What is a private key?
A private key, also known as a secret key, is a variable in cryptography used with an algorithm to encrypt or decrypt data. Private keys play an important role in symmetric cryptography, asymmetric cryptography, digital signatures and cryptocurrency transactions.
What is a private key in cryptography?
The private key is among the best-known types of secret keys in cryptography. It refers to a long, randomly -- or pseudo-randomly -- generated sequence of bits that usually form an alphanumeric code. The code cannot be easily guessed due to its length and randomness.
Unlike the public key -- used along with the private key in asymmetric cryptography -- the private key is not publicly available. An authorized party, usually the recipient of a transaction or message, keeps it secret and will use it to decrypt an encrypted file or message. The sender does the encryption using the public key. To ensure transaction integrity, the key generator should keep private keys secret or only share them with parties authorized to decrypt the data.
The secrecy, complexity and length of the private key matter. These factors determine how easily an attacker can execute a brute-force attack, where they try out different keys until finding the right one to decrypt an encrypted message and gain unauthorized access to its contents.
What is a private key best used for?
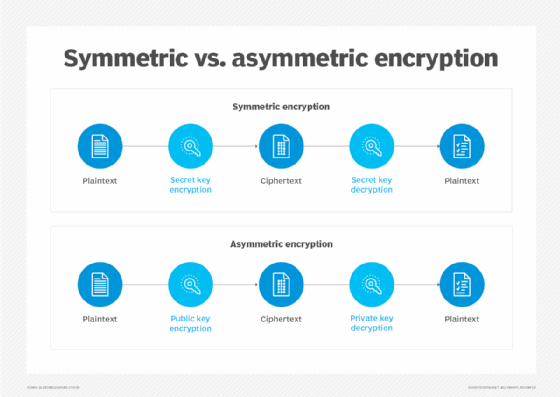
Private keys are most commonly used to decrypt -- and sometimes also encrypt -- data. In symmetric cryptography, the same key is used to both encrypt and decrypt information. In asymmetric cryptography, a private key is used to decrypt data already encrypted by a public key.
Digital signatures are another important application of private keys. Users can create digital signatures using private keys. In transactions where the signature is used, another party can verify the private key using the corresponding public key to confirm that the signature holder is who they say they are.
Transactions made using cryptocurrencies like bitcoin also depend on cryptographic algorithms and private keys to generate, store and exchange digital value. Cryptocurrencies use public key cryptography to create digital signatures that authenticate value transfers, as well as symmetric encryption to protect data exchanges. When a user buys cryptocurrency, they receive both a public key they can share with others to send or receive funds, and a private key that only they can use to unlock their wallet or vault.
Cryptocurrency owners should store private keys securely because losing control or access to a private key could mean losing access to the cryptocurrency asset. Secure options for storing private keys include storing them on an isolated computer with no network -- including internet -- connections, keeping hard copies stored in a physically secure location or simply memorizing them.
How does a private key work?
Private keys can be used in symmetric encryption, where the same private key is used to encrypt and decrypt a message. This involves the following:
- Generating a new private key. Before encryption, generate a new key that is as random as possible. Encryption software is typically used to generate private keys.
- Securely storing the private key. Once generated, the private key must be stored securely. Depending on the application, keys can be stored offline or on the computer used to generate, encrypt and decrypt data. Private keys can be protected with a password, or encrypted or hashed for security. All three methods can also be used to securely store the private key.
- Key exchange. When a private key is used to encrypt and decrypt messages, a key exchange is required during the process. This is where the key is securely shared with trusted parties authorized to exchange secured data. Cryptographic software is usually used to automate this process.
- Key management. Private key management is required to rotate keys. This prevents any individual key from being used for too long, lowering the risk that hackers will get their hands on that key. Key management is a systematic process to securely retire keys after their useful lifetime is reached.
A private key is also used in asymmetric cryptography, also called public key cryptography. Here, the private key refers to the secret key of a public key pair. In this method, the private key is used for decryption. The steps are as follows:
- Generating a public-private key pair. Encryption application software is usually used to generate key pairs. It should require a source of randomness, such as mouse movement. The random nature of a private key is even more important in this process because it ensures its unpredictability and increases the difficulty of guessing the key and cracking the encryption, even if someone already knows the public key.
- Securely storing the private key. Once generated, the private key must be stored securely. As with the symmetric cryptography process, private keys generated in asymmetric cryptography can be stored offline or on the computer used to generate, encrypt and decrypt data. Here, too, private keys should be protected with a password, or encrypted or hashed for security.
- Key exchange. It's almost never a good idea to share the private key of a public key pair with others. Public key cryptography, including digital signatures, is typically used to securely share session keys used for symmetric encryption. However, other protocols for public key infrastructure are used to authoritatively share public keys between cooperating parties.
- Using the private key. The authorized recipient of a message owns and uses their private key from a public key pair to decrypt encrypted data; the data is encrypted with the public key of the pair. Only the holder of the private key should be able to decrypt the data. Only then can message or transactional integrity be assured. For digital signatures, the owner of the key pair uses their private key to encrypt the signature. In this way, anyone with access to the public key can decrypt the signature and verify that it was signed by the private key owner.
- Key management. Public key pairs are often generated with expiration dates, and key management is vital to maintain access to the data protected with a key pair. For example, an expired public key certificate, which depends on a public key pair, might cause browsers to flag access to a website as insecure. Secret keys should be stored with the highest security, and public key pairs should be managed to avoid compromise or issues related to key pair expiration.
Advantages of private encryption keys
Private key encryption provides several advantages, including the following:
- Greater security. Private keys, especially those that are long and have greater entropy, or randomness, are more secure and therefore help protect transactions and data from brute-force or dictionary attacks.
- More speed. Symmetric key encryption, where the same key is used to both encrypt and decrypt data, is computationally faster than asymmetric encryption with its public-private key pairs.
- Superiority for encryption. Most cryptographic processes use private key encryption to encrypt data transmissions. They typically use a public key algorithm to securely share secret keys.
- Stream and block cipher capabilities. Secret key ciphers -- the algorithm for encrypting and decrypting data -- fall into one of two categories: stream ciphers or block ciphers. A block cipher applies a private key and algorithm to a block of data simultaneously; a stream cipher applies the key and algorithm one bit at a time. Both ciphers are popular for data security applications.
Challenges of private encryption key management
The security of encryption keys depends on choosing a strong encryption algorithm and maintaining high levels of operational security. The length and randomness of the key also affect encryption security. Proper encryption key management helps organizations better protect their data using symmetric and asymmetric encryption.
While private key encryption can ensure a high level of security, it can also present some challenges:
- Overall key management. Encryption key management is necessary to protect cryptographic keys from loss, corruption or unauthorized access.
- Continual updating. Private keys, particularly those used to encrypt sensitive or confidential data, should be changed regularly to minimize data exposure and breaches should the keys be leaked or stolen.
- Recoverability and loss. If an encryption key becomes inaccessible, data encrypted with that key will be unrecoverable and potentially lost forever.
Private keys vs. public keys
Asymmetric or public key cryptography uses pairs of public and private keys. These two different but mathematically linked keys are used in encryption to transform plaintext into encrypted ciphertext and in decryption to transform encrypted text back to plaintext.
When the public key is used to encrypt ciphertext, that text can only be decrypted using the private key. This approach enables anyone with access to the public key to encrypt a message, while only the private key holder can decrypt it.
When the private key is used to encrypt ciphertext, that text can be decrypted using the public key. That ciphertext can be a component of a digital signature, used to authenticate the signature. Only the holder of the private key could have encrypted the ciphertext, so if the related public key successfully decrypts it, the digital signature is verified.
The public key is made available to everyone who needs it in a publicly accessible repository. The private key is confidential and should only be accessible to the public key pair owner. In this method, whatever is encrypted with the public key requires the related private key for decryption and vice versa. Public key encryption is typically used for securing communication channels, such as email and e-commerce.
Private keys vs. passwords
Private keys share these characteristics with passwords:
- They must be kept secret to be secure.
- They restrict access to data, in the case of private keys, or resources, in the case of passwords.
- Their strength depends on their length and randomness.
There are also some differences between passwords and private keys.
Passwords are usually limited to characters accessible from a computer keyboard. Cryptographic keys can consist of any string of bits. Such strings can be rendered in human-accessible character sets, if necessary. The inherent complexity of private keys makes them more capable of securing data and transactions than passwords.
Human users choose most passwords, although digitally generated passwords are being used increasingly, particularly on websites.
Private keys are automatically generated by some digital system, such as a cryptocurrency wallet or pseudo-random number generator (PRNG) software. For digital signatures, the certificate owner creates private keys when they generate a certificate signing request from their server or device to request a Secure Sockets Layer/Transport Layer Security certificate.
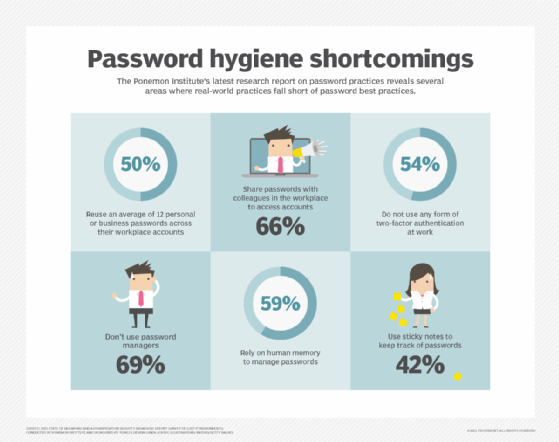
Another difference is that passwords can -- and often are -- reused for multiple transactions or accounts. This aspect makes them insecure. Private keys are rotated frequently using a private key management system, so they cannot be reused. This prevents the system from being compromised even if a hacker manages to guess a previously used private key.
Private key management involves key generation, storage, handling and rotation. All these tasks can make the entire process complex, albeit essential. Password management is rarely so complex because most systems provide easy ways to recover or change passwords.
2 important characteristics to generate secure private keys
Length and randomness are crucial factors in creating and securing private keys.
Length
The length of a cryptographic key necessary to secure it against brute-force attacks depends on the encryption algorithm being used. As computers have become more powerful, cryptographic keys have grown longer to withstand brute-force attacks.
Early web browsers protected data with 40-bit keys. Today, this length is insufficient to ensure data security. In 2015, the National Institute of Standards and Technology recommended a minimum key length of 2,048 bits for use with Rivest-Shamir-Adleman encryption. Key lengths for RSA can go up to 4,096 bits. In fact, RSA has the longest key lengths among asymmetric encryption algorithms, making it one of the strongest algorithms in use today.
Randomness
Just as important to the strength of a private key is its randomness. The more random a private key, the harder it is to guess, and the harder it becomes for an unauthorized or malicious party to break the encryption.
Commercial software often relies on a PRNG to generate private keys. However, PRNG output is not truly random, and an attacker can defeat it.
True random number generators require a source of physical entropy, such as a physical coin toss, a roll of dice or unusual generators, like lava lamps. For example, the Pretty Good Privacy public key encryption program prompts users to generate entropy for a new public key pair by randomly moving their mouse.
As use of the internet continues to expand for commercial, government and personal communication, so does the need for using encryption. Securing the private keys used to protect data is core to maintaining security in all types of communication.
Learn more about how end-to-end encryption works to keep data secure. Read why experts warn cryptography techniques must keep pace with threats and about the importance of security and data encryption in the cloud. Check out an overview of storage encryption options for enterprises.






