate attacks.







