
mangpor2004 - stock.adobe.com
How to secure your home Wi-Fi network in 7 steps
When securing your home Wi-Fi, update devices regularly, change passwords consistently, turn off unused services and inspect outdoor network equipment.
Over the last several years, home wireless networking has undergone quite the transformation. For example, hardware quality and security awareness in the consumer market have both improved. For anyone looking for a prosumer experience, cloud-managed home Wi-Fi -- similar to enterprise setups -- has also emerged as a possibility.
Wi-Fi security, in particular, has evolved. While the days of war driving and finding home networks open to exploit may be over, home Wi-Fi security could still go sideways in many places. For instance, the tools available to hackers have been commoditized as they're still seeking ways to bypass Wi-Fi security even if the days of default open networks are a distant memory.
If you're wondering how to secure your home Wi-Fi network -- given the latest Wi-Fi developments on all fronts -- follow these seven recommendations.
1. Update the ecosystem routinely
Recognize that all your network components form an interconnected system -- and so they need care and feeding. Wi-Fi routers, access points (APs), laptops, mobile devices, printers and anything else on the network should have their OSes kept up to date. Firmware, drivers and applications all develop security weaknesses over time. Keep them updated, especially for devices that may leave your network when you travel.
For those working from home, devices may come and go on your home Wi-Fi network. These devices can be conduits for problems if they aren't kept current. As a bonus, updating your devices can improve device performance and security. These updates can also take advantage of new wireless settings as they're released by the hardware vendor.
2. Use an obscure SSID
For home wireless networks, don't use your last name or any other easy monikers in your service set identifier (SSID). While people are naturally inclined to name devices and networks after themselves, no one should know which wireless LAN (WLAN) is yours. In other words, better to use "TheDogPound" rather than "MikeAndLauraSmith" to name your wireless network.
Putting your name out there might make you a target for nearby hackers if they fall within your signal footprint and decide to play games at your expense.
3. Use WPA2 encryption, minimally
Your encryption options on just about any wireless AP or router will include all or most of the following:
- Wired Equivalent Privacy (WEP), which is long obsolete;
- Wi-Fi Protected Access 1 (WPA1), also a relic;
- WPA2;
- WPA1/WPA2; or
- WPA2/WPA3.
WPA2 is still good and generally a safe bet. If you know you have WPA3-compatible clients, go for WPA2/WPA3 for backward compatibility and the latest encryption. If you have a WLAN client device that requires an obsolete security setting, better to replace that old device than to enable a security problem. Never use WEP or WPA1.
4. Change your Wi-Fi password on occasion
We all tend to allow visitors on our Wi-Fi networks from time to time. If you have children or roommates, it's easy for the Wi-Fi pre-share to get passed around to more people than should have it over time. Every six or 12 months, change your Wi-Fi password. If you have a large gathering at your house, make sure to change your WLAN password after the event.
5. Use strong passwords and disable unused services
It's easy to forget that Wi-Fi is just part of the rest of the network. Important devices on your home network -- like networked storage or media servers -- should have strong passwords as part of the overall home network security posture. Never use the Wi-Fi password for access to these resources.
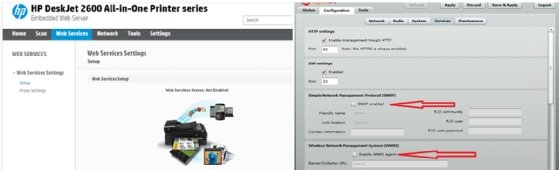
Also, note that many network devices come with a plethora of services enabled -- printers are often the worst in this regard. Services like Simple Network Management Protocol, Telnet, Server Message Block and several more are frequently enabled with weak default settings. If you don't use the service locally, turn it off.
6. Consider a guest SSID
Although using a single SSID on your residential Wi-Fi is easy, it may not be the best approach. Just as you don't give visitors access to your closets and drawers, they don't need full exposure to all your networked devices as you give them internet access.
Additionally, with the drastic rise in work-from-home policies because of the pandemic, more work is being done on the same networks we use for personal use.
Most home Wi-Fi routers provide an option for a separate guest SSID, thus enabling simple segmentation of your home WLAN into two isolated domains. Even if you don't have guests per se, you can use this feature to separate work and play devices.
7. Beware physical risks
Depending on your situation, you may have physical ports or cabling on your network that are exposed or easily accessed by outsiders. Maybe the cabling for an outside AP or camera is accessible from the ground. Aside from being targets of theft, these devices or their uplink wiring can be used for a range of intrusions. Check on them frequently to make sure no one has tampered with them.
It's easy to forget about network components on the outside of the house, but rogue access to your network can take many forms.
Inside, be mindful of where your Wi-Fi router and other important network devices are located. If you have many visitors, you don't want your equipment out in plain sight. You also don't want the cat swinging on patch cables or the dog biting into power cables. Finally, be mindful of how far your signal reaches beyond your walls.
What about MAC address filters?
Beyond these recommendations, you might be tempted to employ Media Access Control (MAC) address filtering to limit what devices can use your Wi-Fi and internet connection. This step is not recommended because more and more devices are using MAC address randomization built into the OS, and one of the first things any junior wireless hacker learns is how to spoof a MAC address to defeat these filters.








