homomorphic encryption
What is homomorphic encryption?
Homomorphic encryption is the conversion of data into ciphertext that can be analyzed and worked with as if it were still in its original form. Homomorphic encryption enables complex mathematical operations to be performed on encrypted data without compromising the encryption.
In mathematics, homomorphic describes the transformation of one data set into another while preserving relationships between elements in both sets. The term is derived from the Greek words for same structure. Because the data in a homomorphic encryption scheme retains the same structure, identical mathematical operations will provide equivalent results -- regardless of whether the action is performed on encrypted or decrypted data.
Homomorphic encryption differs from typical encryption methods because it enables mathematical computations to be performed directly on the encrypted data, which can make the handling of user data by third parties safer. Homomorphic encryption is designed to create an encryption algorithm that enables an infinite number of additions to encrypted data.
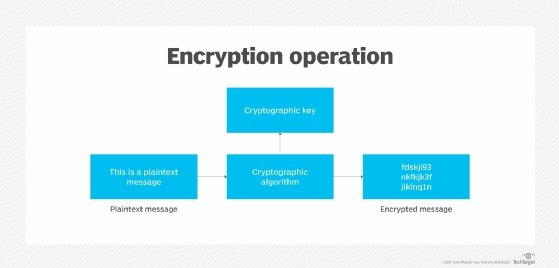
There needs to be a relationship between both plaintext and ciphertext for homomorphic encryption to perform mathematical operations on encrypted data. Plaintext is ordinary readable text, while ciphertext encrypted text is transformed from plaintext using an encryption algorithm. Two ciphertexts in homomorphic encryption, for example, should be able to be added or multiplied together with the same results as if the encryption were performed on two plaintexts. Homomorphic encryption is implemented so that it's hidden from observers.
Types of homomorphic encryption
Enabling an infinite number of additions or multiplications to encrypted data is difficult, however. As a result, homomorphic encryption can be divided into different types of encryption, depending on how it's designed.
If an algorithm is additively homomorphic, then adding two ciphertexts together provides the same result as encrypting the sum of the two plaintexts. Likewise, if an algorithm is multiplicatively homomorphic, then multiplying two encrypted ciphertexts with the same key is equivalent to raising the product of plaintexts to the power of a secret key.
Homomorphic encryption can be either additive or multiplicative, while also being partially, somewhat or fully homomorphically encrypted:
- Partially homomorphic encryption. A defined operation can be performed infinite times on the ciphertext. These encryption schemes are relatively easy to design.
- Somewhat homomorphic encryption. A limited number of addition or multiplication operations are allowed, as opposed to an infinite number of one operation. It's more difficult to design a homomorphic encryption system that supports a set number of operations than one operation infinite times.
- Fully homomorphic encryption. An infinite number of additions or multiplications for ciphertexts is enabled. Programs for any functionality can be run on encrypted inputs to produce an encrypted output.
Applications of homomorphic encryption
Homomorphic encryption could play an important role in cloud computing, enabling organizations to store encrypted data in a public cloud to take advantage of the cloud provider's analytic services.
Currently, it may be challenging for organizations to outsource data for storage, processing or analytics to a third-party cloud environment securely. However, with homomorphic encryption, data processing or analytics can be outsourced to a third party without needing to trust that party's data security. Without the correct decryption key, the original data can't be accessed, which means sensitive data can be sent and analyzed while still remaining encrypted. This can be used to preserve customer privacy in industries such as healthcare, financial services and IT.
Homomorphic encryption can also help with regulatory compliance. For example, it can help companies outside of the European Union (EU) adhere to General Data Protection Regulation (GDPR) requirements. GDPR requires EU data to remain in the EU or in countries with equivalent data security standards, but these rules don't apply to encrypted data.
Homomorphic encryption can also help organizations protect themselves from cybercriminals attacking their supply chain. If data provided to a third party is encrypted and stays encrypted, then a breach at the third party won't interrupt the organization's supply chain.
Some organizations, such as Meta -- formerly Facebook -- sell user data to third parties for targeted advertising. However, homomorphic encryption enables Meta to perform analytics on user data without being able to view the original data. This could provide more private targeted advertising.
The future of homomorphic encryption
Homomorphic encryption could be incredibly useful for data security; however, it's still too slow to have any practical use, as the ciphertexts need to be correctly added or multiplied an infinite number of times. Fully homomorphic encryption is upward of 1 million times slower than equivalent operations in plaintext.
In September 2009, Stanford University student Craig Gentry published his dissertation paper titled "A Fully Homomorphic Encryption Scheme." The paper, which presented the first plausible algorithm, said homomorphic encryption algorithms work in theory but are too slow to be usable.
Organizations such as IBM and Microsoft are currently working on the encryption format by decreasing the computational overhead needed for homomorphic encryption. In 2018, Microsoft released SEAL, which is an open source homomorphic encryption library. It can be run on Azure but is also cross-platform software. Also in 2018, IBM released a version of the open source HElib C++ library that implements homomorphic encryption. It was almost 2 million times faster than IBM's original version but still 1 million times slower than plaintext operations. A single operation that would take a plaintext operation one second would take this version of HElib 11-12 days to complete. There's still much more work needed to make this encryption format practical.
Further standardization of homomorphic encryption could aid in creating a consistency in methods and help simplify the process. However, homomorphic encryption may never realize its full potential due to its inefficiency, and it is being replaced by newer alternatives.
Learn how confidential computing techniques can protect sensitive data in cloud applications.





