
Getty Images
17 Discord malware packages found in NPM repository
These latest reports of Discord malware follow a trend of threat actors using open source software repositories to host malware, two JFrog researchers said.
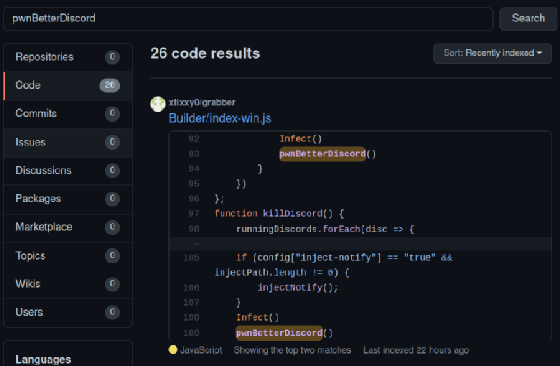
Seventeen malicious packages targeting Discord users have been found in the open source Node.js package manager repository, according to new research by DevOps automation vendor JFrog.
In a blog post published Wednesday, JFrog security researchers Andrey Polkovnychenko and Shachar Menashe detailed how the malicious NPM packages took aim at the popular communications platform with malware and infostealers, including Discord token grabbers; stealing a user's token would give a threat actor complete control over a user's account.
JFrog hypothesized in its blog post that threat actors could use Discord tokens -- and by extension, the attached account -- for botnets, spreading malware and to resell stolen accounts if the users have Discord's premium Nitro service.
Menashe told SearchSecurity the packages were found during routine scanning of the NPM repository.
"We are constantly running our malicious code scanners on popular package repositories, including npm," Menashe said in an email. "The malicious packages were tagged by our scanners, and we later verified manually that these are indeed malicious packages and did a full assessment of the impact. You can see that we've also disclosed several packages which aren't related to Discord (prerequests-xcode, 'wafer-*' packages, and more)."
Cybercriminals targeting the popular communication platform is not a new phenomenon. A report from Cisco earlier this year described both token stealing and malware delivery via file attachments. Sophos, similarly, released research in July about how threat actors are targeting Discord users with malware.
The malicious packages referenced in JFrog's blog were discovered in the NPM repository. Node.js is an open source Java runtime environment used by a number of major enterprises, including Discord.
Polkovnychenko and Menashe warned that threat actors' use of open source repositories for malware hosting is an ongoing trend.
"We are witnessing a recent barrage of malicious software hosted and delivered through open-source software repositories," the blog read. "Public repositories have become a handy instrument for malware distribution: the repository's server is a trusted resource, and communication with it does not raise the suspicion of any antivirus or firewall. In addition, the ease of installation via automation tools such as the npm client, provides a ripe attack vector."
Another example can be found in JFrog research last month, where they found Python malware imitating signed Python Package Index (PyPI) traffic. Further, Menashe pointed out that GitHub decided last month to require two-factor authentication on accounts using popular npm packages.
A Discord spokesperson shared the following statement with SearchSecurity.
"Platform security is a priority for us," the spokesperson said. "Discord relies on a mix of proactive scanning -- such as antivirus scanning -- and reactive reports to detect malware and viruses on our service before they reach users. We also do proactive work to locate and remove communities misusing Discord for this purpose. Once we become aware of these cases or bad actors, we remove the content and take appropriate action on any participants."
Alexander Culafi is a writer, journalist and podcaster based in Boston.







