virus signature (virus definition)
What is a virus signature (virus definition)?
A virus signature, also known as a virus definition, is a piece of code with a unique binary pattern that identifies a computer virus or family of viruses. The signature provides a digital fingerprint of the virus, which can be used to detect the virus within a file or data stream. Antivirus software and breach detection systems use virus definitions when scanning computers and networks to detect the presence of malware.
Antimalware software has long depended on virus definitions when scanning for viruses. To keep up with current threats, the software must continuously download the latest virus signatures from the vendor and incorporate them into the platform. Software that relies on outdated signatures can put both computers and networks at significant risk
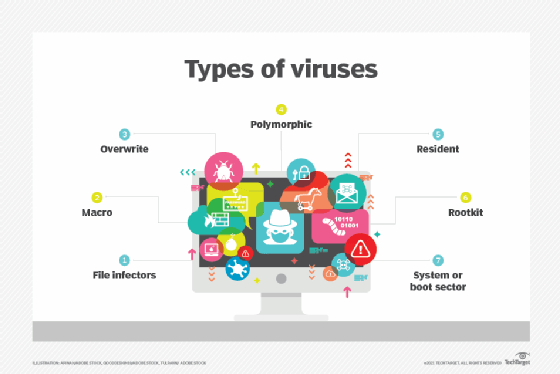
At one time, antimalware products relied heavily on virus signatures to protect systems, but signatures can protect only against known viruses and more traditional types of malware, not against unknown viruses or many of today's more sophisticated malware. For example, metamorphic and polymorphic viruses change their code as they propagate through a system, making it possible to hide malicious bits from conventional scanning processes that rely on virus definitions.
Many antimalware products now incorporate heuristic analysis or other advanced techniques to identify potential malware. For example, a heuristics-based product might use algorithms to detect behavioral patterns that are indicative of malware, rather than relying solely on virus definitions. Strong heuristics have become increasingly important because of advanced persistent threats that use encryption to conceal themselves and evade detection by typical scans.
Despite the move toward heuristics and other advanced technologies, many antimalware products continue to use virus signatures as part of their protection strategies.
How are virus signatures created?
Researchers at malware firms and other organizations create virus signatures by first studying known viruses. They intentionally download the virus from the internet and then examine and test it to see how it operates, working within isolated environments such as virtual machines or air-gapped computers.
As part of their research, they analyze the virus's behavior and functionality, as well as the code itself, examining hashes, file names, data strings, functions, IP addresses, header data and other characteristics. Researchers might use both automated and manual processes when analyzing the malware.
From their analysis, researchers will create a unique virus signature that identifies the malware. The signature will contain one or more sequences of bytes that match the malware's code. Antimalware software can then use the signature to determine whether a file or data stream contains these sequences.
Researchers take different approaches to creating and formatting virus signatures. One popular approach is to base their signatures on the YARA standard, which defines signatures through rules. A rule is a text file that identifies unique byte sequences that match the virus. A YARA file contains one or more of the following sections:
- Meta. This section specifies any metadata that the author wants to include with the rule, such as a description or the date the signature was created. This section is optional.
- Strings. The next section defines one or more byte sequences and assigns each one to a variable that can be referenced in the condition section. This section is optional.
- Condition. The last section defines a Boolean expression that determines the logic of how a file or data stream should be evaluated for the virus. This section, which is mandatory, commonly references the variables defined in the strings section.
The following code provides a simple example of what a YARA rule might look like for a fictitious virus:
rule virus_def1
{
meta:
author = "J. Smith"
description = "This is an example. "
date = "10 Feb 2024"
strings:
$a = { 6F 74 20 35 20 30 20 52 0A 2F 54 79 70 65 20 2F }
$b = { 50 61 67 65 4C 61 79 6F 75 74 20 2F 4F 6E 65 43 }
$c = { 2E 30 29 0A 2F 53 6F 75 72 63 65 4D 6F 64 69 66 }
$d = { 3F 78 70 61 63 6B 65 74 20 62 65 67 69 6E 3D 22 }
condition:
($a or $b) and ($c or $d)
}
A YARA rule begins with the rule keyword, followed by the rule's name, which in this case is virus_def1. The rest of the code is enclosed in a set of curly brackets that include one or more of the three sections. For this rule, the curly brackets include all three sections:
- The meta section provides three pieces of metadata about the rule -- the definition's author, a description of the definition, and the date the rule was created.
- The strings section defines four byte sequences. For this example, the sequences are hexadecimal strings, but they can also be text strings or regular expressions.
- The condition section specifies how the variables should be applied when searching for the virus. The first or second string must match and the third or fourth string must match.
Other systems take different approaches to building virus definitions, but the concepts are generally the same. The definition makes it possible to identify known malware by matching the byte sequences in the virus signature with those in a file or data stream.
Learn about 12 common types of malware attacks and how to prevent them as well as how to avoid malware on Linux systems. Explore the top types of information security threats for IT teams and ways to prevent computer security threats from insiders. Understand the difference between malware vs. ransomware.
