
maxkabakov - Fotolia
How to secure a home network for remote workforces
Remote workers rarely achieve the same network security at home that offices provide. Yet, with the right tools, remote workers can efficiently learn how to secure a home network.
Remote workforces can become risks to organizations that don't take data security seriously.
From a network perspective, remote workers can bolster their home networks in several ways to significantly mitigate the vast number of threats they might come up against. Let's first address why remote workers are currently more at risk than ever. We'll then explore how to secure a home network and ways to eliminate threats with the right network-based security tools and practices.
Why are remote workforces currently more at risk?
Data theft or data loss threats are on the rise, and criminals have shifted their attention to remote workers. The reasons for this shift are simple:
- The number of remote workers increased substantially in 2020 due to the global pandemic.
- Most network-based security tools deployed within corporate networks do not travel home with employees.
- Employees tend to ignore security policies more often when they work at home compared to when they work at the office. This includes inappropriate methods to share or transfer files, use of personal devices to perform work duties, and use of social media and other nonwork-related online activities while also performing work duties.
- Whatever security measures and tools the remote worker may have in place, the tools are likely not sufficient to protect sensitive corporate data.
Differences between enterprise and consumer network tools
Before employees consider different tools and procedures to better secure home networks for remote work, they must understand the difference between enterprise-grade networking hardware and software vs. consumer-grade alternatives.
Employees can purchase consumer-grade security products at big-box electronics stores or online websites, yet these tools provide limited levels of protection. These plug-and-play services are often easily compromised, not regularly updated to protect against the latest threats, and have limited alerting and logging capabilities.
Enterprise-grade hardware and software, on the other hand, offer far more granular levels of threat detection and remediation, provide detailed methods for altering when a breach happens, and can provide low-level details of when and how a breach occurred.
For most midsize to large businesses with relatively large numbers of remote workers, it makes sound business sense to provide each employee with the right level of enterprise-grade network hardware. This is especially true as data breaches constantly become more expensive. Organizations should deploy enterprise-grade security tools to significantly reduce risk of data theft and loss and enable rapid updates as new threats emerge.
How to secure a home network with the right tools
The following list shows examples of network security hardware and software remote workers should have when they work from home.
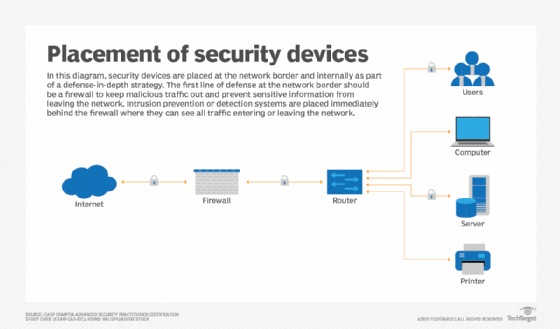
A combined Layer 7 firewall, intrusion prevention system and web security gateway appliance
This all-in-one appliance sits at the internet edge of the remote employee's home network and protects the network edge from external threats. In-house IT staff can centrally monitor and manage these appliances, which can quickly notify the staff when a potential breach occurs. Many network and security vendors offer remote worker gateways that provide all these features -- sometimes more -- in an easy-to-deploy appliance for a reasonable cost.
Software- or hardware-based VPN service
Whether an employee wants to deploy site-to-site VPNs to each remote site location -- using the firewall appliance mentioned previously -- or rely on a software-based remote access VPN, the results are the same. Employees get a fully encrypted and secure tunnel built between their home network and the corporate office.
A traditional VPN alternative is virtual desktop infrastructure (VDI), where the remote worker accesses a virtual PC to perform all work functions. While more expensive than VPNs, VDI adds additional layers of protection and keeps all data confined within a virtual desktop experience.
Enterprise mobility management (EMM)
For employees that wish to use their own PC or smart device to perform work duties, EMM software can scan the untrusted endpoint and determine whether it meets a predetermined level of acceptability from OS, application and security perspectives. If the device does not meet these levels, it cannot access the network until all issues are remediated.
Other security considerations
Finally, it's important to note that remote workers should consider other security products that aren't network-related. This includes malware prevention software and password keeper applications.
Additionally, if remote workers require Wi-Fi connectivity, they may choose to adopt wireless capabilities found more in secure corporate networks, as opposed to secure home networks. This includes the use of Wi-Fi Protected Access 2 enterprise authentication, which requires an individual username and password to access the wireless network, as opposed to a simple preshared key.








