Roman Milert - Fotolia
What are 5 hyper-converged backup best practices?
Compatibility, connection and cost are key considerations for hyper-converged data backup. Dive into these best practices to improve your data protection efforts.
Hyper-converged infrastructure appliances from vendors such as Dell EMC, Hewlett Packard Enterprise and Nutanix continue to perform well in the market, as do backup-oriented systems from vendors like Cohesity and Rubrik. Whichever type of HCI you use, backing up that data is mission critical.
One of the most important best practices for protecting an HCI system is to ensure the backup software is certified to be compatible with your platform. While general-purpose backup tools typically work with HCI deployments, it's best to go with an offering that is guaranteed to be fully compatible. Your HCI vendor may be able to recommend a hyper-converged backup product.
You should also verify that the hyper-converged backup product is compatible with workloads running on your HCI platform. This is especially important if you run mixed workloads, such as VMs and containers, within the same HCI deployment.
Consider how your backup system will physically connect to your HCI platform. Given the volume of data that can reside on an HCI system and the frequency with which you can modify that data, a high-speed data link is likely required. Check with your backup vendor to see which types of connectivity it supports, and then determine how best to provide high-speed connectivity between the backup server and the HCI deployment.
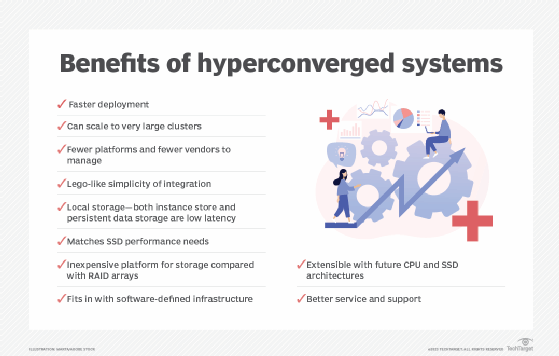
Hyper-converged backup best practices are different for vendors like Rubrik and Cohesity because these companies use HCI as a data protection platform. When using one of these platforms, keep your scalability requirements in mind. As your data grows, so will your data protection requirements. Both companies offer a cloud-based product, but if you use an HCI-based platform, physical capacity is a top concern. It is worth noting, however, that Cohesity has begun supporting unlimited scale-out through its C6000 high-density appliance.
Finally, consider the system's ability and cost to replicate backups to another data center or the cloud. Unless you replicate your backups, the backup system risks becoming a single point of failure in the event of a disaster such as a fire or flood.