cyber espionage
What is cyber espionage?
Cyber espionage (cyberespionage) is a type of cyber attack that malicious hackers carry out against a business or government entity. The goal of cyber espionage, also referred to as cyber spying, is to provide attackers with information that gives them advantages over rival companies or governments.
In the media, cyber espionage often refers to advanced persistent threats (APTs) that one nation-state launches against another for political gain. When the attacker's motives are financial as well as political, the cyber attack qualifies as economic espionage.
Bad actors who engage in cyber espionage typically want to remain in IT environments, undetected, for long periods of time. This means this type of attack is often quite complicated and expensive to carry out.
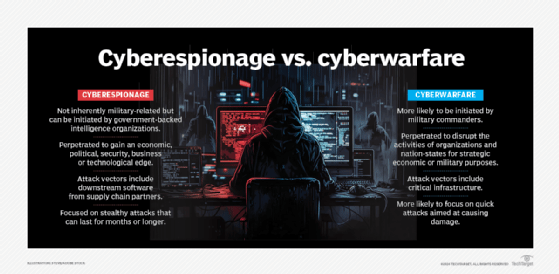
What is the difference between cyber espionage and cyberwarfare?
The terms cyber espionage and cyberwarfare are similar, but they are not the same. The biggest difference is that the primary goal of a cyberwarfare attack is to disrupt the activities of a nation-state, while the primary goal of a cyber espionage attack is for the attacker to remain hidden for as long as possible in order to gather maximum intelligence.
Even though cyber espionage and cyberwarfare are two distinct concepts, they are often used together. For example, cyber espionage can be used to build intelligence that will help a nation-state prepare for a physical or cyberwar.
What are cyber espionage targets?
Any government or large corporation can be the target of a cyber espionage attack. Some of the most commonly targets include the United States, South Korea, Japan, Russia, China and the United Kingdom. According to the U.S. Department of Homeland Security, some of the nations that are best prepared to deal with cyber attacks include -- but are not limited to -- Canada, the United States, Brazil and Germany.
What are cyber espionage tactics?
Cyber espionage tactics are varied. They include, but are not limited to the following:
- Exploiting vulnerabilities in websites or browsers.
- Spear phishing emails designed to escalate the attacker's network privileges.
- Supply chain attacks that target the primary target's partners.
- Malware, Trojans and worms.
- Infecting updates for commonly used third-party software applications.
How can you prevent cyber espionage and protect data?
Although not every company is at high risk of becoming a target of nation-state hackers, individuals in rival companies may also commit cyber espionage. To protect its data and prevent cyber espionage of any kind, an organization can do the following.
- Identify the techniques used in cyber espionage attacks. This can give an organization a good baseline understanding of what to protect.
- Monitor systems for unexpected behaviors. Security monitoring tools can help flag any suspicious activity for further investigation.
- Ensure critical infrastructure has sufficient security controls.
- Enact data security policies, including access control.
- Patch known vulnerabilities.
- Vet the security of any third-party software systems.
- Create a cybersecurity policy that addresses security procedures and risks.
- Establish an incident response plan.
- Educate employees about security policies, including how to avoid opening suspicious-looking emails with links or document attachments.
- Implement a password management policy that mandates users regularly change their passwords.
- Monitor what data users can store on mobile devices, especially in bring your own device (BYOD) environments.
Examples of cyber espionage attacks
In 2020, U.S. organizations and government agencies were the targets of a nation-state attack. Security researchers discovered a backdoor in a popular IT management product from SolarWinds.
FireEye, one of SolarWinds' 300,000 customers, disclosed that the nation-state attack it suffered was the result of a massive supply chain attack on SolarWinds. Attackers gained access to victims through infected updates to SolarWind's Orion IT monitoring and management software. Up to 18,000 SolarWinds customers were vulnerable, including various U.S. government agencies. Multiple media outlets reported APT29, a Russian state-sponsored hacking group also known as Cozy Bear, was behind the SolarWinds attack.
Previously, Cozy Bear attacked the Norwegian Police Security Service in 2017 by attempting to spear phish the emails of nine users, across the Ministry of Defense, the Ministry of Foreign Affairs and the Labor Party.
Cozy Bear and another group, Fancy Bear, made multiple attempts to hack into Dutch ministries and the Ministry of General Affairs that same year. The attackers tried to obtain sensitive information concerning government documents.
North Korea has also been involved in a number of cyber espionage attacks targeting countries such as South Korea, Japan and Vietnam.
North Korea was responsible for a state-sponsored hack of Sony Pictures in 2014. The Sony hack was conducted using malware and a Server Message Block worm tool. U.S. investigators believe the perpetrators of this economic espionage took two months to copy critical files and targeted Sony as a trial-run for future political cyber espionage.





