Getty Images/iStockphoto
What are the pros and cons of shadow IT?
The increase of generative AI, digital natives and remote work drives the rise of shadow IT. CIOs and IT leaders should evaluate the pros and cons to mitigate potential risks.
Most organizations have elements of shadow IT running within their environment, according to analysts, reports and veteran CIOs. That can be good, bad or both, depending on who's speaking.
Shadow IT -- technology created, purchased, deployed or managed by workers without the IT team's knowledge or consent -- is a reality of modern life.
Forty-one percent of employees acquired, modified or created tech outside of IT's visibility in 2022, according to research by Gartner published in 2023. That number will climb to 75% by 2027.
Workers have good reasons for adopting their own tech: They want a way to do their jobs better, more quickly or with less effort and, thus, turn to deploying their own apps to do so. Employees commonly turn to unsanctioned email accounts, messenger platforms, video conferencing products, collaboration tools and file-sharing services, among other tools. They're increasingly using more sophisticated technologies, such as automation and generative AI.
The significant amount of shadow IT that employees use within the enterprise is a longtime challenge for many CIOs and IT leaders. As a result of unsanctioned technology, CIOs and IT leaders often face increased security risks, costs and maintenance issues.
Those issues can be managed with policies and procedures, experts said.
With such controls in place, experts believe CIOs can harness the benefits of shadow IT while mitigating potential problems.
"Too many people, and CIOs in particular, put too much emphasis on the reasons why not to allow shadow IT," said Sue Bergamo, CIO and CISO at BTE Partners, based in Boston. "But if they understand how to work with their business partners to secure and control what happens, they could embrace shadow IT and see some positives."
Here's what CIOs and IT leaders should consider about the pros and cons of shadow IT.
The pros of shadow IT
Although generally considered a risky practice, there are some potential benefits to shadow IT. For example, this approach could increase productivity and innovation as employees use the tools and software that they're most familiar with. However, it's important to note that any potential benefits must be weighed against the likely security risks and the need for proper oversight and governance of IT systems within the organization.
Shifts lower-level tasks out of IT
Employees often deploy shadow IT to help them do their jobs more efficiently. So, seeking out the apps that work for them in such cases can free up IT resources to address the larger challenges that will let IT deliver business value.
"There is [typically] a backlog of demand for IT services," said John Annand, research director of infrastructure and operations at Info-Tech Research Group, headquartered in London, Ont.
Also, workers might resort to shadow IT when they notice a gap.
Enterprise IT teams generally can't get to the smaller tech initiatives that typically get handled by tech-savvy workers, which is then labeled shadow IT, he said.
Thus, dependence on shadow IT can relieve IT departments of less important tasks.
"Enterprise IT has more than enough interesting work to do, and IT doesn't have the time to serve those hundreds, or even thousands, of smaller jobs anyway," Annand said.
Expands innovation efforts
IT departments have policies and processes that guide technology development and deployment. Although those policies and processes provide value in guiding tech initiatives, they sometimes slow innovation and transformation.
But because shadow IT circumvents all that, the approach can foster innovation among users who "want new ways of doing tech," Annand said.
The number of employees often affects key IT projects.
Organizations have many more non-IT workers than they have IT staffers, he said.
So, shadow IT can be a meaningful way to supplement the innovation efforts happening within the IT department itself.
Speeds up delivery of tech
Even in the age of agile software development, many IT teams struggle to promptly address every request for new features or functions. Indeed, most IT departments and agile product teams prioritize requests expected to deliver the most value. That leaves a lot of lower-value requests far down the to-do list.
"So, shadow IT can get tech to users faster," Josh Lazar said, founder and CEO of technology services firm TechThinkTank, headquartered in Orlando, Fla.
Highlights innovative workers
Shadow IT can help IT leaders identify the organization's most digitally savvy, non-IT employees and tap them for future initiatives.
Such users could become effective liaisons between the organization's siloed units and the IT team, helping to improve communication and collaboration, Lazar said.
CIOs and IT leaders might uncover hidden tech talent to help nurture the company's critical IT processes.
They could become key players on agile development teams, which rely on users for identifying and iterating required tech features, functions and tools, he said. Or they could be recruited to join the IT department.
Improves company operations
Workers tend to create or bring in their own tools because they're seeking ways to do their jobs more effectively. Or they do so to enhance teamwork and other soft skills.
Users are best positioned to determine their pain points and areas for improvement, noting that few -- if any -- IT staffers understand the complexities of a particular company process or workflow as well as those who do the work, Lazar said.
Consequently, their tech selections might better target what they need, which could boost the company's overall productivity.
"Shadow IT works well when it allows people to be as efficient as possible," he said.
Delivers software that fits organizational needs
One key aspect of an IT department is to keep up with an ever-evolving tech landscape or maintain legacy systems that serve the company's daily needs. It's crucial to involve users in the decision-making process to determine the most suitable option.
Shadow IT helps the company get what it wants by eliminating users having to explain what they require to technologists -- a step that often results in misunderstandings, Annand said.
However, conventional communication channels might be insufficient between the IT department and the rest of the organization.
"With shadow IT, nothing is lost in translation," he said.
In other words, shadow IT puts problem-solving in the hands of those who know the problem best.
Helps IT identify delivery gaps
It's not uncommon for an organization's IT department to overlook certain areas where their service delivery might be lacking. This drawback could arise from issues like limited resources or inadequate visibility into the end-user experience.
Shadow IT typically happens only when business units feel they're not getting what they need from the tech that IT implemented, said Shruti Sridhar, a cybersecurity, risk and compliance management professional and a member of the Emerging Trends Working Group with the governance association ISACA.
By identifying these gaps, the IT team can take corrective measures.
Consequently, shadow IT can show IT departments where they need to improve delivery and work to better understand company needs and processes, she said.
Higher user satisfaction levels
Users who develop their own apps are typically more tuned in to the tech's limits; they have more right-sized expectations. So, they're more likely to be satisfied with what they create.
Compare that to when they're handed a brand-new tool from IT, where the IT team frequently expect perfection and don't recognize that technology often comes with some downsides.
"When users are creating the solution, you get less finger-pointing when it's not perfect," Annand said.
The cons of shadow IT
Shadow IT poses several challenges to companies, including security risks, lack of standardization and potential data breaches. These activities can also lead to financial losses and decreased productivity. To mitigate these drawbacks, organizations should be proactive in identifying and managing any shadow IT activities.
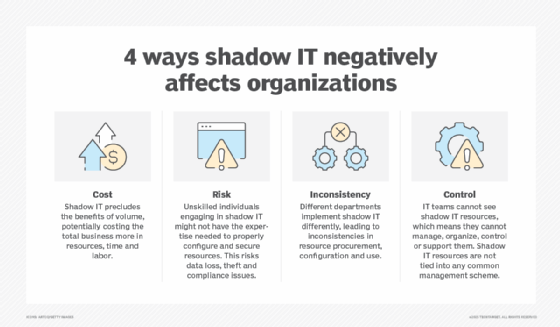
Rings up extra costs
The practice of shadow IT can lead to additional costs, especially in organizations with limited financial resources.
Even though business units often pay for shadow IT from their budgets, the enterprise might feel the pinch of higher costs of letting unsanctioned technologies proliferate, Bergamo said.
To start, the organization might be paying twice for the same capability -- paying for both unsanctioned tech and an equivalent enterprise software program. Or it could be paying premium rates for the unsanctioned tech rather than the better rate typically negotiated by a procurement team.
Shadow IT often comes with hidden costs that add up over time, Sridhar said.
Users don't always factor in licensing fees and associated costs, such as storage fees. Nor do they calculate the expenses for ongoing maintenance and management.
Those aren't the only surprise costs, said Saurajit Kanungo, president of the consulting firm CG Infinity, headquartered in Plano, Tex.
Service providers sometimes offer promotional rates to organizations, which might help reduce short-term costs. However, these rates often have an expiration date.
Company units often see introductory rates and not the regular rates, leading to surprise bills once the trial time is over, Kanungo said.
Increases cybersecurity risks
Employees using unsanctioned tools without proper oversight can lead to various cybersecurity threats.
As workers develop and deploy technology without any reviews or security assessments, they often increase the organization's exposure to various risks, said Kayne McGladrey, a senior member of the IEEE and field CISO at Hyperproof, a compliance management software company, based in Seattle.
Employees should be aware that the IT department conducts thorough research to ensure the organization's technology is safe and compliant with company policies.
The technology itself could be vulnerable to cyberattacks, as unauthorized tech rarely goes through the same level of scrutiny that technology selected and onboarded by IT does, he said.
The practice of shadow IT could open the organization to critical weaknesses.
Hackers are known to look for such vulnerabilities, further upping the cybersecurity risk, McGladrey said.
IT teams might face challenges in managing unfamiliar technologies not approved by the organization.
As the unauthorized technology falls outside of IT's knowledge and control, the IT team might have less visibility into and a diminished ability to monitor its use, he said. That means IT might not quickly detect nefarious activity.
Such practices could lead to potential long-term delays in addressing cybersecurity issues.
"Shadow IT might make it harder for the company to even know it has been breached," McGladrey said.
Puts proprietary and protected data at risk
Organizations take various measures to prevent key data from unauthorized access. However, employees relying on shadow IT could put the company at risk of significant financial and reputational damage.
Shadow IT often exposes sensitive data to theft, compliance and regulatory violations, McGladrey said.
As access to new tools grows, employees must carefully adhere to the organization's strategy for emerging technologies.
Executives have seen such incidents as workers using ChatGPT and other GenAI tools without authorization, he said. In some cases, employees put proprietary or regulated data into these tools and subsequently exposed that data to the public.
At the same time, employees who use unauthorized AI tools could receive inaccurate or biased results -- something that might not be caught if the tools are outside of IT and the governance that IT applies to such technologies.
All those scenarios expose the enterprise to legal, compliance and regulatory risks, McGladrey said.
Introduces performance and user experience problems
Shadow IT can cause app performance issues, user experience problems and outages. That's because the tools typically don't undergo rigorous review, the design and configuration planning, or the testing that IT applies when deploying new tech.
For example, there have been cases where the company's security software mistakenly identified a misconfigured unauthorized app as a breach and shut down the network, Sridhar said.
Runs afoul of vendors' licensing requirements
Users who deploy technology without IT's input might unwittingly expose their organizations to problems with vendors.
"They're not negotiating contracts, and they're not looking at the fine print in the contracts," Kanungo said.
That's particularly true as more workers use unauthorized apps without securing needed licenses or agreements with the vendors.
This scenario could bring big fees for unauthorized, unlicensed use of the software, he said.
Creates maintenance and governance challenges
IT cannot provide support for any unauthorized tech introduced to the organization.
Shadow IT often creates maintenance and governance challenges because it doesn't get the same documentation and management attention that the IT team applies to the technology it deploys, Lazar said.
Those challenges often come up when the shadow IT needs updates or becomes glitchy, he said.
Problems also arise when the worker who first created or deployed the tech moves on, leaving others to puzzle over the tech's origins, licenses, updates and other issues.
"You don't want to be in a situation where no one knows who the administrator [for the technology] is," Lazar said.
Ignores questions of scalability, maintainability and availability
Shadow IT can also introduce problems as more workers try to use it and the longer it stays in use, Kanungo said.
Users typically don't have the skills to assess a technology for its ability to scale or its long-term viability, so they sometimes deploy tech that can't handle the anticipated volume of work or can't keep up with changing company or IT environments, he said.
The technology then becomes more of a hindrance than help for both the business unit and IT, who ends up having to maintain it.
Making shadow IT work for the enterprise
Many CIOs are concerned about the risks of shadow IT, even as they acknowledge the benefits.
For example, 69% of tech execs consider shadow IT as a top security concern, according to the 2022 "State of SaaS Visibility and Impact Report" from software company Torii.
One approach is to implement procedures that allow users to bring in their own technology, but only if they follow the rules established by IT and security to keep the organization safe.
"CIOs need to partner with the business and agree on what should be done, where IT should extend a hand and where the business needs to extend a hand back," Bergamo said.
IT needs to establish security and data-related guidelines that users can follow when deploying technology independently, Annand said.
Additionally, IT needs to deploy policies and technology that control access to and use of sensitive data so that shadow IT doesn't put that data at risk, Annand said. IT and organization leaders should agree on policies for ongoing governance, maintenance and funding.
Such steps help move shadow IT out of the dark, where it is likely to be more beneficial and less risky, Annand said. At that point, it stops being shadow IT and becomes an IT-managed app.
Mary K. Pratt is an award-winning freelance journalist with a focus on covering enterprise IT and cybersecurity management.