Zero trust in the IT ops stack: Securing hybrid workloads
Zero trust replaces perimeter security with identity-based access, automation and continuous monitoring in hybrid and multi-cloud environments, boosting visibility and resilience.
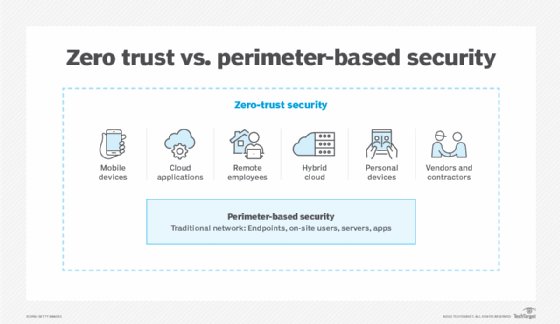
As hybrid and multi-cloud infrastructures expand the attack surface, modern IT environments are moving beyond legacy, perimeter-based security to distributed, identity-centric models. This shift is driving increased convergence between security and IT operations responsibilities.
Zero-trust operations embed continuous verification and enforcement of least privilege access into business-critical workflows. For executive leaders, zero trust delivers tangible value in several ways:
- Strengthening risk governance.
- Reducing the blast radius.
- Improving executive visibility.
- Modernizing legacy architecture.
- Improving resilience.
- Aligning security with digital transformation and agility.
- Enhancing auditability and compliance.
This article examines the role of zero-trust security in forward-looking enterprises. It includes an executive roadmap for directing this evolution.
Zero-trust security is not a product; rather, it's an essential operational model that is rapidly becoming a strategic imperative for enterprise security leadership. Before delving into the role of identity in zero trust, it's important to understand how traditional security approaches fail to address modern threats.
Identity as the foundation of zero-trust operations
Perimeter-based security establishes a clear network boundary and implements security controls within it. These controls assume that any entity within the environment could be trusted. Modern hybrid/remote workforces and evolving threat models render this approach obsolete.
Instead, identity is the new security control plane, handling users, services, applications, automation and workloads. Here are some core operational practices:
- Identity lifecycle management. Automate provisioning and deprovisioning, enforce multifactor authentication and regularly review access to prevent orphaned accounts and privilege creep.
- Least privilege access. Apply fine-grained role-based access control (RBAC) and attribute-based access control (ABAC) policies based on context, and continuously audit permissions across hybrid environments.
- Short-lived credentials and token-based access. Use ephemeral tokens and just-in-time access to minimize risk and eliminate standing privileges.
- Centralized visibility. Unify identity data across on-premises, cloud and SaaS to monitor access, detect anomalies and enforce consistent governance.
Managing nonhuman identities is crucial. Service accounts, APIs and workloads represent a growing risk area, increasing the attack surface area for many organizations.
Operationalizing zero trust requires centralized visibility and management across all environments -- on-premises, remote and cloud -- to drive risk mitigation and governance. Automation supports these efforts, particularly in complex hybrid infrastructures.
Automating security policies across hybrid infrastructures
Enforcing consistent control across on-premises, remote and cloud deployments remains complex. Successful operations teams will transition from manual controls to scalable, policy-driven automation.
The following are key best practices:
- Policy as code for version-controlled, auditable enforcement.
- Automated compliance and continuous validation.
- Infrastructure guardrails embedded in provisioning workflows.
- Integration with infrastructure as code (IaC) tools to enforce security at deployment.
The benefits? IT operations will experience less configuration drift, faster incident remediation and scalable governance. However, zero trust extends beyond infrastructure to include CI/CD pipelines.
Securing CI/CD and the modern IT delivery pipeline
One often-overlooked attack vector involves the CI/CD delivery pipeline. The software supply chain -- whether entirely in-house or in tandem with external partners -- represents a new and high-value attack target. Securing delivery pipelines is a prime example of using zero-trust security models.
The following are key controls to consider:
- Secrets management, including the use of vaults and dynamic secrets.
- Signed artifacts and provenance tracking.
- Restricted pipeline permissions and isolation.
- Runtime verification and deployed artifact monitoring beyond CI/CD pipelines.
Enforcing least privilege access for developers and automation tools is non-negotiable. Executives must ensure that third-party developers and partner organizations adhere to the same rigorous security requirements as internal teams.
Visibility and continuous verification
Zero-trust security models require continuous monitoring. Implementing a zero-trust infrastructure means significant changes to IT practices, tooling and configuration management. It can't be a one-time project with a single validation check.
All elements of the architecture require observability, including access identities, workloads and network activity. Integrate tools that detect anomalies in access patterns and behavior, alerting security staff and launching automated incident response activities.
Continuous process evaluation enables agility and growth. This evaluation requires feedback loops between monitoring systems and policy enforcement. Tools must provide the necessary telemetry to improve the organization's security posture over time and to measure progress.
Operational roadmap for IT leaders
Plan for incremental adoption versus an organization-wide transformation. A realistic strategy that prioritizes scalability and governance enables the greatest success.
Use the following roadmap to establish and maintain a zero-trust architecture:
- Step 1: Visibility. Inventory all identities -- human, service and machine -- then map workload access paths and identify overly permissive roles across hybrid environments.
- Step 2: Prioritize critical assets. Classify sensitive systems, data and pipelines to focus zero-trust efforts where risk is highest.
- Step 3: Enforce least privilege. Implement RBAC or ABAC, eliminate standing privileges and adopt short-lived credentials wherever possible.
- Step 4: Introduce policy automation. Use policy as code and integrate with IaC pipelines to enforce guardrails consistently at deployment and runtime.
- Step 5: Secure the delivery pipeline. Apply zero-trust controls to CI/CD, including secrets management, artifact signing and restricted execution environments.
- Step 6: Continuously monitor and adapt. Feed telemetry into detection systems, refine policies based on behavior and automate remediation where feasible.
- Step 7: Drive organizational alignment. Ensure security, IT operations and platform teams share ownership, metrics and tooling for sustained adoption.
Conclusion: From concept to operational discipline
Zero trust is no longer theoretical -- it's an operational discipline IT leaders must actively build into their environments. As hybrid and multi-cloud environments evolve, identity-driven, continuously verified access will define resilience.
Start small, automate relentlessly and integrate security into every workflow. Organizations that act now will be in the best position to adapt, scale and defend in an increasingly distributed and unpredictable threat landscape.
Damon Garn owns Cogspinner Coaction and provides freelance IT writing and editing services. He has written multiple CompTIA study guides, including the Linux+, Cloud Essentials+ and Server+ guides, and contributes extensively to Informa TechTarget, The New Stack and CompTIA Blogs.






