cyberwarfare
What is cyberwarfare?
The generally accepted definition of cyberwarfare is a series of cyber attacks against a nation-state, causing it significant harm. This harm could include disruption of vital computer systems up to the loss of life.
There has been some debate among experts regarding what acts specifically qualify as cyberwarfare. While the United States Department of Defense (DOD) states the use of computers and the internet to conduct warfare in cyberspace is a threat to national security, why certain activities qualify as warfare, while others are limited to the label of simply cybercrime, is left unclear.
Generally accepted parameters, however, include the idea that cyberwarfare seeks to further the goals of one nation-state over another nation-state. Cyberwarfare carries the potential to cause damage to government and civilian infrastructure, which could disrupt critical systems that result in damage to the nation or loss of life.
Although cyberwarfare generally refers to cyber attacks perpetrated by one nation-state on another, it can also describe attacks by terrorist groups or hacker groups aimed at furthering the goals of a nation.
Cyberwarfare could, for example, be the use of a virus or distributed denial-of-service (DDoS) attack to damage or infiltrate another nation's information network.
What are the goals of cyberwarfare?
According to the Cybersecurity and Infrastructure Security Agency, the goal of cyberwarfare is to "weaken, disrupt or destroy" another nation. To achieve their goals, cyberwarfare programs target a wide spectrum of objectives that can harm national interests. These threats range from propaganda to espionage and extensive infrastructure disruption and loss of life to citizens.
Other potential motivations behind cyberwarfare include civil and income motivations. Threat actors may have a goal to affect civil infrastructure by targeting internet service providers, telecommunication systems, network equipment, electrical grids or financial networks.
Nation-state actors may also be motivated by income, where income is generated by using techniques like ransomware attacks against another nation -- targeted at its critical infrastructure, for example.
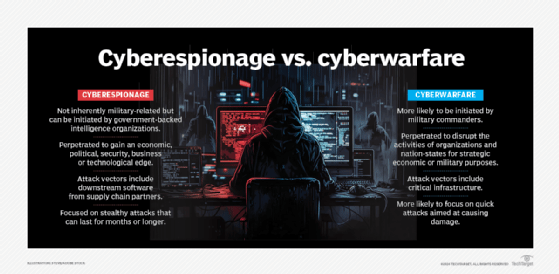
Cyberwarfare is also similar to cyber espionage (cyber spying), with the two terms oftentimes being conflated. The biggest difference is the primary goal of a cyberwarfare attack is to disrupt the activities of a nation-state, while the primary goal of a cyber espionage attack is for the attacker to remain hidden for as long as possible in order to gather intelligence.
The two activities are distinct concepts but are also often used together, as gaining additional intelligence could be another motivation in cyberwarfare. Cyber espionage can also be used to build intelligence that helps a nation-state prepare for declaring a physical or cyber war.
What are the types of cyberwarfare attacks?
The threat of cyberwarfare attacks grows as a nation's critical systems are increasingly connected to the internet. Even if these systems can be properly secured, they can still be hacked by perpetrators recruited by nation-states to find weaknesses and exploit them. Major types of cyberwarfare attacks include the following.
Data theft
Cybercriminals hack computer systems to steal sensitive information that can be used for intelligence, held for ransom, sold, used to incite scandals and chaos, or destroyed.
Destabilization
Cybercriminals also attack governments through critical infrastructure, like transportation systems, banking systems, power grids, water supplies, dams and hospitals. The adoption of the internet of things makes the manufacturing industry increasingly susceptible to outside threats.
From a national security perspective, destabilizing critical digital infrastructure inflicts damage on vital modern services or processes. For example, an attack on the energy grid could have massive consequences for the industrial, commercial and private sectors.
Economic disruption
Nation-state attackers can target the computer networks of banks, payment systems and stock markets to steal money or block others from accessing their funds.
Propaganda attack
This type of attack targets the thoughts of people in another nation-state. Propaganda is used to spread lies and expose truths, with the goal of making citizens in a targeted nation-state lose trust in their side or country.
Sabotage
Cyber attacks that sabotage government computer systems can be used to support conventional warfare efforts. Such attacks can block official government communications, contaminate digital systems, enable the theft of vital intelligence and threaten national security.
State-sponsored or military-sponsored attacks, for example, may target military databases to get information on troop locations, weapons and equipment being used.
The Center for Strategic and International Studies (CSIS) maintains a timeline record of cyber attacks on government agencies, defense and high-tech companies, and economic crimes with losses of more than $1 million. In CSIS timelines dating back to 2006, many of the recorded cyber incidents involve hacking and data theft from nation-states.
How cyberwarfare attacks are perpetrated
How each attack is accomplished may change depending on the target, purpose and type of attack. Examples of attack methods include the following:
- Viruses, phishing, computer worms and malware that can take down critical infrastructure.
- DDoS attacks that prevent legitimate users from accessing targeted computer networks or devices.
- Hacking and theft of critical data from institutions, governments and businesses.
- Spyware or cyber espionage that results in the theft of information that compromises national security and stability.
- Ransomware that holds control systems or data hostage.
- Propaganda or disinformation campaigns used to cause serious disruption or chaos.
Historical examples of cyberwarfare attacks
There are many examples of cyberwarfare attacks, including the following.
Bronze Soldier -- 2007
In 2007, the Estonian government moved the Bronze Soldier, a painful symbol of Soviet oppression, from the center of Tallinn, the capital of Estonia, to a military cemetery on the outskirts of the city.
In the following months, Estonia was hit by several major cyber attacks. This resulted in many Estonian banks, media outlets and government sites being taken offline due to unprecedented levels of traffic.
The Stuxnet worm -- 2010
The Stuxnet worm was used to attack Iran's nuclear program in what is considered one of the most sophisticated malware attacks in history. The malware targeted Iranian supervisory control and data acquisition systems and was spread with infected USB devices.
DDoS attack in Ukraine -- 2014
The Russian government allegedly perpetrated a DDoS attack that disrupted the internet in Ukraine, enabling pro-Russian rebels to take control of Crimea.
Sony Pictures -- 2014
Hackers associated with the government of North Korea were blamed for a cyber attack on Sony Pictures after Sony released the film The Interview, which portrayed the North Korean leader Kim Jong Un in a negative light.
The Federal Bureau of Investigation found that the malware used in the attack had data that included encryption algorithms, data deletion methods and compromised networks that were similar to malware previously used by North Korean hackers.
The U.S. Office of Personnel Management -- 2015
Cybercriminals backed by the Chinese state were accused of breaching the website of the U.S. Office of Personnel Management and stealing the data of approximately 22 million current and former government employees.
The U.S. presidential election -- 2016
The "Report on the Investigation into Russian Interference in the 2016 Presidential Election" by special counsel Robert Mueller determined that Russia engaged in informational warfare to interfere with the U.S. presidential election.
The Mueller Report found that Russia used social media accounts and interest groups to disrupt the political climate in the U.S., using what it called "information warfare." The operation began with discrediting the electoral system in 2014 and escalated to more explicit activities designed to benefit candidate Donald Trump in the 2016 election, according to the report.
China's Ministry of State Security -- 2018
In 2018, the U.S. Department of Justice charged two Chinese hackers associated with the Chinese government's Ministry of State Security with targeting intellectual property and confidential business information.
Iranian weapons systems -- 2019
In June 2019, the United States launched a cyber attack against Iranian weapons systems that disabled the computer systems associated with controlling rocket and missile launchers. This was done in retaliation after the shooting down of a U.S. drone.
Ukraine and Russia -- 2022
Ukraine saw a large increase in cyber attacks during Russia's invasion of Ukraine. Well-known groups, such as APT29 and APT28, for example, have been among the nation-state groups performing cyberwarfare attacks. These attacks include malware, data wipers, DDoS attacks and other attacks meant to target critical industrial infrastructure, data networks, and public and private sector organizations, as well as banks. The aim of the attacks has also changed over the course of the war, from disruption and destruction of critical infrastructure to information and intelligence gathering.
Combating cyberwarfare
Since 2010, the Cooperative Cyber Defence Centre of Excellence, part of the North Atlantic Treaty Organization, has conducted annual war games to increase preparedness and evaluate countermeasures to defend nations against cyber attacks.
On Aug. 2, 2017, President Donald Trump signed into law the Countering America's Adversaries Through Sanctions Act (Public Law 115-44). This law imposed new sanctions on Iran, Russia and North Korea to help prevent acts of cyberwarfare and strengthen the U.S. information security program.
The National Defense Authorization Act for 2021 included 77 cybersecurity provisions, among other appropriations and policies for DOD programs and activities. It is considered a significant piece of cybersecurity legislation.
Learn more about 13 different types of cyber attacks and the security strategies needed to defend against them.







