Alex - stock.adobe.com
Implement zero trust to improve API security
Not all organizations have an API security strategy in place. Using zero trust in API security is one way to protect APIs and reduce their changes of being attacked.
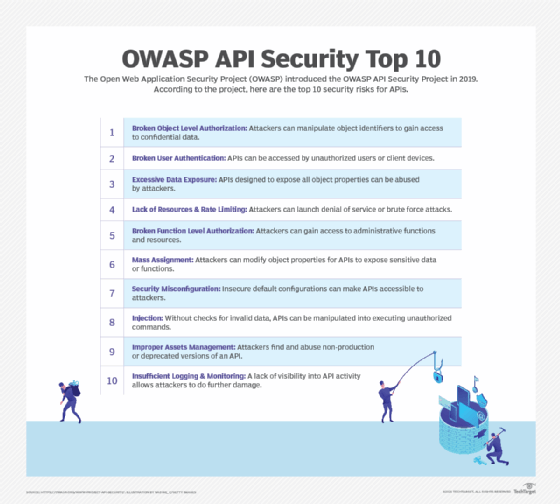
APIs provide an integral lifeline for technology interactions, enabling not only connections between modern applications, but also a conduit to work with legacy infrastructure. This connective tissue is a ripe target for attack, however. Content delivery network vendor Akamai reported a 167% increase in web application attacks from 2021 to 2022, and Gartner predicted APIs will become the primary web app attack vector in 2023.
One way to mitigate API attacks is to implement zero trust to secure APIs. A zero-trust framework assumes users and devices are untrustworthy by default. Continuous authentication and authorization then verify if a device or user remains trusted. Even then, only minimum access is provided during a limited time frame.
Here are four ways to use zero trust to keep APIs secure.
1. API inventory, assessment and remediation
Zero trust requires an understanding of the existing attack surface. So, the first step to securing APIs is to discover and inventory all APIs in use, assess them for continued use and potential risks and weaknesses, and remediate any issues found, if necessary.
API discovery tools help find and evaluate all APIs within the IT infrastructure, whether the API is public-facing, internal or connected to legacy applications. The tools may also discover functioning APIs connected to decommissioned applications.
After the discovery and inventory phases, determine whether given APIs should remain in use, how secure they are and how to secure them moving forward. From there, remediate vulnerable APIs or decommission those no longer needed.
2. API data access assessment and policy control
With an inventory in place, document and manage what data APIs have access to. Use tools such as cloud database management software for information about what data APIs are currently accessing. Reassign or tighten API data access rights as needed via access control mechanisms in the database.
Create and apply zero-trust policies for APIs. For example, use data security policies to control data access. In a policy, lay out which users and roles can access different data types, when they can access it and where they can access it. Use this information to ensure only active and secure APIs access data they are allowed to within an infrastructure.
Also, consider if the data accessed by decommissioned APIs should be investigated further or destroyed to reduce risk.
3. API authentication and authorization
Authentication and authorization are important principles for implementing zero trust. Look at how users and devices can interact with APIs. Consider each API a resource, and require users and devices to authenticate and authorize before allowing access.
API access should use granular zero-trust access policies, such as the principle of least privilege. To authenticate API traffic, implement standards such as OpenID and OAuth 2.0. Additional authentication methods to consider include API keys, HTTP authentication and JSON web tokens. The best API authentication method varies depending on a specific API and its uses. For example, API keys are often used for simpler API requests and aren't as secure as OAuth or JSON web tokens.
4. API rate limiting
Implement API rate limiting to help prevent API attacks, such as DDoS attacks. Malicious attackers use DDoS attacks to flood API services with an overload of API calls. More sophisticated DDoS attacks use bots to deploy more CPU- or memory-intensive API calls to degrade services.
Specifically, brute-force rate limiting restricts the number of API calls per minute or per hour using a set upper limit -- anything above the upper limit is automatically rejected. More sophisticated rate limiting restricts API calls based on day, time, geolocation or frequency of use.
For further API protection, implement additional API security best practices, such as encrypting requests and responses, recording APIs in an API registry and stashing API keys.