Nimda
What is Nimda?
First appearing on September 18, 2001, Nimda is a computer virus that caused traffic slowdowns as it rippled across the Internet. Nimda spread through four different methods, infecting computers containing Microsoft Window's web server, known as Internet Information Server (IIS), and computer users who opened an email attachment.
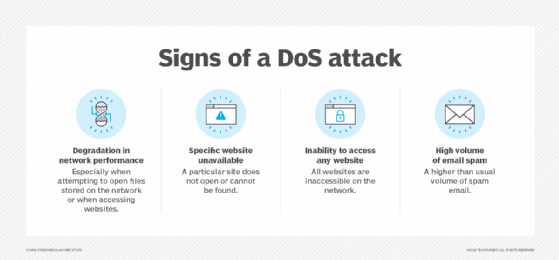
Like several predecessor viruses, the Nimda worm's payload appears to be the traffic slowdown itself.
It did not destroy files on the operating system or cause harm to the computer security. Instead, it served more to cause chaos through the slowing of traffic or the denial of service.
Its file name, which spelled backward is "admin," refers to the admin.dll file shared through an email message that, when run, continues to propagate, causing an outbreak of worm copies. Nimda affected computers running on Windows 95, 98, 2000, and Windows NT and XP before a patch was created to rectify the vulnerability.
A company called F-Secure uncovered the text "Concept Virus(CV) V.5, Copyright(C)2001 R.P.China" in the Nimda code, which helped narrow down the origin of the virus.
Another example is the Code Red and Code Red II outbreaks that attacked computers running Microsoft IIS. Unlike Nimda, these worms created a backdoor in the target system, making it vulnerable to future attacks.
What does Nimda malware do?
Nimda probes each IP address within a randomly selected range of IP addresses, attempting to exploit weaknesses that, unless already patched, are known to exist in computers with Microsoft's Internet Information Server.
A system with an exposed IIS web server reads websites containing an embedded JavaScript that automatically executes, causing the same JavaScript code to propagate to all web pages on that server.
When users with Microsoft Internet Explorer browsers 5.01 or earlier visit sites at the infected web server, they unwittingly download pages with JavaScript.
The JavaScript automatically executes, sending the virus randomly from the infected computer to other devices on the Internet. Nimda hackers can also infect users within the web server's internal network with an open network share (a portion of file space).
Finally, the Nimda virus causes an infected system to send an email with an executable readme.exe attachment to the addresses in the local Windows address book. A user who opens or previews this attachment -- an infected website with JavaScript -- propagates the virus further.
How to protect your system from malware
As a best practice, PC users should never open a readme.exe or readme.eml file attachment sent by email. More to the point, users should never open files or links they don't recognize or from senders they don't recognize.
Users should always make sure they have the most updated version of their browser running
If they do believe the system is infected:
- Disconnect the points of entry for the infection.
- Restore the system from a backup or reformat it and reinstall/patch the OS.
- Restore the existing data -- whether it is infected or not -- and then cleanse the system and scan it with antivirus software.
- Should it pass, go ahead reconnect it to the network.
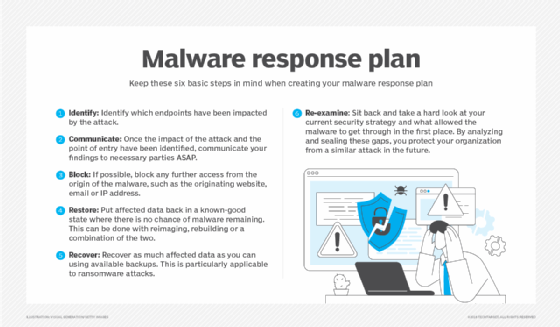
Once a victim's system has been fully restored, install reputable antivirus software on the device. Reputable providers include Norton, McAfee and Symantec.
Explore difference between malware and ransomware and learn what you should know to become a malware analyst. Also, find out what you should do after an employee clicks on a malicious link and check out some data protection tips to give ransomware the boot.








