
Alex - stock.adobe.com
8 dangers of shadow IT and how to manage them
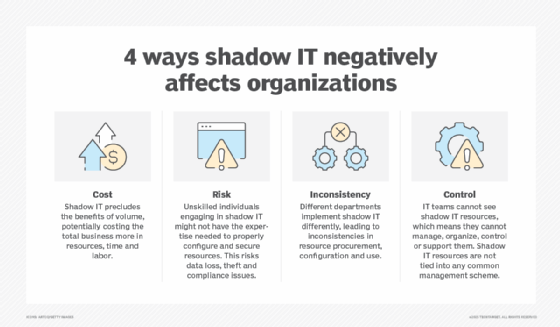
Unauthorized devices, software and system changes -- and other forms of shadow IT -- can expose organizations to a range of security risks. Here are ways to manage them.
If an ounce of prevention is worth a pound of cure, then CIOs and their teams should be aware that allowing shadow IT can weaken an organization in more ways than one. But there are ways to minimize or eliminate the dangers.
Shadow IT occurs when employees get frustrated by the IT department's slow response to trouble reports, refusal to update a system or another situation where IT is not accommodating user requests or complaints. This frustration can result in the creation of an invisible or "shadow" IT activity, usually by employees with IT skills willing to bypass IT policies and procedures to get what they want.
When a shadow IT activity emerges, IT teams and company management might experience significant repercussions, especially in the form of cybersecurity risks. Examples of shadow IT activities that could lead to critical security incidents include employees using unauthorized devices and software, bypassing device security access protocols and making changes to system parameters without permission.
These actions can result in loss of control over IT operations. There's also the potential reputational damage to the organization, such as if improperly performing systems interact with customers. Shadow IT could also grant access to hackers and other unauthorized cyber attackers through misconfigured security resources.
Here's what CIOs and IT leaders should understand about the dangers of shadow IT.
8 dangers of shadow IT
By recognizing that shadow IT is a real threat that can occur quietly and without visible evidence, company leaders must proactively search their infrastructures to discover and address suspicious behavior. To help that process, the following list can help company leaders identify common shadow IT risks, along with guidelines for remediation.
1. Unauthorized access to data
A key form of audit control is ensuring that only authorized users can access IT systems and resources. Several access controls and technologies are available to ensure the organization complies with regulations and standards as well as holds up under audit scrutiny. Two important controls are the use of role-based access, which restricts access to company resources based on an individual's role, and multifactor authentication, which requires multiple authentication methods to verify a user's identity before granting access to the system. Unauthorized access to production systems can result in significant risks, such as data loss, damage to applications, information theft and malware.
2. Unauthorized changes to data
Someone with unauthorized access can potentially change critical data, such as customer data, databases and content used in daily company operations, with potentially disastrous effects. For example, changing a single character in a patient's health record could result in a misdiagnosed condition or the patient receiving the wrong medication. If detected, such changes could violate data privacy laws and regulations, resulting in potential litigation and fines.
3. Physical access to IT systems
Employees that have or can fraudulently obtain access to data centers, equipment rooms on different floors and other locations with IT assets can create security issues. Placing cameras at entrances and reviewing access logs can reduce the possibilities of unauthorized entry.
4. Introduction of malignant code
When shadow IT activities occur, there is the risk of introducing malicious code into production systems both intentionally or unintentionally. Shadow IT activities also make organizations more vulnerable to ransomware attacks.
5. Inability to properly patch
Patching is a critical activity that ensures all production systems, cybersecurity and network devices, utilities, and other code-based resources are updated with the latest features and security provisions. These patches can minimize the likelihood of cyberattacks. External shadow IT activities that affect patching schedules could create unexpected performance and security issues, such as launching an incorrect patch or a patch at the wrong time.
6. Compliance issues
Regulated organizations, such as financial institutions and government agencies, and companies under close government scrutiny, such as healthcare organizations and utility companies, can't afford to become noncompliant with regulations. Shadow IT activities could inadvertently create problems that result in out-of-compliance conditions, such as system failures or generating incorrect performance data. In situations where compliance is regularly monitored and reported, shadow IT could create noncompliant conditions that, if discovered, could potentially result in fines and litigation.
7. Cybersecurity risks
Preventing and dealing with cybersecurity breaches is a top priority facing IT teams across sectors, and hackers often get into organizational systems because of shadow IT. Shadow IT activities involve using unauthorized systems, resulting in security gaps such as breaks in firewalls or failures to update firewall rules regularly. Internal shadow IT activities could compromise existing security software such as virus detection, anti-phishing or security equipment, such as an intrusion detection system and an intrusion prevention system.
8. Reputational risks
In addition to system-related issues, shadow IT can cause software breaches and performance problems that damage an organization's reputation, competitive position and financial standing. The failure to quickly discover and terminate shadow IT activities could result in complaints from customers and stakeholders that could damage the company's reputation.
How to manage shadow IT risks
Diligence and awareness are two key management attributes that can identify potential shadow IT activities. For example, if the volume of complaints about IT support activities increases, technology teams should carefully review each report, especially from employees with repeat complaints. When teams identify any notable IT performance issues, they should fix them as soon as possible. Then they can monitor help desk activities to see if the number of complaints declines.
Clues can point to possible shadow IT activities that CIOs and IT leaders should keep top of mind. These might include issues involving slower response times and application execution times, network throughput delays, missed dates and times for execution of batch jobs, and short-duration system outages for less than 10 minutes. While any of these could simply be normal performance issues, they might also be the result of behind-the-scenes shadow activities. Company leaders must take each of these events seriously and conduct prompt investigations.
Additional proactive measures to reduce the likelihood of risks from shadow IT activities include the following:
- Use network sniffing programs that detect IP addresses not in the known list of IP addresses.
- Keep a current inventory of all IT infrastructure resources up to date.
- Run inventory and asset software that identifies new devices on a regular basis.
- Analyze email traffic to identify suspicious activities and attachments.
- Have senior IT leaders identify possible shadow installations.
- Discuss shadow IT activities at staff meetings.
- Keep firewall rules current for both inbound and outbound traffic to identify suspicious traffic.
- Ensure intrusion detection and intrusion prevention system rules are up to date.
- Keep employees aware of possible unauthorized logins via emails, messages on intranet sites and other alerting systems.
- Educate and encourage employees to report any suspicious activity to the IT help desk.
- Ensure that IT teams regularly brief senior management on suspicious IT activity and measures to remediate it.
- Ensure that managed service firms and cloud service organizations monitor company resources and provide alerts if they detect suspicious activity.
- Engage shadow IT analysis capabilities of cloud-based and other managed service providers if they are available.
- Consider the use of third parties with experience in shadow IT detection.
- Establish policies and protocols for managing shadow IT activities.
- Partner with HR and legal departments to define penalties for employees who conduct shadow IT activities.
- Update the existing bring your own device policy to address shadow IT.
- Establish and maintain a file of evidence on shadow IT activities for future audits and management review.
- Consider deploying shadow IT detection tools.
Shadow IT is serious business
Shadow IT activities are a serious threat to IT organizations and need swift handling. As these activities often evolve from dissatisfaction with how an IT department handles customer service, consider elevating help desk and other customer service activities to a higher priority. Regularly review IT department performance, e.g., help desk and operations, to identify potential occurrences of shadow IT.
Paul Kirvan is an independent consultant, IT auditor, and technical writer, editor and educator. He has more than 25 years' experience in business continuity, disaster recovery, security, enterprise risk management, telecom and IT auditing.








