metamorphic and polymorphic malware
What are metamorphic and polymorphic malware?
Metamorphic and polymorphic malware are two types of malicious software (malware) that can change their code as they propagate through a system. The main difference between them is that polymorphic malware can morph itself to change its code using a variable encryption key, whereas metamorphic malware rewrites its code without an encryption key.
Of the two, polymorphic malware is more common with most malware executables falling under this category. In contrast, metamorphic malware is more complex and hugely transformative, which enables it to evade traditional detection methods.
Polymorphic malware explained
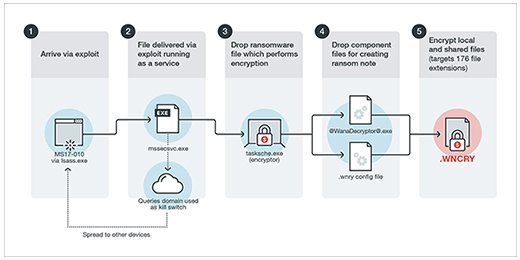
Polymorphic malware uses an encryption key to change its shape and signature. It combines a mutation engine with self-propagating code to change its appearance continuously and rapidly morph its code.
This type of malware exists in multiple forms, such as the following:
Polymorphic malware consists of two parts, namely:
- Encrypted virus body. Code that changes its shape.
- Virus decryption routine. Code that doesn't change its shape and decrypts and encrypts the other part.
Since only one part changes its shape, while the other remains the same, it's easier to detect polymorphic malware than metamorphic malware.
Nonetheless, the malware can quickly evolve into a new version. By the time antimalware detects the malware, it often has changed already. That's why many traditional signature-based detection methods can't keep up with this type of malware.
Bad actors can use one of the following obfuscation techniques to create polymorphic malware:
- Dead-code insertion, which randomly injects dead code throughout a program.
- Subroutine reordering, in which the ordering of the code's subroutines is changed in a randomized way so that it is harder for antivirus programs to detect it.
- Register reassignment, which changes registers to newer generations, while retaining the program code and behavior.
- Instruction substitution, which changes code by replacing some instructions with equivalent ones.
- Code transposition, in which routines and branches in the code are reordered without having a visible effect on its behavior.
- Code integration, in which the malware integrates itself in the target program and produces a new version of the target program.
Polymorphic malware risk factors
Bad actors use polymorphic malware to take advantage of poor cybersecurity hygiene among employees, as well as undetected zero-day vulnerabilities. When careless or clueless employees click on a malicious attachment in a phishing email or enter sensitive information into a phishing (fake) website, they leave the enterprise network and data vulnerable to polymorphic malware attacks. Also, since the malware evolves continuously, it's hard to identify and eliminate using traditional cybersecurity techniques.
Common types of polymorphic malware
Some common types of polymorphic malware seen in the previous decade are the following:
- WannaCry, a worm that spreads by exploiting Windows OS vulnerabilities.
- CryptoLocker, a virus that changes virtual servers into encrypted data blocks.
- Virlock, a type of ransomware that weaponizes files it infects and spreads through the cloud like a virus.
- CryptXXX, a Windows ransomware that is distributed using the Angler exploit kit.
Metamorphic malware explained
Metamorphic malware is rewritten with each iteration without using an encryption key. After each iteration, the new version becomes more sophisticated, although it functions the same way as before. This malware is body-polymorphic, meaning a new instance (body) of the malware is created instead of generating a new decryptor.
As with polymorphic malware, obfuscation techniques are used to create new instances of metamorphic malware. Often, malware authors use multiple transformation techniques, such as the following:
- register renaming
- code permutation
- code expansion
- code shrinking
- garbage code insertion
Metamorphic malware reprograms itself by translating its own code and then rewriting it to ensure that subsequent copies appear different with each iteration. No part of the malware remains constant, nor does the malware ever return to its original form. That's why this malware is more difficult to detect and identify using signature-based antivirus software or other cybersecurity tools.
Polymorphic versus metamorphic malware
While both polymorphic and metamorphic malware evade security by morphing and have the same objective of circumventing regular antivirus and antimalware tools, there are fundamental differences between them.
A major difference is the use of an encryption key unique to polymorphic malware. Once injected into a system, the malware uses this key to change its code, making it different from the original form. On the other hand, metamorphic malware creates a new code with each iteration.
Polymorphic malware only changes part of its code, while the other part remains the same. This feature makes it slightly easier to identify this malware. Metamorphic malware completely rewrites every part of its code so that each newly propagated version no longer matches its previous iteration. Such constant and continuous changes make it harder to detect and identify this type of malware.
Another striking difference is in the detection techniques applied. While polymorphic malware usually requires an entry point algorithm or generic description technology for detection, metamorphic malware is usually detected via geometric detection or by using tracing emulators.
Additionally, it's more difficult to write metamorphic malware than polymorphic malware because the author must use multiple transformation techniques (see previous section).
Defending against polymorphic and metamorphic malware
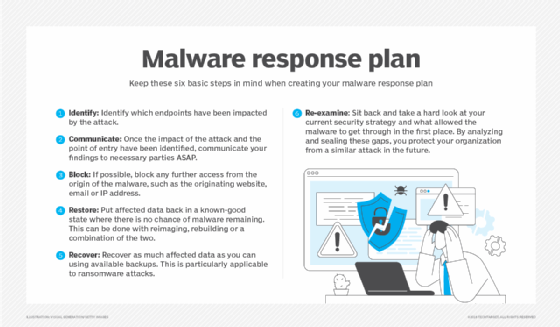
At the least, organizations should patch all known vulnerabilities to minimize the threat of successful polymorphic and metamorphic malware attacks. They should also step up their efforts to find and patch zero-day vulnerabilities.
Employee training is also critical to ensure that they know how to recognize and resist phishing scams that leave the door open to polymorphic and metamorphic malware attacks. Upgrading all software, including operating systems, and ensuring that vendors provide all necessary security updates are crucial.
Other ways to defend against this malware are as follows:
- Implementing multifactor authentication to minimize password-related attacks.
- Deploying behavior-based detection tools to identify suspicious behaviors and take immediate action.
- Using endpoint detection and response tools to narrow down threats in real time.
- Strengthening the security posture using standard frameworks, like Mitre ATT&CK.
- Employing heuristic analyses to scan for shared components of threats.
- Tightening access controls, especially to sensitive data and business-critical systems.
- Employing advanced antispam and antiphishing software to identify, quarantine and remove suspicious emails.
See also polymorphic virus and metamorphic virus.