asymmetric cryptography
What is asymmetric cryptography?
Asymmetric cryptography, also known as public key cryptography, is a process that uses a pair of related keys -- one public key and one private key -- to encrypt and decrypt a message and protect it from unauthorized access or use.
A public key is a cryptographic key a person can use to encrypt a message so it can only be decrypted by the intended recipient with their private key. A private key -- also known as a secret key -- is shared only with the key's initiator.
When someone wants to send an encrypted message, they pull the intended recipient's public key from a public directory and use it to encrypt the message before sending it. The recipient of the message can decrypt the message using their related private key.
If the sender encrypts the message using their private key, the message can be decrypted only using that sender's public key, thus authenticating the sender. These encryption and decryption processes happen automatically; users do not need to physically lock and unlock the message.
Many protocols rely on asymmetric cryptography, including Transport Layer Security (TLS) and Secure Sockets Layer (SSL), which make HTTPS possible.
The encryption process is also used in software programs that need to establish a secure connection over an insecure network, such as web browsers, or that need to validate a digital signature.
Increased data security is the primary benefit of asymmetric cryptography. It is the most secure encryption process because users are never required to reveal or share their private keys, decreasing the chances of a cybercriminal discovering a user's private key during transmission.
How does asymmetric cryptography work?
Asymmetric encryption uses a mathematically related pair of keys for encryption and decryption: a public key and a private key. If the public key is used for encryption, then the related private key is used for decryption. If the private key is used for encryption, then the related public key is used for decryption.
The two participants in the asymmetric encryption workflow are the sender and the receiver. Each has its own pair of public and private keys. First, the sender obtains the receiver's public key. Next, the plaintext message is encrypted by the sender using the receiver's public key. This creates ciphertext. The ciphertext is sent to the receiver, who decrypts it with their private key, returning it to legible plaintext.
Because of the one-way nature of the encryption function, one sender is unable to read the messages of another sender, even though each has the public key of the receiver.
Uses of asymmetric cryptography
Asymmetric cryptography is typically used to authenticate data using digital signatures. A digital signature is a mathematical technique that validates the authenticity and integrity of a message, software or digital document. It is the digital equivalent of a handwritten signature or stamped seal.
Based on asymmetric cryptography, digital signatures can provide assurances of evidence to the origin, identity and status of an electronic document, transaction or message, as well as acknowledge informed consent by the signer.
Asymmetric cryptography can also be applied to systems in which many users might need to encrypt and decrypt messages, including the following:
- Encrypted email. A public key can encrypt an email message, and a private key can decrypt it.
- SSL/TLS. Establishing encrypted links between websites and browsers also uses asymmetric encryption.
- Cryptocurrencies. Bitcoin and other cryptocurrencies rely on asymmetric cryptography. Users have public keys that everyone can see and private keys that are kept secret. Bitcoin uses a cryptographic algorithm to ensure only legitimate owners can spend the funds.
In the case of the Bitcoin ledger, each unspent transaction output (UTXO) is typically associated with a public key. For example, if user X, who has an UTXO associated with their public key, wants to send the money to user Y, user X uses their private key to sign a transaction that spends the UTXO and creates a new UTXO that's associated with user Y's public key.
What are the benefits and disadvantages of asymmetric cryptography?
The benefits of asymmetric cryptography include the following:
- The key distribution problem is eliminated because there's no need for exchanging keys.
- Security is increased since the private keys don't ever have to be transmitted or revealed to anyone.
- The use of digital signatures is enabled so a recipient can verify that a message comes from a particular sender.
- It allows for nonrepudiation so the sender can't deny sending a message.
Disadvantages of asymmetric cryptography include the following:
- It's a slow process compared to symmetric cryptography. It's, therefore, not appropriate for decrypting bulk messages.
- If an individual loses their private key, they can't decrypt the messages they receive.
- Because public keys aren't authenticated, no one can ensure a public key belongs to the person specified. Consequently, users must verify their public keys belong to them.
- If a malicious actor identifies a person's private key, the attacker can read that individual's messages.
What's the difference between asymmetric vs. symmetric cryptography?
The main difference between asymmetric versus symmetric cryptography is that asymmetric encryption algorithms make use of two different but related keys. One key encrypts data and another key decrypts it. Symmetric encryption uses the same key to perform both encryption and decryption functions.
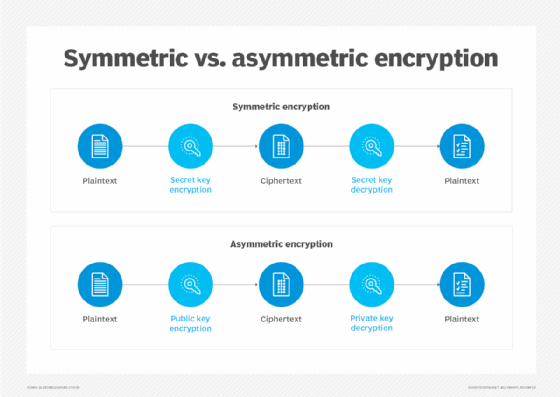
Another difference between asymmetric and symmetric encryption is the length of the keys. In symmetric cryptography, the length of the keys -- which is randomly selected -- is typically set at 128 bits or 256 bits, depending on the level of security needed.
In asymmetric encryption, there must be a mathematical relationship between the public and private keys. Since malicious actors can potentially exploit this pattern to crack the encryption, asymmetric keys need to be longer to offer the same level of security. The difference in the length of the keys is so pronounced that a 2,048-bit asymmetric key and a 128-bit symmetric key provide about an equivalent level of security.
Asymmetric encryption is notably slower than symmetric encryption, which has a faster execution speed.
What are examples of asymmetric cryptography?
The RSA (Rivest-Shamir-Adleman) algorithm -- the most widely used asymmetric algorithm -- is embedded in SSL/TLS, which is used to provide secure communications over a computer network. RSA derives its security from the computational difficulty of factoring large integers that are the product of two large prime numbers.
Multiplying two large primes is easy, but the difficulty of determining the original numbers from the product -- factoring -- forms the basis of public key cryptography security. The time it takes to factor the product of two sufficiently large primes is beyond the capabilities of most attackers.
RSA keys are typically 1,024 or 2,048 bits long, but experts believe 1,024-bit keys will be broken soon due to the advent of quantum computing, which is why government and industry are moving to a minimum key length of 2,048-bits.
Elliptic curve cryptography (ECC) is gaining favor with many security experts as an alternative to RSA. ECC is a public key encryption technique based on elliptic curve theory. It can create faster, smaller and more efficient cryptographic keys through the properties of the elliptic curve equation.
To break ECC, an attacker must compute an elliptic curve discrete logarithm, which is significantly more difficult than factoring. As a result, ECC key sizes can be significantly smaller than those required by RSA while delivering equivalent security with lower computing power and battery resource usage.
The history of asymmetric cryptography
Whitfield Diffie and Martin Hellman, researchers at Stanford University, first publicly proposed asymmetric encryption in their 1977 paper, "New Directions in Cryptography."
The concept was independently and covertly proposed by James Ellis several years earlier, while he was working for the Government Communications Headquarters, the British intelligence and security organization. The asymmetric algorithm as outlined in the Diffie-Hellman paper uses numbers raised to specific powers to produce decryption keys. Diffie and Hellman initially teamed up in 1974 to solve the problem of key distribution.
The RSA algorithm, which was based on the work of Diffie, was named after its three inventors -- Ronald Rivest, Adi Shamir and Leonard Adleman. They invented the RSA algorithm in 1977 and published it in Communications of the ACM in 1978.
Editor's note: This article was updated by Kate Brush and Michael Cobb in 2021. TechTarget editors revised it in 2024 to improve the reader experience.






