Information Security
- Editor's letterWhat a proactive cybersecurity stance means in 2019
- Cover storyBattling nation-state cyberattacks in a federal leadership vacuum
- InfographicCutting SecOps breach response time is key to success
- FeatureTop 10 CISO concerns for 2019 span a wide range of issues
- ColumnCISO tackles banking cybersecurity and changing roles

pogonici - Fotolia
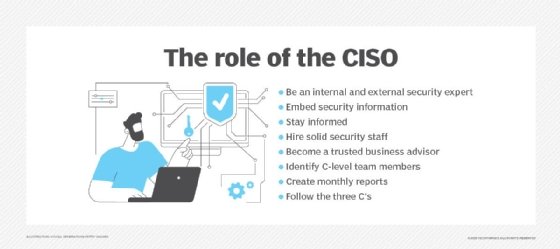
Top 10 CISO concerns for 2019 span a wide range of issues
From dealing with data and staffing shortages to adapting to an ever-expanding set of job responsibilities, CISOs face an array of serious issues in 2019.
When asked about the top CISO concerns he sees now, cybersecurity leader Robert LaMagna-Reiter said his own primarily involve taking a turn toward the business side. As the CISO at FNTS, an IT strategy and managed services company, LaMagna-Reiter wants his priorities list to more closely align with the stated top objectives of his company's business executives. It's a work in progress and a task he'll focus on in the upcoming months, he said.
"We've been striving to better communicate security risks, … to be better aligned, to make our KPIs [key performance indicators] more meaningful and to make our relationships more meaningful so -- as the organization's strategic roadmaps evolve -- we can communicate our value and the resources we need to do what we need," he said.
LaMagna-Reiter ticked off his priorities that are helping improve alignment: ensuring the security of cloud services for FNTS' holding company, First National of Nebraska Inc. and its other clients; implementing newer technologies, such as automation, into its security processes; and encouraging his staffers to build relationships with business-side colleagues as he is doing at the executive level.
 Robert LaMagna-Reiter
Robert LaMagna-Reiter
He said such work allows him to advance the strategic value of the CISO role and the security function within the organization.
"It's an iterative process that CISOs continue to refine," LaMagna-Reiter said. "Largely, we've been focused on the technical aspects since the inception of our defined role within an organization, but the strategic focus has become more important and a bigger part of the role as security has become elevated to the board and C-suite level."
As organizations finalize their cybersecurity budgets for the upcoming year, plot out their 2019 strategies and tweak their roadmaps for the months ahead, LaMagna-Reiter and other CISOs said several key issues will be at the forefront. The CISO concerns topping their priority lists include, first, the need to evolve the CISO role to a more strategic and business-focused position and then to use emerging technologies, address increasing regulations and mature practices to stretch security further beyond the boundaries of the enterprise itself.
"More CISOs are moving from being techies to really having to understand the business, the business risks and how business processes are supported by technology," said Ash Ahuja, CISO in residence and vice president of leadership for partner cybersecurity and risk management at Gartner. Then, from the security and risk perspective, CISOs have to understand whether they have enough monitoring and controls so they know what to do when something goes wrong, Ahuja added.
As they head into 2019, 10 CISO concerns are dominating the agenda:
1. Strategic alignment
Ahuja and others said one CISO concern is that only a minority of CISOs have evolved into strategically focused executive partners who align the cybersecurity function with organizational strategy, but they noted many CISOs are moving in that direction. To do that, they are increasingly building relationships with their executive colleagues, reporting to CEOs and engaging board members.
 Mansur Hasib
Mansur Hasib
CISOs should be developing strategic plans aligned with an organization's mission, something they should develop based on what the business articulates as its needs and appetite for risk, said Mansur Hasib, an author of Cybersecurity Leadership, a former CIO and chair of the cybersecurity technology program in The Graduate School at University of Maryland University College. CISOs should use these plans to articulate the value their team brings to the organization.
Hasib said all of this helps CISOs get the support and resources they need, thereby making them better able to deliver the security programs needed by their enterprises. "Once you have that framework, where everything you do ties into this framework," he added, "then you're not playing whack-a-mole with every new threat."
2. Regulations
Meeting existing regulations as well as new laws legislators are poised to pass also tops the list of CISO concerns as organizations and their security leaders head into 2019. Many anticipate growing public concerns about privacy and data breaches will spur increased enforcement of laws, such as the European Union's General Data Protection Regulation (GDPR).
"While not a completely new challenge for 2019, I expect to see increasing demand and challenges in complying with international security and privacy regulations. In the wake of GDPR, others are using it as a blueprint to enact more stringent compliance standards," said Tom Conklin, CISO at Druva, a data management-as-a-service company. The California Consumer Privacy Act goes into effect January 2020, and we should expect to see more of the same in the coming years," he added.
"Such regulations mean company obligations will become more complicated and will need to meet new standards," Conklin said. This would force companies to improve security "across the board," he continued. "Security and IT teams will have to prove they have fully captured risks to the organization and know where company data is being processed, how it is being used and how it is being protected."
3. Cloud security
 Ash Ahuja
Ash Ahuja
As more parts of the IT stack move to the cloud, security will continue to dominate the agenda in the year ahead, Gartner's Ahuja said. "That changing landscape keeps those security basics as an ongoing task. The work is never done; that's something CISOs are realizing."
Security leaders said the work includes improving network security and improving identity and access management practices, both of which become increasingly critical as more access and connection points move outside the walls of enterprise IT. Security leaders say such work must be done in addition to, not in place of, the work ensuring the security of legacy systems, however.
"We are in a transition state where more services are being consumed, but legacy on-premises data processing systems still exist. So now security teams need to be experts on both fronts," Conklin said.
4. Staffing
Omar F. Khawaja, CISO at Highmark Health, said his 125-member team is his No. 1 priority. "If I take care of my people, they'll do the right thing, and if they do the right thing, then the business and my customers will be happy," Khawaja said.
 Omar F. Khawaja
Omar F. Khawaja
Khawaja acknowledged personnel issues should be high on the list of CISO concerns; the need for high-level attention to personnel is something he learned during his five-year tenure at the healthcare organization. The staff attrition rate three years ago was in the 33% to 50% range -- about average for a field where the usual tenure for security professionals is two to three years. Now, he said his attrition rate among the employees he seeks to retain is less than 5%. Khawaja credited the policies he designed to better engage employees and identify personnel-related risks.
He said he is also working to empower his managers and staffers so they are able to handle all the tactical elements of the security function, leaving him to focus on the strategic elements that have become the chief component of the CISO role. "It's all about having the right person in the right role doing the best work of their lives," Khawaja added.
5. Emerging technologies
CISOs are turning to more emerging technologies to help them reach their security objectives, CISO Ahuja said. They're using artificial intelligence, machine learning, automation and orchestration. They're also using cloud-based security offerings that can garner threat information across multiple organizations to sort through the barrage of potential threats and identify the ones that really need attention.
Deploying more technologies in the security process is one of the priorities for Gary Hayslip, CISO at internet security company Webroot. "We're going to get an orchestration engine in place to sort out all the data and sort through the rules to identify the 'badness' so we can look at just that. Then we will tie the different technologies into it and create dashboards to get visibility into things like data flow and whether the data flow meets a certain level of risk that will kick off a service ticket and an SMS message to alert the lead to investigate," he said, noting this technology would automate what is today a manual process in his company.
6. Response and remediation
 Sam Olyaei
Sam Olyaei
Gartner analysts recommend security budgets be divided into three parts: protection; monitoring and detection; and response and remediation. Among others, Sam Olyaei, senior principal for security and risk management at Gartner, said this reflects the reality CISOs face -- that they will be breached, and, instead of focusing only on keeping bad actors out, they need to spend more on detection and remediation so they can appropriately react when the inevitable happens.
7. Expanding responsibilities
CISOs must also realize the scope of their responsibilities is expanding on a few fronts, Olyaei said. "They have to handle other risks -- such as supplier or third-party risks," he said, noting several high-profile breaches happened not only because of a weakness within the breached organization, but due to a lapse in a partner's security profile.
Given such realities, he said, leading CISOs are expanding their work to include security assessments of third parties. They're also responsible for sharing their own security profiles with third parties as well. "Businesses are being asked to showcase specific certifications or requirements by other businesses before they'll work together," Olyaei explained.
8. Larger attacks
Another of the leading concerns is the growing scope of attacks. "One of the biggest things I'm concerned about is the scale of attacks. I think it's only a matter of time before we see an attack that causes a large number of deaths," Webroot's Hayslip said. He believes the growing use of automation and orchestration can help counter that threat, as those technologies can help security teams focus only on the real threats and not waste time chasing false alarms. He hopes the push in business, and society overall, to talk not just about cyber-awareness but about cybersecurity as a safety issue will increase concern about potential threats and energize people to better prepare to thwart a major attack, or at least lessen its impact.
9. Dealing with data
Khawaja notes some reports estimate almost 50% of the data organizations store has no use or value. Eliminating unneeded data his organization stored is one of his priorities "because that would mean 50% less we have to safeguard."
Other security experts said stronger data governance is a priority for leading CISOs and their organizations. As a case in point, Gartner's Ahuja said some organizations are creating a data protection officer role that reports into legal but works with the CISO's office on how to best protect data in alignment with growing regulations.
10. Strengthening the foundation
Many CISOs still struggle with creating strong policies and practices around foundational security measures, Gartner's Olyaei said. As a result, basic security hygiene remains a priority for CISOs, both those who struggle with this and those who have more mature practices.
LinkedIn CISO Cory Scott said his security function "encompasses traditional information security, product security, and trust and safety operations," and noted his team has grown significantly over the past five years.
But Scott still focuses on the foundation as part of his overall security strategy as he heads into 2019. "I'm not crossing anything off the list, but I am generally pleased with the awareness that basic security hygiene -- asset management, patching and configuration management, collecting security telemetry, multifactor authentication -- is actually the most important thing to get right. I think we'll start to see a back-to-basics approach in 2019, based on these learnings."
Related Resources
Dig Deeper on Security operations and management
-
![]()
Quantifying cyber-risk at Netflix, Highmark Health: Case studies
By: Mary Pratt
-
![]()
Databricks boosts data security with AI-powered suite
By: Eric Avidon
-
![]()
Tata Communications hosted SASE claims to redefine networking, security
By: Joe O’Halloran
-
![]()
Optus earmarks A$140m to cover cost of data breach
By: Aaron Tan