
Getty Images
Use shadow IT discovery to find unauthorized devices and apps
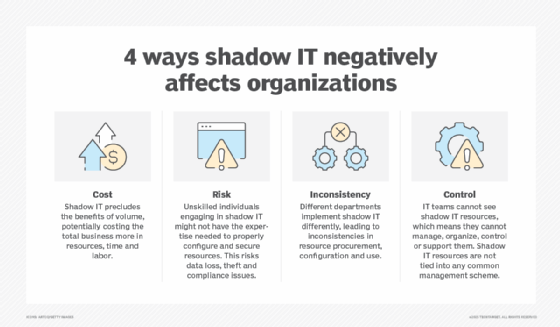
Shadow IT may be convenient for users, but it isn't for IT -- especially where security is concerned. Shadow IT discovery finds unmanaged devices and apps.
The acquisition and unauthorized use of hardware, software, services and media by users or groups within an organization is known as shadow IT -- and it's a rampant trend across companies.
Shadow IT often occurs because people want to use the devices and apps they like and are comfortable with rather than the ones available from IT -- and they perceive the IT department as an obstacle or source of delay if they want to get preferred devices and apps approved.
Unfortunately, IT departments can't secure resources they don't know about, leaving sensitive data unprotected. This may violate laws, regulations and corporate policies and even enable major data breaches.
Shadow IT discovery is needed to collect information on potentially unauthorized resources and enable risk assessments and informed decision-making on which resources should become authorized and which should be blocked.
Learn how to perform shadow IT discovery in three categories: unauthorized devices, local software and removable media, and cloud services. Note, multiple methods should be used in combination to keep shadow IT at bay.
Shadow IT discovery for unauthorized devices
Finding unauthorized desktops and laptops, mobile and IoT devices, and other hardware is generally straightforward. When these devices try to connect to corporate networks and servers -- either on premises or remotely via technologies such as VPNs, security service edge or Secure Access Service Edge -- they contact your networking devices. These can include network switches, wireless access points, VPN gateways, proxy servers, firewalls and routers. Such networking devices can identify outside devices they've never seen before and collect information on them.
Many enterprises use onboarding or provisioning processes for new devices. In conjunction with asset management tools or network access control technologies, these processes can automatically generate allowlists for network access. Every time a device tries to connect to the network that isn't on an allowlist, a shadow IT device may have been discovered.
Shadow IT discovery for local software and removable media
Endpoints authorized to connect to a corporate network often use unauthorized software or removable media. If the endpoints are managed, the enterprise endpoint management software is ideal for shadow IT discovery. Endpoint security tools, such as vulnerability scanners, patch and configuration management utilities, mobile device management and asset management tools, can collect information on unauthorized installed software.
Monitor virtual endpoints, such as emulated OSes running on top of other OSes. Virtual endpoints can also have unauthorized software installed, or the emulated OS itself might be unauthorized.
Shadow IT discovery for cloud services
The use of unauthorized cloud resources is a major concern today. Users can easily access free and low-cost SaaS offerings on demand. While cloud services can increase productivity, they can also enable third parties to access the organization's sensitive data due to lacking SaaS safeguards.
Cloud-based shadow IT use can be identified in many ways. The best methods for your organization depend largely on what security tools are already in use. Consider the following options:
- Cloud access security broker tools and cloud app security tools provide enterprise security capabilities, including tracking cloud use and collecting information on which users and devices are involved and what they're accessing.
- Most SaaS management tools support cloud app discovery. Some provide risk ratings for common shadow IT resources to help with risk assessment.
- Endpoint management software may be able to monitor and log SaaS use from managed endpoints.
- Web activity can be monitored at proxy servers, firewalls and other major network points to identify connections to unauthorized cloud-based resources. DNS requests can also provide basic information on attempts to access known shadow IT resources.








