
Getty Images
17 potential costs of shadow IT
Companies should be vigilant and consider the significant costs associated with shadow IT. Learn about these overlooked issues and how they affect the organization.
To avoid unexpected expenses, CIOs and IT leaders must ensure a safe and secure IT environment aligned with the company's objectives.
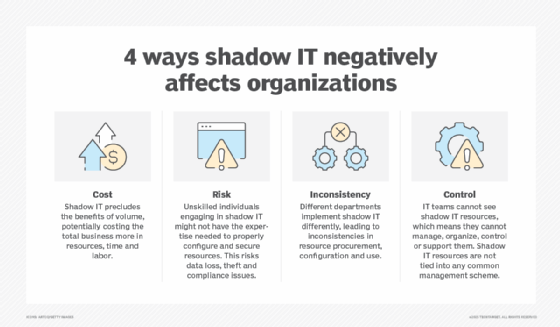
One way for organizations to best protect themselves against potential security breaches is by proactively identifying and addressing shadow IT activities. Shadow IT refers to the use of systems, devices, software or services by employees or departments without the approval or knowledge of the company's IT department. These activities can result from employees who believe that they can solve persistent IT issues without the IT department's help. IT leaders' efforts to identify, prevent and mitigate the effects of shadow IT can add unplanned financial burdens to already-limited budgets.
Savvy CIOs and IT leaders understand the importance of proactively searching out unauthorized and rogue IT activities to maintain a smooth-running IT environment. While not all shadow IT activity causes problems, the potential for harm exists. Companies might face costs of varying degrees, especially those associated with discovering the activity, mitigating it and dealing with the long-term employee and business issues that might arise.
Here are some of the potential costs of shadow IT.
The pitfalls with people
One of the challenges with shadow IT is dealing with the human side of tech. Some employees might be more comfortable using specific, but unauthorized, software to complete their daily tasks. However, there are drawbacks to allowing this to happen. They include the following:
- Dealing with employees. Companies might need to spend money, time and other resources dealing with suspected shadow IT users. This concern can include discovering the perpetrators, gathering evidence, identifying consequences of shadow activities and resolving any tech issues.
- Retaining legal expertise. Organizations without a legal department might need external guidance. For example, retaining legal counsel with expertise in IT operational litigation falls into this category. The active involvement of HR teams is critical at this point.
- Prosecuting employees. If company policy mandates termination due to a security issue, a company might incur legal costs if an employee fights a termination. HR should be an active participant in this process.
How shadow IT affects the business
CIOs and IT leaders should understand that taking a strong stance against shadow IT has positive effects throughout the company. However, ignoring or downplaying these unsanctioned activities means potentially exposing the entire organization to the following:
- Addressing disrupted IT operations. Companies might need to deploy tech to identify shadow IT activities, along with requiring resources to recover affected production systems. A disaster recovery plan (DRP) might need to be activated, based on the damage.
- Addressing mission-critical systems and processes. Organizations must remediate and relaunch systems if shadow IT affects specific mission-critical systems. To minimize downtime, companies should back up critical systems and data regularly, along with deploying a DRP.
- Identifying and managing risks. Periodic risk assessments (RAs) are advisable to identify situations that could evolve into shadow IT or other rogue activity. Disruptions to IT operations are serious threats to the business, and investing in RAs might help prevent the problems before they occur. HR advice and counsel are valuable in such RAs.
- Dealing with lost productivity. Lost productivity costs could be significant, particularly if shadow IT disrupts IT operations. Once the IT team identifies lost productivity, reestablishing a business-as-usual state could be a resource- and cost-intensive process. If business operations are disrupted, it might be necessary to activate DR and business continuity plans.
- Hiring external tech expertise. Companies might require external support, such as vendors and consultants, if shadow IT causes significant disruption. Firms with experience in penetration testing, social engineering and other security threats are advisable.
- Addressing compliance irregularities. Regulated organizations or those that must comply with specific regulations, such as HIPAA, the Gramm-Leach-Bliley Act or the Sarbanes-Oxley Act, could face legal and financial penalties if shadow IT causes noncompliance. Even firms not governed by specific regulations should have something in place, e.g., IT security policies, to address unauthorized IT activity.
- Paying higher business insurance premiums. Claims associated with shadow IT activities might increase business insurance premiums, such as liability or loss of assets. Cybersecurity insurance might be advisable if the shadow IT activities lead to a surprise security breach that results in a ransomware attack.
- Repairing reputational damage. While never an easy issue to compute in terms of financial effects, organizations can address reputational damage using companies that specialize in protecting and repairing how the public and other stakeholders view the organization.
Issues with technology and facilities operations
If organizations allow shadow IT activities to occur, the effects not only compromise data security, but can lead to software incompatibility issues and increase the risk of system failures due to ransomware or information security issues. Specific challenges that facilities might be facing include increasing the complexity of managing compromised infrastructure and creating additional demand for power, cooling and other resources. Minimizing these long-term effects might start with the following:
- Buying specialized hardware and software. Various systems can help identify and track suspicious IT activities in a company's IT infrastructure. Companies might need additional software licenses, maintenance, patching and vendor technical staff because of shadow IT damage and the painstaking efforts to deal with the consequences.
- Specialized third parties. Securing the assistance of external firms that deal with suspicious IT activity and related human-focused issues can be an important investment. Forensic specialists, experts in penetration testing and inventory discovery, and psychologists and others who understand human behavior could be essential partners when addressing a suspected shadow IT problem.
- Cloud access security broker (CASB). A prospective resource to help address shadow IT is a CASB. Often associated with cloud service vendors and data centers, CASBs monitor data traffic of all kinds, particularly cloud-based activities, to discover suspicious activities. The tool functions as an arbitrator of data traffic, based on internal rules and policies established by the cloud vendor or the IT department using the software. Anything that appears suspicious or violates these predetermined rules can be flagged.
- Dismantling shadow IT activities. Once IT teams identify egregious shadow IT activities, they need to shut down activity as soon as possible or move into an operating environment securely firewalled from other IT production systems, depending on company policy. This issue exemplifies why a regular cadence of backing up IT systems and company data is critical.
- Reconfiguring disrupted or compromised network resources. Reconfiguring affected network routing and termination points can be costly. This challenge can include repairing or replacing servers, routers, power systems and other assets. Companies might incur additional costs if network services are rerouted or reconfigured.
- Addressing data center infrastructure issues. Organizations with large data centers must proactively ensure the integrity of those centers. More critically, CIOs and IT leaders must address disruptions to physical security systems as quickly as possible to prevent unauthorized access. While the installation of cameras and motion detectors is an important deterrent, it might also be useful to retain vendors and consultants with data center security expertise.
Paul Kirvan is an independent consultant, IT auditor, and technical writer, editor and educator. He has more than 25 years' experience in business continuity, disaster recovery, security, enterprise risk management, telecom and IT auditing.








