
zephyr_p - stock.adobe.com
10 of the biggest cyber attacks of 2020
Here is a list of 10 of the largest cyber attacks of a pandemic-dominated 2020, including several devastating ransomware incidents and a massive supply chain attack.
A pandemic-focused year made the events of 2020 unprecedented in numerous ways, and the cyber attacks were no different.
As the world transitioned to virtual everything -- work, school, meetings and family gatherings -- attackers took notice. Attackers embraced new techniques and a hurried switch to remote access increased cyberthreats across the board. For example, K-12 schools took a brunt of the hit, and new lows were reached like the exfiltration of student data. The list of top cyber attacks from 2020 include ransomware, phishing, data leaks, breaches and a devastating supply chain attack with a scope like no other. The virtually-dominated year raised new concerns around security postures and practices, which will continue into 2021.
While there were too many incidents to choose from, here is a list of 10 of the biggest cyber attacks of 2020, in chronological order.
- Toll Group
Toll Group tops the list for the year's worst cyber attacks because it was hit by ransomware twice in three months. However, a spokesperson for Toll Group told SearchSecurity the two incidents were not connected and were "based on different forms of ransomware." On Feb. 3 the Australia-based logistics company announced on Twitter that it had suffered a cyber attack. "As a precautionary measure, Toll has made the decision to shut down a number of systems in response to a cyber security incident. Several Toll customer-facing applications are impacted as a result. Our immediate priority is to resume services to customers as soon as possible," Toll Group wrote on Twitter. The most recent attack occurred in May and involved a relatively new ransomware variant: Nefilim.
- Marriott International
For the second time in two years, the popular hotel chain suffered a data breach. On March 31, Marriott released a statement disclosing the information of 5.2 million guests was accessed using the login credentials of two employees at a franchise property. According to the notice, the breach affected an application used by Marriott to provide guest services. "We believe this activity started in mid-January 2020," the statement said. "Upon discovery, we confirmed that the login credentials were disabled, immediately began an investigation, implemented heightened monitoring, and arranged resources to inform and assist guests." While the investigation is ongoing, Marriott said it has no reason to believe that the information included the Marriott Bonvoy account passwords or PINs, payment card information, passport information, national IDs, or driver's license numbers. However, compromised information may have involved contact details and information relating to customer loyalty accounts, but not passwords.

- Magellan
On May 12, the healthcare insurance giant issued a letter to victims stating it had suffered a ransomware attack. Threat actors had successfully exfiltrated logins, personal information and tax information. The scope of the attack included eight Magellan Health entities and approximately 365,000 patients may have been impacted. "On April 11, 2020, Magellan discovered it was targeted by a ransomware attack. The unauthorized actor gained access to Magellan's systems after sending a phishing email on April 6 that impersonated a Magellan client," the letter said. The company, which has over 10,000 employees, said at the time of the letter they were not aware of any fraud or misuse of any of the personal information. Phishing, a common attack vector, intensified over the year as threat actors refined their impersonation skills.
The popular social media company was breached in July by three individuals in an embarrassing incident that saw several high-profile Twitter accounts hijacked. Through a social engineering attack, later confirmed by Twitter to be phone phishing, the attackers stole employees' credentials and gained access to the company's internal management systems; dozens of high-profile accounts including those of former President Barack Obama, Amazon CEO Jeff Bezos, and Tesla and SpaceX CEO Elon Musk, were hacked. The threat actors then used the accounts to tweet out bitcoin scams that earned them over $100,000. Two weeks after the breach, the Department of Justice (DoJ) arraigned the three suspects and charged 17-year-old Graham Ivan Clark as an adult for the attack he allegedly "masterminded," according to authorities.
- Garmin
The navigation tech supplier suffered a cyber attack that encrypted some of its systems and forced services offline. Though Garmin first reported it as an outage, the company revealed on July 27 that it was the victim of a cyber attack which resulted in the disruption of "website functions, customer support, customer-facing applications, and company communications." The press release also stated there was no indication that any customer data was accessed, lost or stolen. Speculation rose that the incident was a ransomware attack, although Garmin never confirmed. In addition, several media outlets reported that they gave in to the attackers' demands, and a ransom had been paid. Some news outlets reported it as high as $10 million.
- Clark County School District
The attack on the Clark County School District (CCSD) in Nevada revealed a new security risk: the exposure of student data. CCSD revealed it was hit by a ransomware attack on Aug. 27 which may have resulted in the theft of student data. After the district declined to pay the ransom, an update was posted saying it was aware of media reports claiming student data had been exposed on the internet as retribution. While it's unclear what information was, the threat of exposing stolen student data was a new low for threat actors and represented a shift to identity theft in attacks on schools.
- Software AG
The German software giant was the victim of a double extortion attack that started on Oct. 3, which resulted in a forced shutdown of internal systems and ultimately a major data leak. Files were encrypted and stolen by operators behind the Clop ransomware. According to multiple news outlets, a $20 million ransom was demanded, which Software AG declined to pay. As a result, the ransomware gang followed through with its promise and published confidential data on a data leak site including employees' passport details, internal emails and financial information. Operators behind the Clop ransomware weren't the only group utilizing a double extortion attack. The name-and-shame tactic became increasingly common throughout 2020 and is now the standard practice for several ransomware gangs.
- Vastaamo Psychotherapy Centre
The largest private psychotherapy provider in Finland confirmed it had become the victim of a data breach on October 21, where threat actors stole confidential patient records. The attack set a new precedent; rather than making demands of the organization, patients were blackmailed directly. As of last month, 25,000 criminal reports had been submitted to Finland police. In addition, the government's overall response to the incident was significant, both in urgency and sensitivity. Finland's interior minister called an emergency meeting with key cabinet members and provided emergency counseling services to potential victims of the extortion scheme.
- FireEye and SolarWinds supply chain attack victims
FireEye set off a chain of events on Dec. 8th when it disclosed that suspected nation-state hackers had breached the security vendor and obtained FireEye's red team tools. On Dec. 13, the company disclosed that the nation-state attack was the result of a massive supply chain attack on SolarWinds. FireEye dubbed the backdoor campaign "UNC2452" and said it allowed threat actors to gain access to numerous government and enterprise networks across the globe. According to a joint statement Dec. 17 by the Federal Bureau of Investigation, the Cybersecurity and Infrastructure Security Agency and the Office of the Director of National Intelligence, the attacks are ongoing. Additionally, the statement revealed that the supply chain attack affected more than just the Orion platform. CISA said it has "evidence that the Orion supply chain compromise is not the only initial infection vector leveraged by the APT actor." Since the statement, major tech companies such as Intel, Nvidia and Cisco disclosed they had received the malicious SolarWinds updates, though the companies said they've found no evidence that threat actors exploited the backdoors and breached their networks. However, Microsoft disclosed on Dec. 31 that threat actors infiltrated its network and viewed -- but did not alter or obtain -- the company's source code. Microsoft also said there is no evidence the breach affected customer data or the company's products and services.
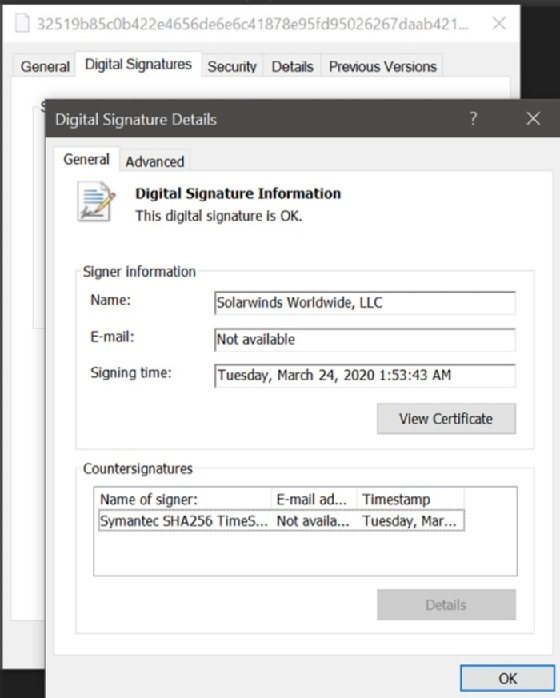
- SolarWinds
The scope of the attack, the sophistication of the threat actors and the high-profile victims affected make this not only the biggest attack of 2020, but possibly of the decade. The incident also highlights the dangers of supply chain attacks and brings into question the security posture of such a large company. Threat actors, who had performed reconnaissance since March, planted a backdoor in SolarWinds' Orion platform, which was activated when customers updated the software. SolarWinds issued a security advisory about the backdoor which the vendor said affected Orion Platform versions 2019.4 HF5 through 2020.2.1, which were released between March 2020 and June 2020. "We have been advised this attack was likely conducted by an outside nation-state and intended to be a narrow, extremely targeted and manually executed attack, as opposed to a broad, system-wide attack," the company said. In the three-week-long investigation since, the full breadth of the attack has grown immensely, but is still not yet fully understood.







