
alphaspirit - Fotolia
6 remote workforce cybersecurity strategies for 2021
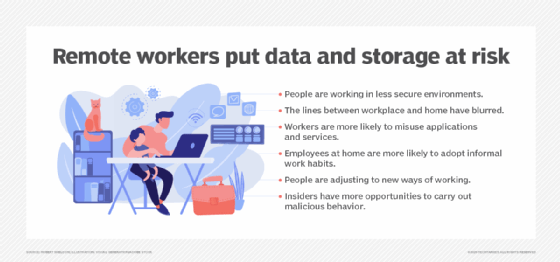
Remote worker data security has quickly evolved into a top concern for IT security. Here are six strategies to ensure remote workforce cybersecurity in 2021.
It's becoming increasingly likely that, in 2021, work-from-home policies will remain in place. The mad rush to ensure remote workers had the access to the resources they needed has ended; now, IT departments can refocus their attention on the best ways to secure those employees working out of the house. After all, remote worker data security is easily the biggest concern facing IT departments. Let's look at six strategic moves your organization can make to better secure remote workers in the coming year.
1. Improved password management and security
Ineffective or incomplete password management systems continued to plague businesses throughout 2020. A shift to remote work only amplified this issue. In 2021, serious effort should be put into improving password management. This should include a path for single sign-on (SSO) for every app and service the business uses. Combine SSO with multifactor authentication and a massive chunk of remote workforce cybersecurity risk will be immediately eliminated.
2. Increased infrastructure visibility
Data traffic visibility is becoming increasingly important as remote workers use business devices -- formerly secured by the corporate infrastructure -- on their internet connections. Tools such as network detection and response are a great way to regain that visibility. Being able to granularly track and plot network traffic between work-from-home (WFH) employee devices and company apps, data and services either in private data centers or public clouds can help identify traffic anomalies or configuration mistakes that lead to performance- or cybersecurity-related problems.
3. Deploy enterprise-grade teleworker security hardware
Most mid- to large-sized businesses already deploy plenty of network security tools to manage and control the endpoint devices that employees use. Next-gen firewalls, intrusion prevention systems, network-based malware tools and 802.1x authentication for Wi-Fi access are just a few examples. But, as more employees began working from home, IT security admins realized they were hobbled in their attempts to manage and control security policies once the devices were no longer protected by the corporate network. Teleworker gateways -- which extend corporate security features to employees' homes -- can help create a uniform security policy and help separate the home into business and nonbusiness networks. These appliances also build a secure VPN tunnel to remote resources. This eliminates the need for employees to install and continuously enable software-based remote VPN software.
4. Virtual desktops
Many businesses are moving away from deploying corporate laptops to remote workers and instead are relying on virtual desktops. While there are plenty of IT management, performance and cost-saving benefits of virtual desktop infrastructures, the biggest reason why businesses are moving to virtualized desktops is data loss prevention. Virtual desktops enable end users to launch a business OS that looks and operates as if it is local to the user. In reality, the desktop is being streamed from a secure private data center or, as is the case with desktop-as-a-service providers, from the public cloud. This keeps sensitive business data off remote desktops where it could either be accidently or purposefully leaked.
5. Zero trust
For IT security, 2021's biggest buzzword will likely be zero trust. However, unlike many other formerly hot trends, zero trust is actually a legitimate and ideal security framework for workers and digital resources that reside both inside and outside the boundaries of the corporate infrastructure. Consider these principles of zero trust to determine where you're at with your security infrastructure and where you need to go to achieve its impressive security benefits.
6. WFH security training and materials
The new year is a great time to get rid of bad habits. There is no better time to create or rework existing security training and associated materials. The goal here should be to acquaint employees with some common cybersecurity mistakes and misperceptions that often occur when working remotely. These include topics like the handling of passwords, securing corporate hardware, using authorized collaboration apps, storing sensitive data, avoiding the risks of shadow IT and verifying -- safely -- the identity of people with whom employees are collaborating.







