What is Blowfish?
Blowfish is a variable-length, symmetric, 64-bit block cipher. Designed by Bruce Schneier in 1993 as a "general-purpose algorithm," it was intended to provide a fast, free, drop-in alternative to the aging Data Encryption Standard (DES) and International Data Encryption Algorithm (IDEA) encryption algorithms.
Unpatented and available free for all users and uses, Blowfish is significantly faster than DES and IDEA. However, due to its small block size, it couldn't completely replace DES. The algorithm's 64-bit block size is considered insecure and makes it vulnerable to birthday attacks, timing attacks and data leaks.
Twofish, its successor, addressed the security problem with a larger block size of 128 bits, which is why Schneier himself has recommended that people transition from Blowfish to Twofish. But its security concerns notwithstanding, full Blowfish encryption has never been broken -- via a concept known as cryptanalysis -- and the algorithm is included in many cipher suites and encryption products available today, including applications like virtual private networks, antivirus software and password managers.
What is Blowfish encryption?
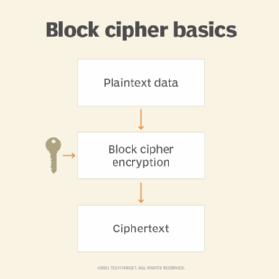
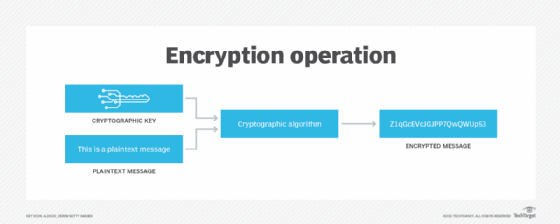
Blowfish is a type of symmetric encryption, meaning the same key is used to both encrypt and decrypt data. It is a 64-bit cipher since it features a 64-bit block size. It takes a fixed plaintext size of 64 bits of data known as a block at any one time and then encrypts it into ciphertext.
Additionally, Blowfish takes a variable-length secret key, with key lengths that can vary from 32 bits to 448 bits. The key length determines the security of the data being encrypted, with longer key lengths increasing security. It consists of 16 Feistel-like iterations, where each iteration operates on a 64-bit block that's split into two 32-bit words. Apart from the 64-bit block size and variable-length secret key, Blowfish encryption involves the following:
- Generation of 18 subkeys using P-array and the precomputation of S-boxes.
- Sixteen rounds of encryption involving complex substitutions and transpositions using XOR operations, additions and lookups in the S-boxes.
- Some postprocessing to reform 64-bit ciphertext blocks.
After postprocessing, the ciphertext is decrypted using the same process as encryption, albeit in reverse, to regenerate the plaintext.
How does Blowfish encryption work?
Blowfish uses a 16-round Feistel cipher structure.
In a Feistel structure, a round function is run iteratively a certain fixed number of times inside the algorithm. In each round, the plaintext is processed using a substitution step and permutation step.
In the case of Blowfish, each iteration operates on a 64-bit block that's split into two 32-bit subblocks. These two halves of the plaintext, which can be denoted as L for left and R for right, are scrambled separately using a series of mathematical operations -- substitution and permutation. At the end of the last round (16th), L and R are concatenated to form the ciphertext block. During decryption, the same process repeats with the subkeys used in reverse order. In the last step, L and R are swapped to enable decryption.
Blowfish encryption and decryption process
Blowfish uses a single encryption key to encrypt and decrypt data, making it an example of a symmetric encryption algorithm.
The Blowfish algorithm consists of two major parts:
- Data encryption. Prior to encryption, 18 subkeys are generated; the same subkeys are used for both encryption and decryption. The P-array and four S-boxes are initialized with the digits of pi. The encryption process consists of 16 rounds and also involves some postprocessing to rejoin 32-bit scrambled bits into 64-bit ciphertext blocks.
- Key expansion and subkeys. In the key expansion process, maximum size 448-bit keys are converted into several subkey arrays, totaling 4,168 bytes. Subkeys form an integral part of the Blowfish algorithm, which uses many of them. These subkeys are precomputed before encryption or decryption can occur.
Blowfish uses a P-array consisting of 18 32-bit subkeys (18-entry P-array) and four 32-bit S-boxes with 256 entries (256-entry S-boxes). The subkeys are calculated with these steps:
- The P-array and S-boxes are initialized with a fixed string of hexadecimal digits of pi.
- The first element in the P-array (P1) is now XORed with the first 32 bits of the key, and P2 is XORed with the second 32-bits and so on, until all the elements in the P-array are XORed with the key bits.
- All-zero strings are encrypted by the algorithm as described in the preceding steps.
- P1 and P2 arrays are replaced with the output from step three.
- This output is encrypted by Blowfish with modified subkeys.
- The output of step five modifies P3 and P4 in the P-array.
- This process continues until all the P-arrays and four S-boxes are modified -- meaning the entire P-array and all the S-box entries are replaced.
Every round involves using one entry of the P-array. After the final round, there are two remaining unused P-entries, one of which is XORed with each half of the data block. In total, Blowfish runs 521 times to generate all the subkeys and processes. This represents about 4 kilobytes of data processed.
During decryption, the subkeys are used in reverse. The process involves generating 18 subkeys stored in a P-array and the initialization of S-boxes -- four S-boxes, each having 256 entries and initialized with the digits of pi. As with encryption, Blowfish decryption also involves 16 rounds, plus postprocessing, which results in a 64-bit plaintext output.
Blowfish encryption and decryption process example
Assume the message "Hi world" needs Blowfish encyrption. The following are the steps involved:
- Initially, the input "Hi world" consists of seven characters plus one space, which is equal to 64 bits, or 8 bytes.
- The input is split into 32 bits. The left 32 bits -- "Hi w" -- are XORed with P1, which is generated by key expansion to create a value called P1 -- P denotes a prime number, a number that is not divisible except by 1 and itself.
- Then, P1 runs through a transformative F-function (F In) in which the 32 bits are split into 4 bytes each and passed to the four S-boxes.
- The first two values from the first two S-boxes are added to each other and XORed with the third value from the third S-box.
- This result is added to the output of the fourth S-box to produce 32 bits as output.
- The output of F In is XORed with the right 32 bits of the input message -- "orld" -- to produce output F1'.
- Then, F1' replaces the left half of the message, while P1' replaces the right half.
- This same process is repeated for successive members of P-array for 16 rounds in total.
- Finally, after 16 rounds, the outputs P16' and F16' are XORed with the last two entries of the P-array, i.e., P17 and P18. They are then recombined to produce the 64-bit ciphertext of the input message.
Advantages of Blowfish
One of the fastest and most compact block ciphers in public use, Blowfish uses a symmetric encryption key to turn data into ciphertext. Almost three decades after it was first developed, Blowfish is still widely used because it offers these advantages:
- It's much faster and more efficient than DES and IDEA algorithms and more flexible due to the variable key size.
- It can be freely used by anyone even without a license.
- Despite the complex initialization phase before encryption, the data encryption process is efficient and requires fewer operations compared to some other encryption algorithms.
- Once the key is encrypted, it can be quite difficult for an unauthorized party or a malicious threat actor to recover the data if they don't already have the original key.
- It provides extensive security for software and applications developed in Java.
- It offers secure access for backup tools, and it supports secure user authentication for remote access.
Disadvantages of Blowfish
There are some downsides to using Blowfish for encryption:
- Speed is hampered when changing keys.
- The initial setup process and key schedule can take a long time, making the algorithm unusable for applications where speed is a priority or where key turning is required.
- The small 64-bit block size makes the algorithm vulnerable to birthday attacks, a class of brute-force attacks, that can compromise application and user security.
- Blowfish algorithm variants with fewer rounds are vulnerable to known plaintext attacks.
- A lack of built-in authentication or data integrity checks increases the probability of data leaks.
Applications of Blowfish
Blowfish is still used in a wide range of applications:
- Bulk encryption.
- Random bit generation.
- Packet encryption.
- Password hashing and management.
- Mobile processors.
- Email, file or disk encryption.
- Data backup.
- Secure Shell.
Many popular products use Blowfish:
- PasswordWallet. This app creates and stores passwords in an encrypted database for multiple accounts, eliminating the need for remembering or managing passwords and reducing the risk of identity theft.
- Older versions of Veritas NetBackup, previously Symantec NetBackup. This multilayer data security solution combines data management and automation to protect enterprise data across integrated hybrid clouds. Starting with NetBackup v8.0, Blowfish was replaced by the 256-bit Advanced Encryption Standard (AES).
- PeaZip. This free, open source file archiver and file management utility supports multiple file and archive formats and can automate backup operations.
In the past, some social media platforms and e-commerce websites also used Blowfish to protect user data. Most of them now use elliptic curve cryptography, AES and Rivest-Shamir-Adleman because these newer algorithms are considered more secure, particularly for safeguarding sensitive information, like credit card details, and encrypting electronic communications.
Scrambling plaintext into ciphertext is essential to protect data so it cannot be read or used by the wrong people. Further explore the basics of symmetric key encryption algorithms.