network functions virtualization (NFV)
What is network functions virtualization (NFV)?
Network functions virtualization (NFV) is a network architecture model designed to virtualize network services that have traditionally run on proprietary, dedicated network appliances. With NFV, functions like routing, load balancing and firewall access controls are packaged as virtual machines (VMs) or containerized processes delivered on commodity hardware -- the two most popular virtualization technologies available today. Individual virtual network functions (VNFs) are an essential component of NFV architecture.
Multiple VNFs can be added to a standard x86 server and then monitored and controlled by a VM hypervisor or container host. NFV's mission to use commodity hardware is important because network managers no longer need to purchase and manually configure dedicated appliances in order to build a service chain that links certain functions to perform a desired sequence. Each dedicated appliance, by comparison, needs to be manually cabled together accordingly, which is a time-consuming process and consumes more data center space and electricity.
Because NFV architecture virtualizes network functions and eliminates previously required physical appliances, network administrators can add, move or change network functions at the server level in a simplified provisioning process using software, as opposed to hardware.
If a VNF running on a VM requires more bandwidth, for example, the network operations staff can move the VM to another physical server or provision another VM on the original server to handle part of the load. This move is performed solely in software and can be automated and remotely executed. Having this level of flexibility enables a network team to respond to moves, adds and changes in a more nimble and scalable manner to changing business goals and network service demands.
Benefits of network functions virtualization
The NFV concept was originally presented by a group of network service providers at the SDN and OpenFlow World Congress in October 2012. These service providers sought a way to simplify and accelerate the process of adding new network functions or applications that could offer the following benefits:
- rapid deployment;
- ability to scale upward or downward with ease;
- effortless upgrades through software and without expensive hardware replacements; and
- lower overall cost of network deployment and management.
The service providers' solution enabled networks to be deployed in such a way that network services could be virtualized and placed onto low-cost, generic commodity hardware. This decoupling of hardware from software using a virtualized layer provided the ideal foundation from which to build complex, scalable and highly flexible commercial networks that could be placed into increasingly smaller data centers for energy conservation purposes.
The European Telecommunications Standards Institute (ETSI) Industry Specification Group for Network Functions Virtualization proceeded to spearhead NFV development and standards.
While NFV can benefit enterprises, service providers have a more immediate use case for it. Many see NFV's potential to improve scalability and better utilize network resources. This is especially true now that edge computing and micro data centers are beginning to gain momentum for the servicing of real-time applications. If a service provider's customer requests a new function, for example, NFV enables the service provider to more easily add that service in the form of a VM without upgrading or buying new hardware on the customer end.
Basic NFV benefits also include reduced power consumption and decreased physical data center space, since NFV eliminates most traditional hardware appliances. In this regard, NFV can help reduce both operational and capital expenditures, creating faster return on investment (ROI) for edge computing data center rollouts.
Challenges of network functions virtualization
Until recently, NFV deployment has seen relatively slow progress due to a lack of standards in NFV management and orchestration (MANO). MANO delivers the following benefits:
- provides the framework for managing NFV infrastructures;
- simplifies the network functions onboarding process through automation;
- helps components within NFV infrastructure communicate with existing operational and billing support systems.
Part of the challenge for NFV adoption is the number of standards and open source projects being conducted to promote NFV development. For example, a short list includes ETSI, Open Platform for NFV, Open Network Automation Platform, Open Source MANO and MEF -- formerly the Metro Ethernet Forum.
With so many competing approaches -- all backed by various service providers and operators -- settling on an approach that offers usable capabilities for the whole industry is problematic. As a result, some service providers were hesitant to invest in NFV architectures until a clear architectural direction was made.
Even more importantly was, despite the need for flexibility and scalability, service providers struggle to prove an ROI that would justify such a major architectural change. However, two factors have eased this problem as of late:
- the use of containers to reduce OS and compute overhead within virtualized environments; and
- an increasing demand for edge computing services that is forcing service providers to operate using a more nimble infrastructure, like NFV.
NFV architecture
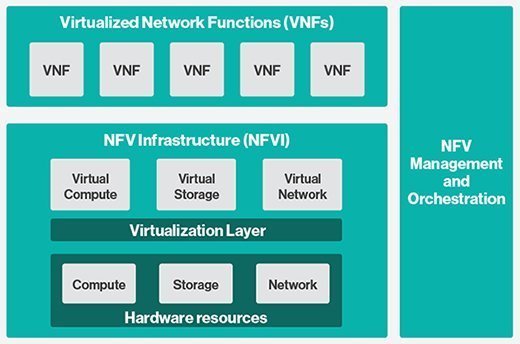
Unlike traditional network architectures that combine software and hardware to develop individual network functions, NFV decouples hardware from software by virtualizing hardware processes within a software layer. Additionally, a third software layer is responsible for MANO of both the NFV infrastructure (NFVI) and VNFs to enable rapid VNF deployment and scalability.
In the following diagram, there are three distinct layers. At the bottom, the NFVI is the software-derived layer that mimics and allocates traditional hardware functions, including compute, storage and networking. Individual VNFs are the actual network functions that tap into the NFVI for those resources. Finally, the NFV MANO layer provides management and observability.
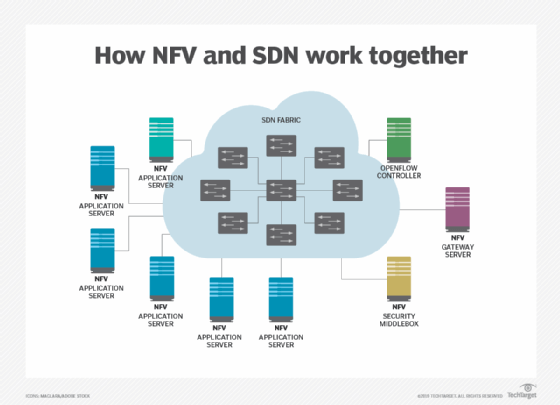
NFV vs. SDN
Often confused as being the same, NFV and software-defined networking (SDN) are complementary network abstraction initiatives. The purpose of NFV is to decouple hardware from network functions and move those services inside virtual network environments. The goal is to lower implementation and operational costs, while simplifying scalability and management.
SDN, on the other hand, focuses on separating the execution of network functions from configuration control and management. The control plane is then responsible for managing all network functions across the entire infrastructure, while the distributed data plane performs the network functions it was requested to perform by the control plane. This model is ideal for environments where network automation is highly desirable.
When SDN is combined with NFVI, however, SDN's centralized control plane management function can facilitate the optimal forwarding mechanisms that the data plane uses, while NFV enables routing control functions to run within VMs or containers located in a data center, cloud or edge compute environment, for example.